This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
EDR capabilities in Microsoft Defender ATP for Mac now available for preview
At Microsoft, we’re committed to building security solutions not just for Microsoft but also from Microsoft. We know that customers have complex and heterogenous environments running multiple applications, multiple clouds, and multiple platforms. Today, the Microsoft Defender ATP team is proud to announce the public preview availability of endpoint detection and response (EDR) capabilities on macOS devices.
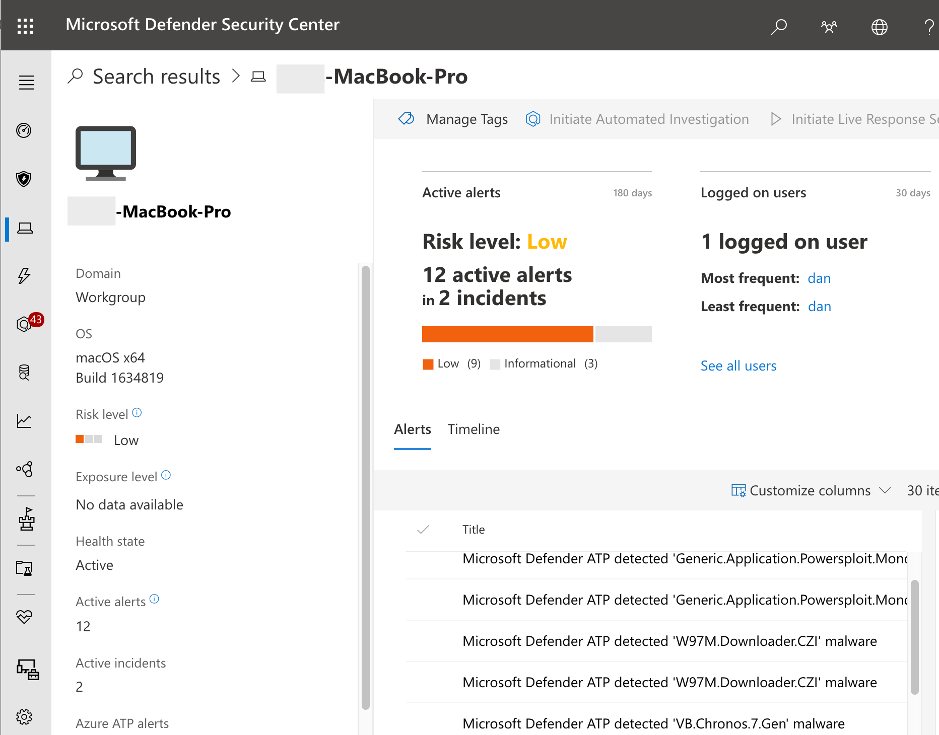
Microsoft Defender ATP for Mac currently includes preventive antivirus capabilities and reporting via Microsoft Defender Security Center. With the new EDR capabilities, Microsoft Defender ATP customers will have the ability to detect advanced attacks that involve macOS devices, utilize rich investigation experiences, and quickly remediate threats.
We’ve been working closely with design partners and several customers on this post-breach component of the platform in private preview. Today, we invite you to experience the new capability, with these benefits:
- Rich investigation experience – including machine timeline, process creation, file creation, network connections and, of course, the popular Advanced Hunting.
- Optimized performance – enhanced CPU utilization in compilation procedures and large software deployments.
- In-context AV detections – just like with Windows, get insight into where a threat came from and how the malicious process or activity was created.
If you’re already running Microsoft Defender ATP for Mac, we recommend that you configure some of your macOS machines to Insider Mode and try the suggested simple scenario below. If this is the first time you deploy Microsoft Defender ATP for Mac, learn how to install and configure, and then enable the Insider Mode.
Experience Microsoft Defender ATP for Mac EDR with simulated attack
The following steps simulate a detection scenario on a macOs machine. Follow the steps, try to investigate the case, and give us feedback.
- Verify that the onboarded macOS machine appears in Microsoft Defender Security Center. If this is the first onboarding of the machine, it can take up to 20 minutes until it appears.
- Download and extract the file from here (filename: MDATP MacOS DIY.zip) to an onboarded macOS machine. Note: If the device is running macOS Catalina and was onboarded manually, you may need to take a few more steps. In macOS Catalina you must explicitly allow full disk access to monitor built-in directories. To enable access, follow instructions here.
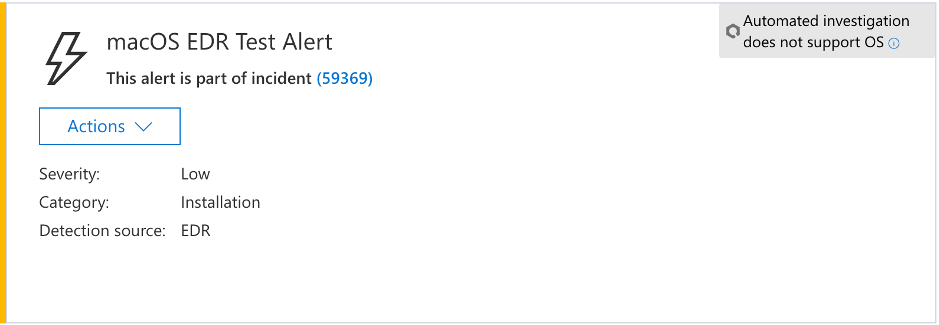
- After a few minutes, the following alert should be raised in Microsoft Defender Security Center.
- Look at the alert details, machine timeline, and perform the regular investigation steps.
Note: A prerequisite for this scenario in macOS Catalina is to enable full disk access. Learn how to do it here.
Performance
We have optimized CPU utilization in compilation procedures and large software deployments, and we invite customers to give us feedback on performance. Please refer to the Performance measurement documentation [PDF] for more details.
Help us innovate Microsoft Defender ATP for Mac
We are extremely excited to deliver this new milestone today. We value customer feedback. Join us as we continue to enhance Microsoft Defender ATP for Mac. Try out the EDR capabilities and use the feedback mechanism in the Microsoft Defender Security Center or join the discussion below to share your thoughts.