Introduction
As a cloud native SIEM solution, our innovation continues to help enterprises protect assets across distributed environments, analyze the growing volume of security data, and prioritize response to real threats.
We recently announced new exciting product updates and 3rd party integrations including the integration with SOC Prime, with the intent to help enterprises stay on top of emerging security threats and reduce implementation time.
This is the first installment of a 3-part blog on Azure Sentinel’s integration with SOC Prime. Today’s posts delves into the first point of the SOC Prime integration, the Uncoder.io service, which provides enterprises the ability to seamlessly convert Sigma rules to functional Azure Sentinel queries & rules.
The second installment of this blog will provide the steps to configure the integration between Azure Sentinel and SOC Prime , which will empower you to expand your threat detection content by leveraging SOC Prime’s extensive threat detection marketplace.
What is Sigma?
Sigma is an open source project to create a generic signature format for SIEM systems that enables analytic re-use and sharing. The common analogy is that Sigma is “the log file equivalent of what Snort is to IDS and what YARA is for file-based malware detection.” Sigma acts as the proverbial “rosetta stone” for all platform-specific query languages and enables translation across a myriad of search languages.
Please reference the Importing Sigma Rules to Azure Sentinel blogpost to further understand what Sigma is and how to utilize the sigmac tool to import sigma rules into Azure Sentinel.
What is Uncoder.io?
One Common Language for Cybersecurity
Uncoder.io is SOC Prime’s free tool for SIEM search language conversion. Uncoder relies upon Sigma to act as a proverbial “rosetta stone”, enabling event schema resolution across platforms.
