This post has been republished via RSS; it originally appeared at: Windows IT Pro Blog articles.
Traditionally, the desktop management scenario for most enterprises has been one where all users and devices are located on-site with a direct network connection. That’s been the state of things for years.
But the workplace is changing. More of your users work remotely full-time; some never set foot in your physical facilities. If you do the initial setup for a Windows 10 device on-premises, you start out in control. But if those devices are distributed to your remote workforce, how do you maintain control? How do you make sure user devices are secure and up-to-date while keeping the update process simple and hassle-free?
In short, you implement a modern desktop management strategy.
Extending your directory to the cloud
You can modernize your desktop management processes by extending your local directory to the cloud using Microsoft Azure Active Directory (Azure AD). By connecting remote and on-premises devices—even personally owned devices — to Azure AD you can protect your remote users and their devices much as you would on-premises. In fact, you can use both Azure AD and your on-premises AD together to create a hybrid solution.
This post is designed to provide you with a quick look at the steps you need to take to integrate your on-premises directory with Azure AD. It’s a straightforward process:
- Create your Azure AD tenant, including verifying your custom domain and adding branding.
- Prepare your on-premises directory.
Create your Azure Active Directory tenant
If you’re already using Microsoft Azure to host virtual machines (VMs), to store backups, for Azure SQL databases, or if you are already using Office 365, you already have an Azure AD tenant.
There are four main editions of Azure AD:
- Free
- Basic
- Premium P1
- Premium P2
If you don’t already have Azure AD, go to the Azure Active Directory page to learn about these editions and sign up for a trial.
You can try Azure AD Premium P1 for free if you would like to follow along with the rest of these instructions. Azure AD Premium is also included as part of Microsoft 365, an all-in-one modern desktop solution.
Create a new tenant
The first thing you’ll need to do is create a new tenant in your organization’s Azure Portal. Once you’ve done that, continue to follow the steps below.
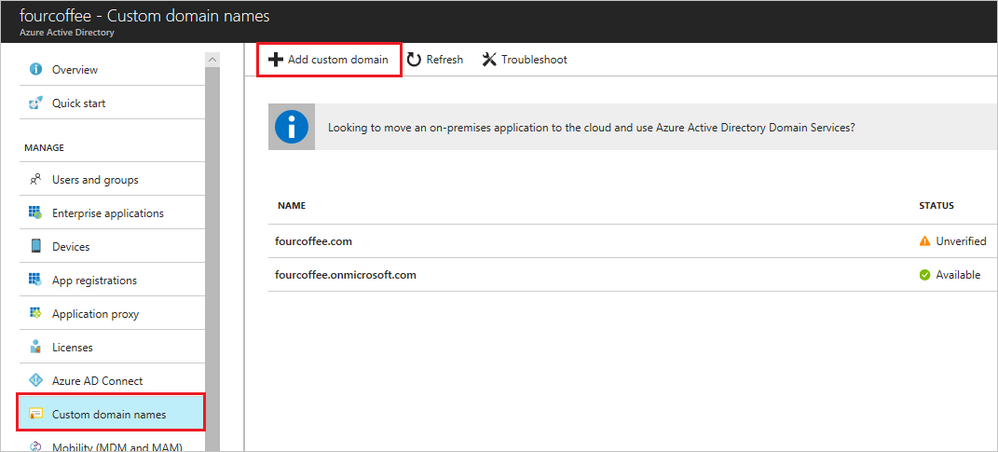
Add a custom domain name
Each Azure AD tenant comes with a default domain name that looks like tenantname.onmicrosoft.com. You can’t change that name, which you probably don’t want to use in real life, so you’ll want to connect your own custom domain name. Just sign in to the Azure Active Directory admin center and select Custom domain names from the menu. Then select Add custom domain and follow the instructions.
