This post has been republished via RSS; it originally appeared at: IIS Support Blog articles.
TL;DR: When creating an app registrations for a bot, make sure the app ID is created for a multi-tenant access (see below screen capture); the resulting manifest has to specify signInAudience = AzureADandPersonalMicrosoftAccount.
In many organizations, regular users are not allowed to create app registrations in Azure AD; this is a privilege reserved to tenant administrators.
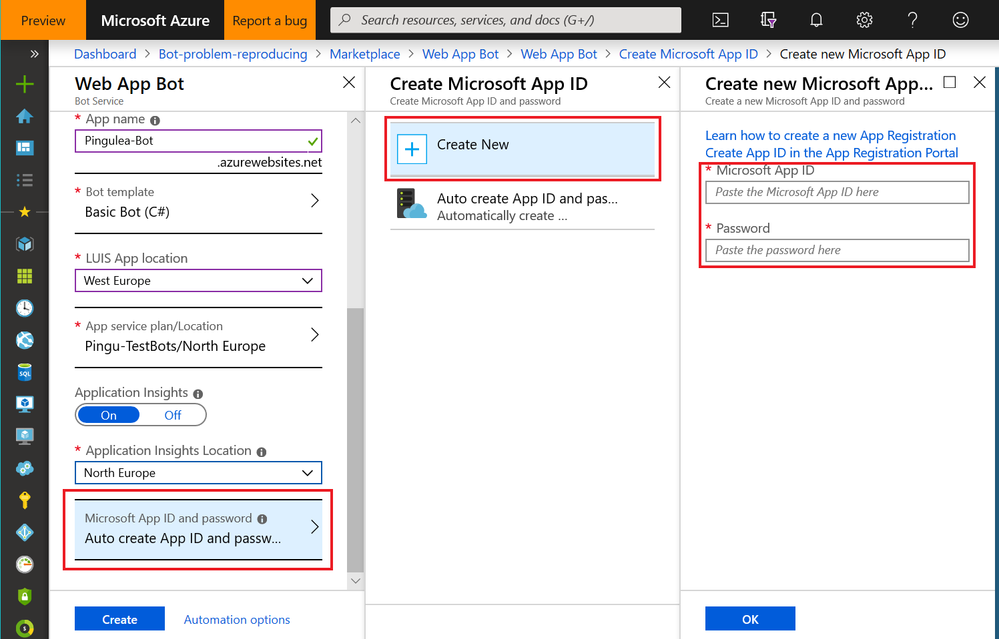
And so, when creating a bot – either with Web App Bot template, or with the Bot Channel Registration – the developers need to specify a pre-defined pair of Application ID with its Password (Secret). Like below:
But then, in many cases, the newly created bot does not work. It does not reply. Event when the bot is created with the standard bot template code which should work out-of-the-box.
After banging the head in the keyboard and enabling Application Insights for the bot application, we may see that there are exceptions generated by dependency calls ending in 401 response status code – Unauthorized. Of course, checking the App ID and Password handed by the tenant admin does not reveal anything wrong – they match. Then why?
In many cases, I found, it is because of the application registration performed by the tenant admins. How? Well, I applied the troubleshooting guidance from the article below, but using Postman instead of curl.
https://docs.microsoft.com/en-us/azure/bot-service/bot-service-troubleshoot-authentication-problems#step-2
In the illustration below, client_id is filled with App ID, and the client_secret gets the password.
