This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Hello everyone! Tim Beasley coming at ya’ from the cold, destitute land we humbly call Misery (Missouri). Sometimes I really miss Texas… Anywho. One of my amazing customers recently asked about the illusive “Vulnerability Assessment” we introduced to Azure Security Center not too long ago. They struggled to find it and thought it was just a myth.
Once upon a time...A young man was venturing out on the internet and stumbled upon a Microsoft article talking about Vulnerability Assessment Services available in Azure Security Center. Reading the article, he thought to himself, “Hey! This is a really cool idea and I am wondering if I need to check my own VMs inside my Azure tenant…Thanks Microsoft!” So he logged into his Azure tenant, and followed the instructions to review the ASC Recommendations. However, he couldn’t find the recommendation the article above referenced! “Oh no! What do I do now?!”
Rest assured there’s a way to get it to work in ASC and start using the vulnerability tests from our 3rd party partners in the industry.
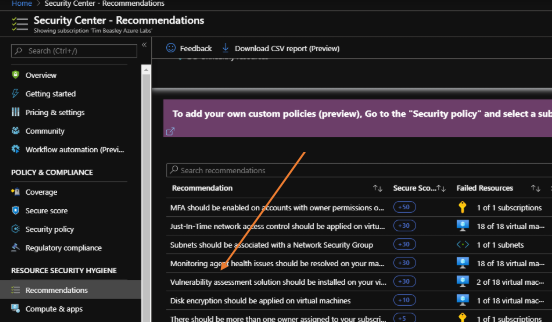
This is a simple guide to implement the specific recommendation of “Vulnerability assessment solution should be installed on your virtual machines.” In some instances, Azure Security Center (ASC) will display this as a recommendation without having to do anything. But in other instances, you might want to run a scan against your own tenant / VMs and this particular recommendation is no where to be found.
Pertaining to the article above, the Vulnerability assessment check will search your VMs to find any solutions that are installed…if one can’t be found, it recommends you deploy one. Afterwards, the partner agent that gets deployed starts reporting vulnerability data back to the partner management services, which in turn reports data back to Azure Security Center. Currently the 2 partners that have available vulnerability agents for this specific check are Rapid7 and Qualys. That’s currently though... :)
Now that the background is established, how do we go about enabling this recommendation when it doesn’t seem to exist in ASC’s recommendations?
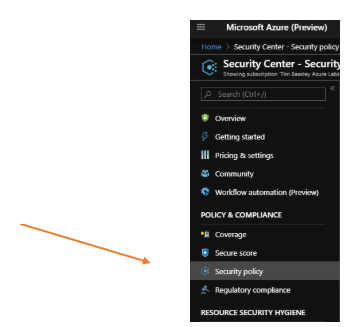
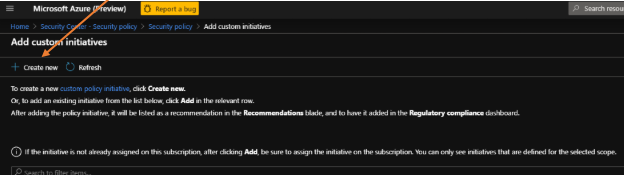
First, log into your Azure tenant and what we need to do is “Add a custom initiative” found under ASC, Security Policy. For further info:
*Dark theme in use
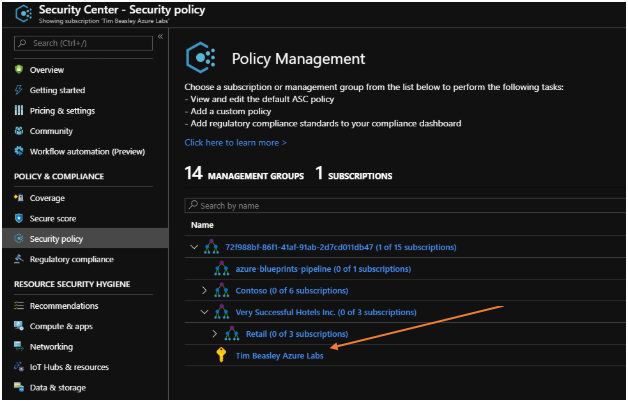
Once you’re in Security Center – Security Policy, you will see in the right pane in Policy Management, all subscriptions you have. Simply click on the subscription that you want the Vulnerability assessment check to be associated with. In this example, I’m using my “Tim Beasley Azure Labs” Subscription.
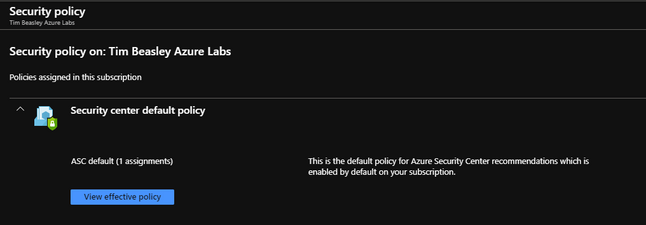
Now you should be in the Security Policy pertaining to your subscription.