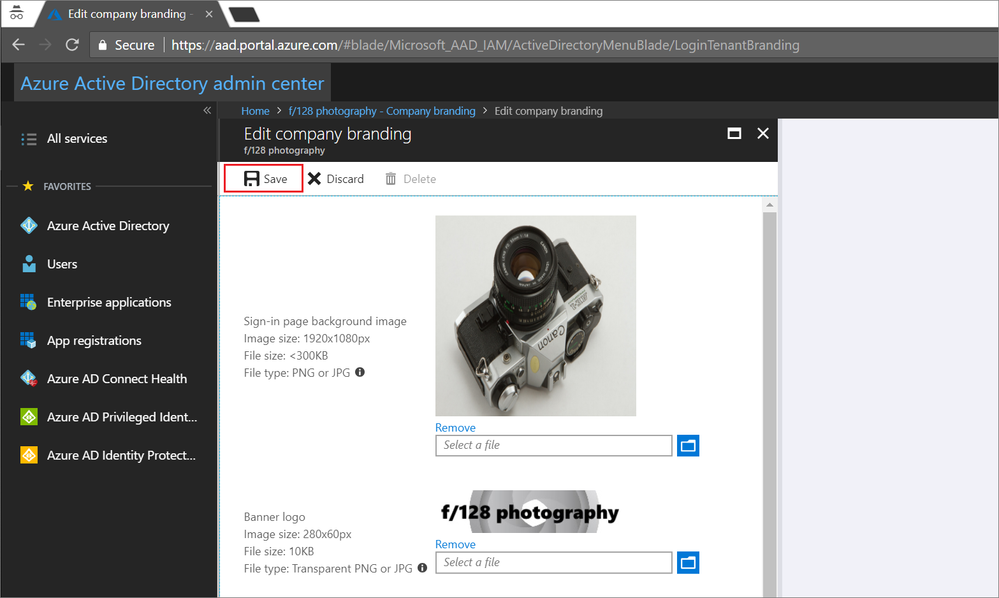
Add your company branding
To help you and your users know that they’re signing into the correct tenant, it’s a good idea to add your company branding. This will modify the sign-in page for any web applications that depend on Azure AD, such as Office 365. That way you can tell your users to look for your branding as potential way to identify phishing campaigns trying to steal credentials. In the Azure AD admin center, select Company branding from the menu, then select Edit to customize your branding. For more details, visit How to: Add branding to your Azure Active Directory sign-in page.
Prepare your on-premises directory
You’ll also need to make sure your on-premises directory is ready for synchronization with Azure AD. For example, if you subscribe to Office 365, you will want to run IdFix to identify any problematic user accounts that might not synchronize successfully (typically duplicates or with IDs that have formatting problems). You’ll also want to make sure that your directory meets the following requirements:
- AD schema version and forest functional level are Windows Server 2003 or later.
- Your Domain Controllers (DCs) are running Windows Server 2008 or later, with latest service pack.
- Your DC must be writable.
- Your on-premises domain can’t use dotted NetBios names (like domainname.local).
- The server you install Azure AD Connect on must be running Windows Server Standard or better and must have a full graphical user interface (GUI) installed. This means no Small Business Server, Windows Server Essentials, or server core.
- The Azure AD Connect server must be running Windows Server 2008 or later with latest hotfixes.
- Password synchronization requires Windows Server 2008 R2 SP1 or later.
- Using group managed service accounts requires Windows Server 2012 or later.
- If you want to deploy Active Directory Federation Services (ADFS), there are additional requirements like Secure Sockets Layer (SSL) certificates, configuring name resolution, and more. For more details, visit Prerequisites for Azure AD connect.
Download and install Azure AD Connect
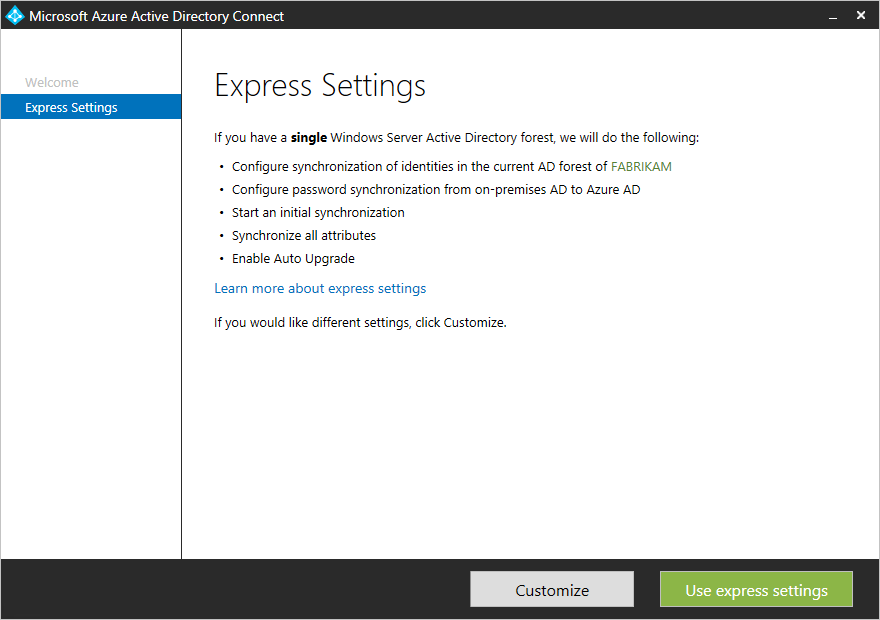
Downloading and installing Azure AD Connect is probably the simplest part of the process.
