This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Hi folks, Ned Pyle guest-posting today about SMB over QUIC, a game-changer coming to Windows, Windows Server, and Azure Files. In today’s world, SMB file share access for mobile users requires expensive & complex VPNs. Departments trying to use Azure Files often find their ISP has blocked port 445. Even though users are just as likely to be deskless and organizations are doing more hybrid computing than ever, SMB hasn’t kept up.
That’s all changing with SMB over QUIC.
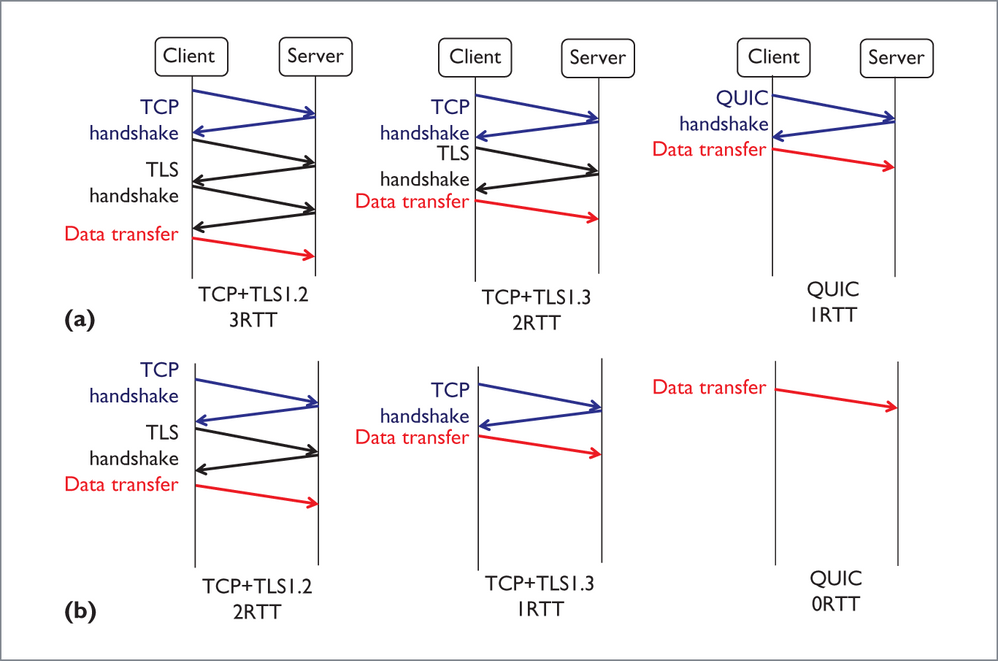
QUIC is an IETF-standardized protocol that replaces TCP with a web-oriented UDP mechanism that theoretically improves performance and congestion, but still tries to maintain TCP’s reliability & broad applicability. Unlike TCP, QUIC is always encrypted and requires TLS 1.3 with certificate authentication of the tunnel.
QUIC’s already in use in Windows 10 through the Edge browser and other apps. With QUIC over SMB – I don’t have a clever marketing name for this yet :) – QUIC becomes the transport, optionally replacing TCP/IP and RDMA, as well as a tunnel securing all SMB payloads with encryption, even if SMB encryption is not enabled, all while multiplexing over port 443 to an enlightened share. An admin will be able to opt-in to this new capability by deploying a Windows Server at the edge of the network, installing a certificate trusted by clients, then enabling the QUIC option. Or enable it on their Azure Files instance.
We have two design imperatives for SMB over QUIC:
- Secure: Prevent man-in-the-middle and spoofing by malicious parties as well as guarantee no sniffing of that sweet file payload or allowing any user credentials onto the Internet. The entire SMB conversation – negotiate capabilities, authentication, authorization, message bodies – all occur inside the QUIC layer, just like if the user was in an IPSEC or VPN tunnel. Yes, it even blankets NTLM challenges.
- Simple: The user experience for SMB over QUIC can’t change from their corpnet/LAN/branch office experience, it’s too expensive to retrain users. So, we don’t add extra UI or command-line arguments to the client experience – their updated Windows 10 machines will simply try TCP and RDMA like always, but then wait briefly and try QUIC too. This means if they can get faster perf on a local network with RDMA or unencrypted TCP, they will. And if they are travelling or an admin mandates QUIC, they can get that instead. All seamless to the end user and their apps.
Here’s a quick (heh) demo of the user experience. Spoiler alert: a user probably can’t tell anything changed except that SMB now works when I’m at a hotel for Microsoft Ignite.
The question I always get at this point is: when is this coming? I don’t have a good answer yet, but as we get firmer, I'll get more details out there. This is a key technology for Azure Files and Windows Server edge computing, as well as our mobile strategy, so all I can say is that it’s coming. As you can see from the demo, we’re far along. Check back at the ITOpsTalk.com and FileCab blogs for more details and info on Insider Previews this year. We are working with third parties to offer up this choice in other mobile platforms as well – you should be asking your vendors what their plans are.
I hope you’ve enjoyed learning about this new feature, I think it’s a real game changer. If you have questions, hit me up on twitter or DM me on TechCommunity.
- Ned Pyle