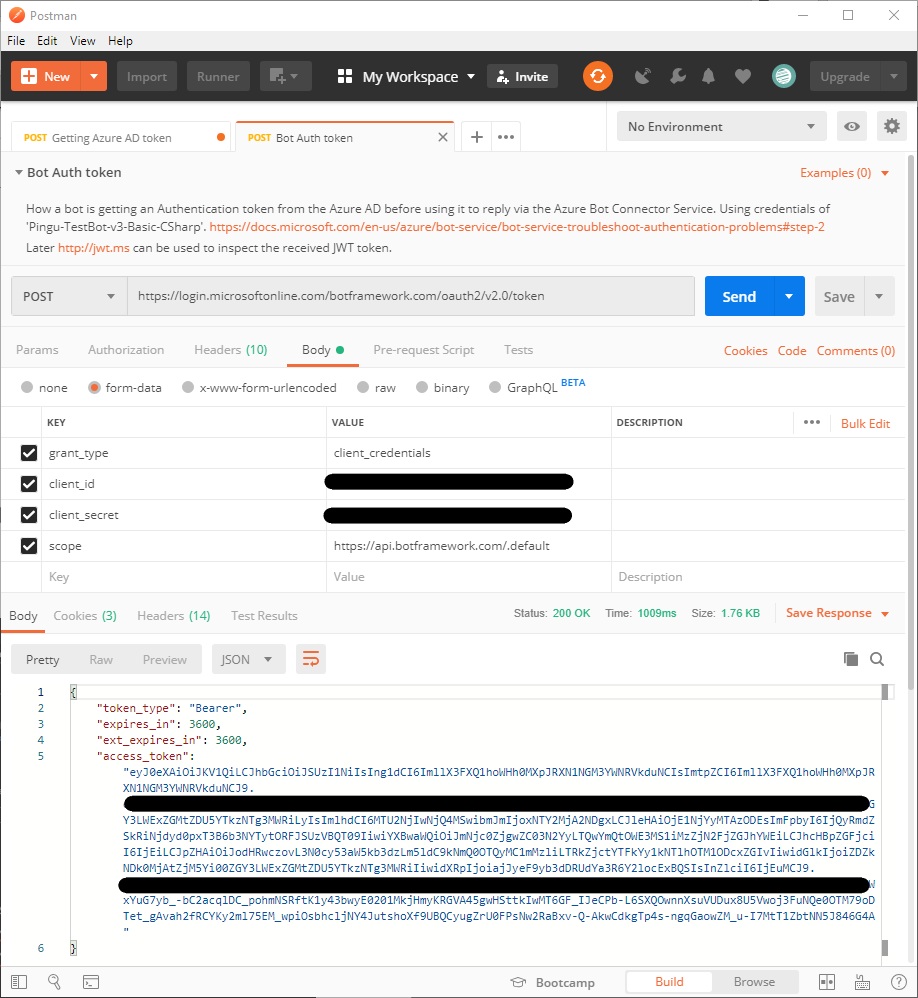
With a properly set app registration, the Azure AD tenant of botframework.com should be able to issue the ticket, like illustrated above. And the ticket could be further inspected using a site like http://jwt.ms.
However, if the response from Azure AD is an authorization error like below, look no further. There is something wrong with the app registration.
{
"error": "unauthorized_client",
"error_description": "AADSTS700016: Application with identifier 'NNNNNNNN-NNNN-NNNN-NNNN-NNNNNNNNNNNN' was not found in the directory 'botframework.com'. This can happen if the application has not been installed by the administrator of the tenant or consented to by any user in the tenant. You may have sent your authentication request to the wrong tenant.\r\nTrace ID: TTTTTTTT-TTTT-TTTT-TTTT-TTTTTTTTTTTT\r\nCorrelation ID: CCCCCCCC-CCCC-CCCC-CCCC-CCCCCCCCCCCC\r\nTimestamp: 2019-08-19 11:21:28Z",
"error_codes": [ 700016 ],
"timestamp": "2019-08-19 11:21:28Z",
"trace_id": "TTTTTTTT-TTTT-TTTT-TTTT-TTTTTTTTTTTT",
"correlation_id": "CCCCCCCC-CCCC-CCCC-CCCC-CCCCCCCCCCCC",