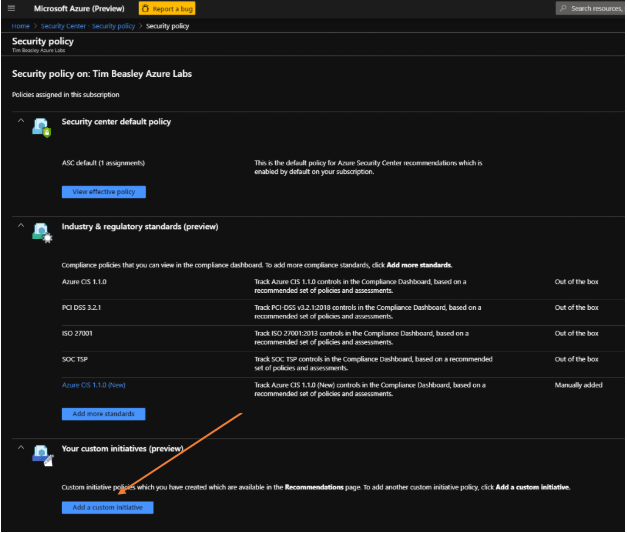
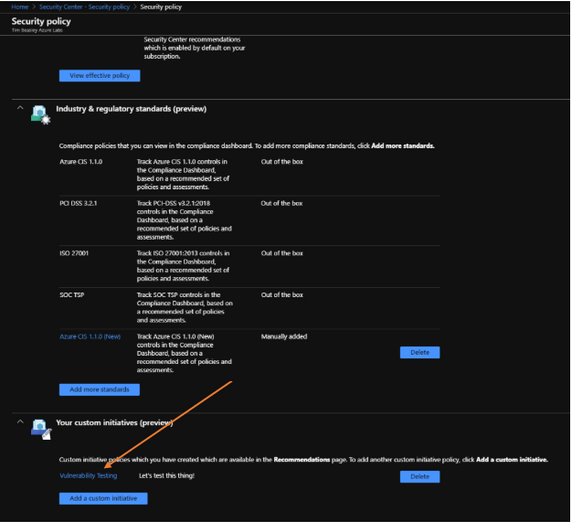
You’ll see 3 sections, one being Security Center Default Policy, then Industry & Regulatory standards (preview), and Your custom initiatives (preview).
What’s interesting about these 3 sections is that you can use this to help shape what ASC scans for within your tenant. If you are having to manually add the Vulnerability checks to your subscription, then if you were to click on “view effective policy” button in the “Security Center default policy” section, you will notice that the Vulnerability scans aren’t part of the ASC default policy.
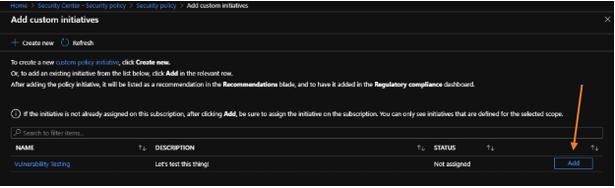
Of the 3 sections, the one you want is “Your custom initiatives (preview)”. Click on “Add a custom initiative” (see below)
Then click the “create new” button to start creating a new custom policy initiative.
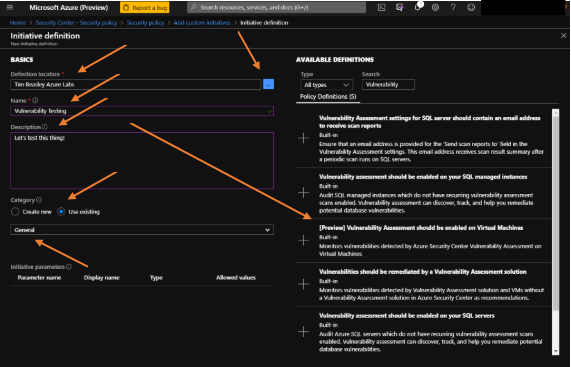
Next, we must define the initiative definition basics. This includes the location, name, description, category and parameters if needed.
For the “Definition Location” click on the ellipses button, and this will launch another window for you to select your subscription. Choose the subscription you want the checks to run against. Afterwards, you should see available definitions populate on the right side. Filter/search for “Vulnerability” and it’ll narrow down the available options and low and behold, there’s the one we’re looking for! Fill out the fields for Name, and for category, select “use existing” then pick the General option from the drop down list.