Uncoder.IO is the online translator for SIEM saved searches, filters, queries, API requests, correlation and Sigma rules to help SOC Analysts, Threat Hunters and SIEM Engineers. Serving as one common language for cyber security it allows blue teams to break the limits of being dependent on single tool for hunting and detecting threats.
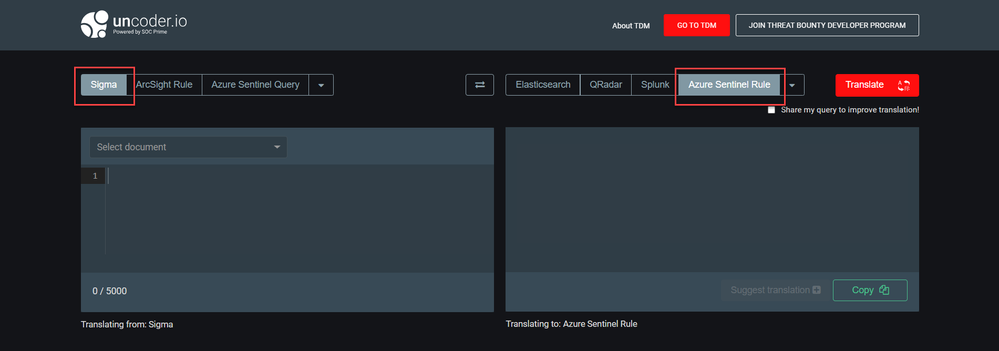
Access the translation tool here: https://uncoder.io/#
Undecoder.io Conversion
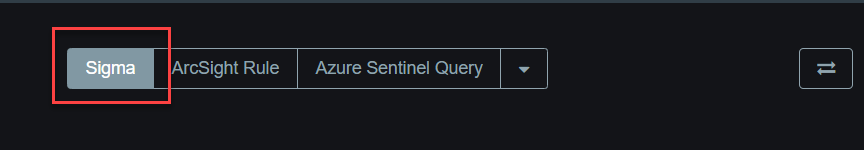
1. The first step to convert Sigma Rules into an Azure Sentinel rule or query Is to select Sigma as the “Input Language” on the top left:
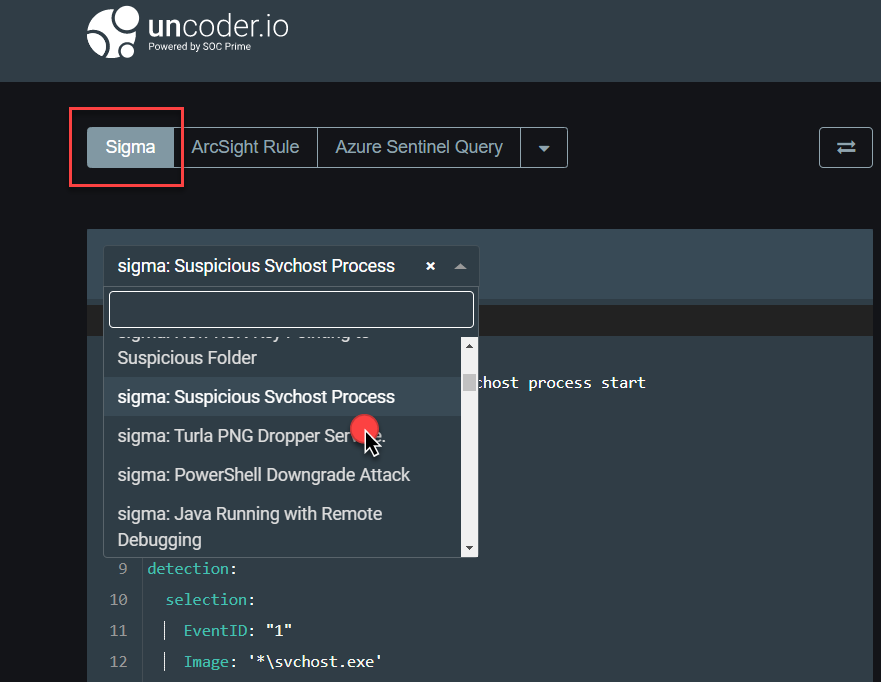
2. Next, you will need to paste a query into the left text box or select a pre-set Sigma query from the drop-down:
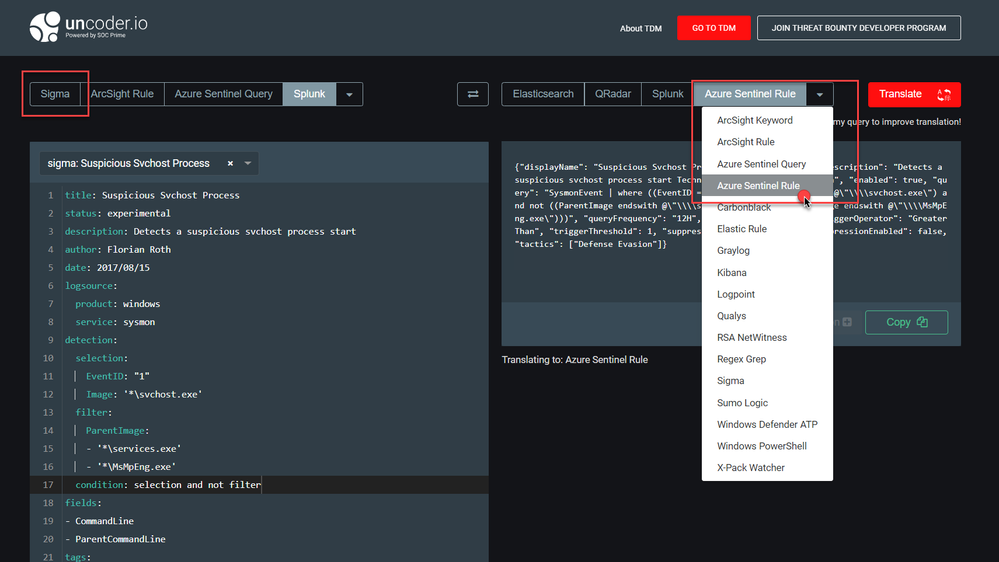
3. You have the ability to select “Azure Sentinel Query” or “Azure Sentinel Rule” as the Output language on the top right.
4. Lastly, copy the translated results and leverage them to investigate, hunt, and create an analytic rule in Azure Sentinel
Note: Please reference our public documentation on how to create custom analytics to detect suspicious threats in Azure Sentinel.
In this first installment of the blog, we covered how you are able to reduce implementation time by leveraging SOC Prime’s Uncoder.io to convert Sigma rules to functional Azure Sentinel Queries and Rules.
In the next installment of the blog, we will dive in deeper into the integration between Azure Sentinel and SOC Prime. We will provide the detailed steps to configure the integration, which will empower you to expand your threat detection content by leveraging SOC Prime’s extensive threat detection marketplace.
Until then, try it out and let us know what you think!