Even if you eventually want to enable more advanced features, starting with the express settings enabled is a great way to take advantage of essential capabilities right away. You can always run the wizard again later to enable more advanced features and you can find guidance here for deploying Azure AD in more complex environments.
- Download the latest version of Azure AD Connect to the server you want to install it on.
- Find and double-click AzureADConnect.msi.
- Choose Use express settings and follow the steps in the wizard.
Registering devices
Of course, having Azure AD synchronizing with your on-premises AD doesn’t get those remote devices under control all by itself. You need to get those devices registered with Azure AD.
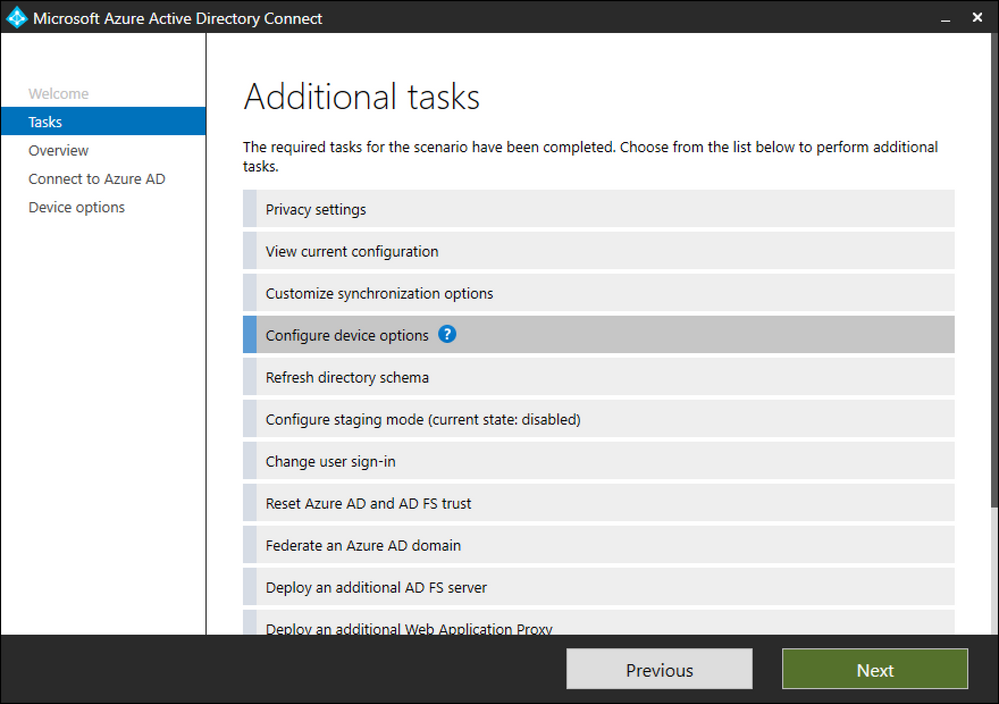
The devices joined to your on-premises domain can also be joined to your Azure AD domain (called hybrid Azure AD join). You can configure hybrid Azure AD join through Azure AD Connect.
Just sign into Azure AD Connect, select Configure, and then on the Additional tasks page select Configure device options. After that, follow the instructions in the wizard, selecting Configure Hybrid Azure AD join and the appropriate domain when prompted.
You’ll also need to push a policy to your devices that add the following URLs to the Local Intranet zone in Internet Explorer:
Additionally, you’ll have to enable Allow updates to status bar via script in their local intranet zone. For more details see How to manage devices using the Azure portal.
Take control
Once you’ve got devices registered with Azure AD, you’re ready to take more control. You can implement conditional access to resources based on the state or location of your users’ desktops, along with your users’ group membership. You’ll also have insight into what cloud apps they use with Cloud App Discovery, plus greater ability to manage Windows 10 features such as Windows Hello for Business and BitLocker.
Modern is simpler
Azure Active Directory is just one example of how managing a modern desktop is simpler with Microsoft 365. Along with Azure Active Directory Premium, Microsoft 365 also includes Intune for mobile device and app management as part of Enterprise Mobility + Security (EMS), Office 365 ProPlus, and Windows 10.
For more information about the advantages of modern desktop management, download the e-book Modern management with Windows 10: What’s in it for IT?
Continue the conversation. Find best practices. Bookmark the Windows 10 Tech Community.
Looking for support? Visit the Windows 10 IT pro forums.