"error_uri": "https://login.microsoftonline.com/error?code=700016"
}
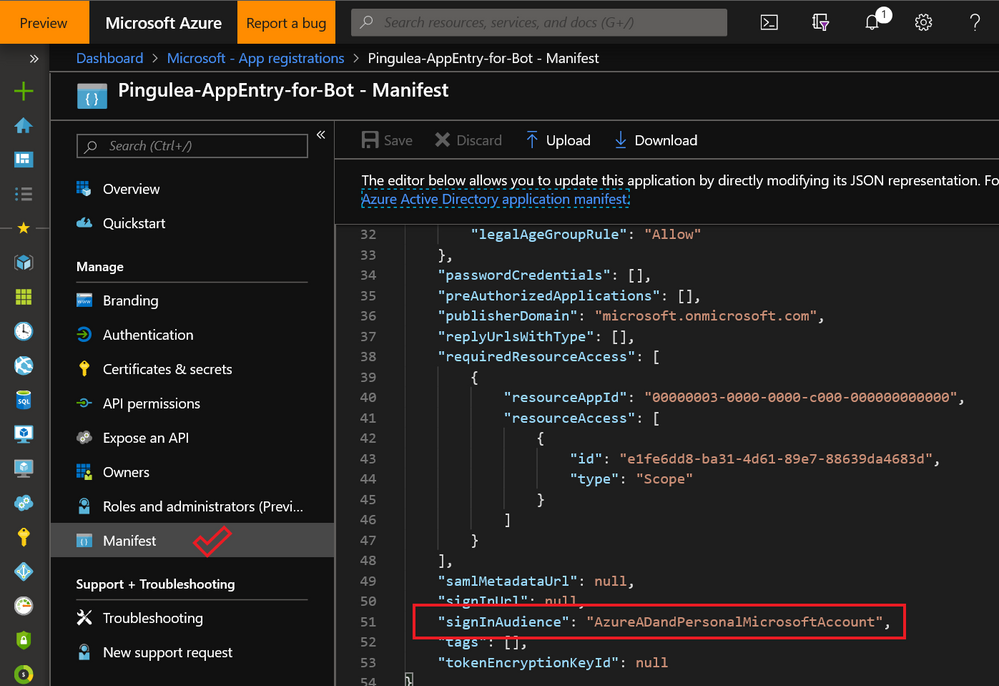
One simply has to check the manifest of the app registration. The manifest has to specify signInAudience = AzureADandPersonalMicrosoftAccount, as illustrated below.
Note: Sometimes editing the manifest is the only option available, if the bot already exists; because once a bot was created with an App ID (app registration), that cannot be changed.
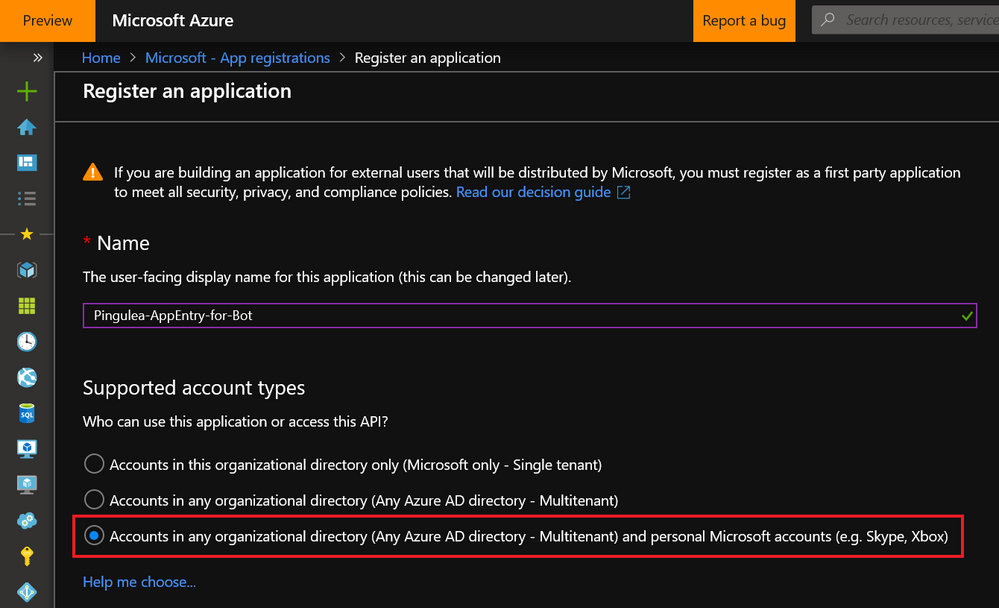
To make sure that an Azure AD app registration would work fine for a bot solution, admin tenant should check the third option in the Supported account types: Accounts in any organizational directory (Any Azure AD directory - Multitenant) and personal Microsoft accounts (e.g. Skype, Xbox).
Send them this illustration below when you’re asking for a new app registration for a bot.
All the best of luck!

God bless you
per https://docs.microsoft.com/en-us/azure/bot-service/bot-service-quickstart-registration#manual-app-registration AzureADMultipleOrgs is also valid