This post has been republished via RSS; it originally appeared at: Ask the Directory Services Team articles.
First published on TechNet on Aug 14, 2013Hi everyone, David here with a quick announcement.
Yesterday, MSRC announced a timeframe for deprecation of built-in support for certificates that use the MD5 signature hash. You can find more information here:
Along with this announcement, we've released a framework which allows enterprises to test their environment for certificates that might be blocked as part of the upcoming changes ( Microsoft Security Advisory 2862966 ) . This framework also allows future deprecation of other weak cryptographic algorithm to be streamlined and managed via registry updates (pushed via Windows Update).
Some Technical Specifics:
This change affects certificates that are used for the following:
- server authentication
- code signing
- time stamping
- Other certificate usages that used MD5 signature hash algorithm will NOT be blocked.
For code signing certificates, we will allow signed binaries that were signed before March 2009 to continue to work, even if the signing cert used MD5 signature hash algorithm.
Note: Only certificates issued under a root CA in the Microsoft Root Certificate program are affected by this change. Enterprise issued certificates are not affected (but should still be updated).
What this means for you:
1) If you're using certificates that have an MD5 signature hash (for example, if you have older web server certificates that used this hashing algorithm), you will need to update those certificates as soon as possible. The update is planned to release in February 2014; make sure anything you have that is internet facing has been updated by then.
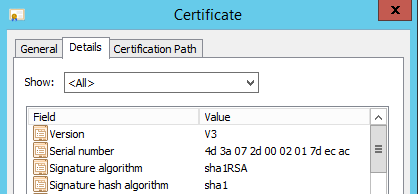
You can find out what signature hash was used on a certificate by simply pulling up the details of that certificate's public key on any Windows 8 or Windows Server 2012 machine. Look for the signature hash algorithm that was used. (The certificate in my screenshot uses sha1, but you will see md5 listed on certificates that use it).
If you are on Server Core or have an older OS, you can see the signature hash algorithm by using certutil -v against the certificate.
2) Start double-checking your internal applications and certificates to insure that you don't have something older that's using an MD5 hash. If you find one, update it (or contact the vendor to have it updated).
3) Deploy KB 2862966 in your test and QA environments and use it to test for weaker hashes (You are using test and QA environments for your major applications, right?). The update allows you to implement logging to see what would be affected by restricting a hash. It's designed to allow you to get ahead of the curve and find the potential weak spots in your environment.
Sometimes security announcements like this can seem a little like overkill, but remember that your certificates are only as strong as the hashing algorithm used to generate the private key. As computing power increases, older hashing algorithms become easier for attackers to crack, allowing them to more easily fool computers and applications into allowing them access or executing code. We don't release updates like this lightly, so make sure you take the time to inspect your environments and fix the weak links, before some attacker out there tries to use them against you.
--David "Security is everyone's business" Beach