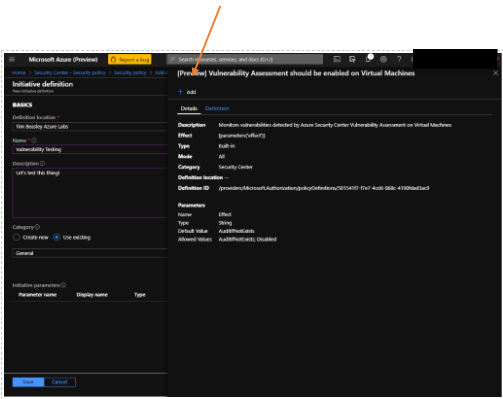
Great! Now go ahead and select the “(Preview) Vulnerability Assessment should be enabled on Virtual Machines” and another window opens. Click the “add” button. (screenshot below)
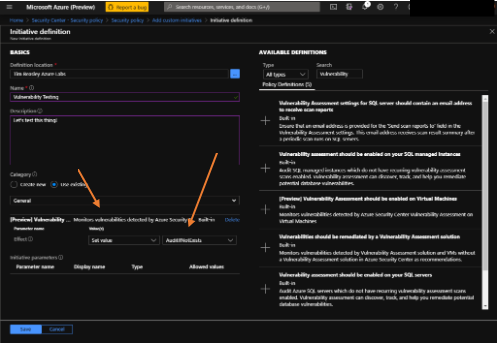
The window closes, and now you’ll see that option added to your custom initiative along with some additional options. Ensure the “AuditIfNoExists” option is selected. Click the Save button.
After saving, it’ll take you back a screen and you will see your new custom initiative for Vulnerability tests are now available. (see below)
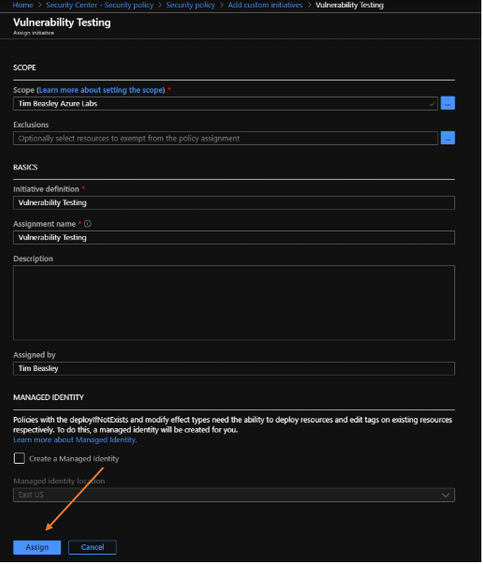
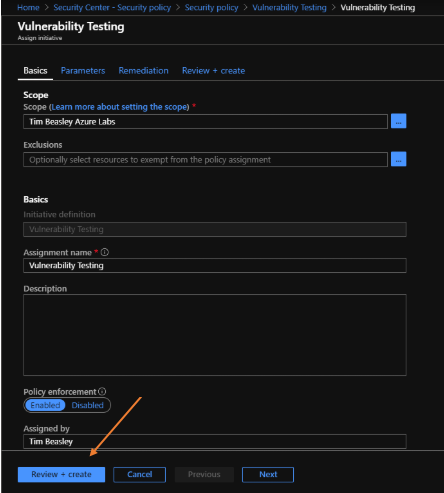
Clicking the Add button (above) will start the “assignment” process. Most of the fields auto-populate so not much is needed here.
Simply click on the “assign” button (below) after you’ve verified the field information.
And back to the main Security Policy window for your subscription we go! You might think that’s all there is to it, but…we aren’t done yet!
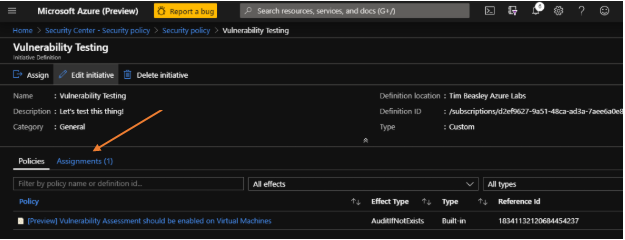
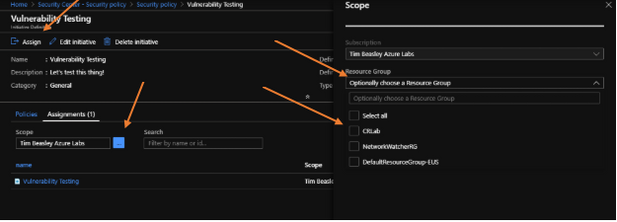
We still have to associate it to the proper Resource Group within your subscription. Otherwise it won’t do anything. So now click on the Initiative title you gave it. In this example, it’s “Vulnerability Testing.”
Within the next screens, you can assign the resource group you want ASC to check against, mark exclusions on resources, etc. Click on the “assignments” link (below) to open it up and make any changes necessary.
Click the ellipses button to open up scope modifications. Make any selections, and then click the “Assign” button at the top left. (screenshot below)
After clicking the “Assign” button, it’ll open up the policy initiative again, and just click on the “Review+Create” button if you don’t need to make any more changes. (screenshot below)
Click “Create” and you’re done. FINALLY!!!
Now all you have to do is make sure your VMs are running within your subscription and wait for ASC to scan them. Typically takes about an hour or so. Afterwards, you can follow the article instructions that I mentioned at the beginning of this guide to implement the vulnerability assessment agents.
Happy scanning! Oh, and don’t forget to give kudos to your fellow PFEs! Tim Beasley – out for now.