This post has been republished via RSS; it originally appeared at: Intune Customer Success articles.
By Matt Shadbolt (@ConfigMgrDogs) | Principal Program Manager, Microsoft Endpoint Manager
Microsoft is excited to announce another step in the deep integration between Microsoft Endpoint Manager and Microsoft Defender ATP. Microsoft Defender ATP onboarding capabilities are now available in the Endpoint Manager console for deployment to Configuration Manager standalone clients.
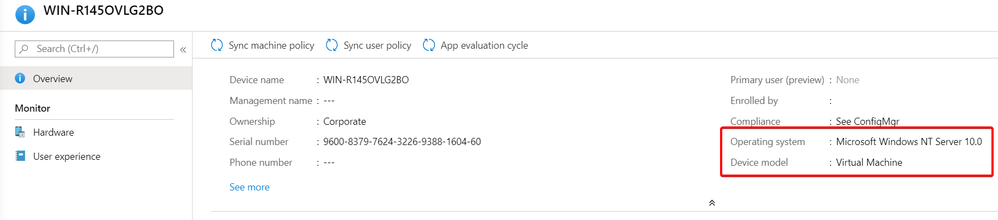
Onboarding a client to Microsoft Defender ATP will enable Endpoint Detection and Response, Threat and Vulnerability Management and many other SecOps related functionalities available in the Microsoft Defender Security Center. Once onboarded, the endpoint will appear in the Defender Security Center and advanced security events and insights will become available.
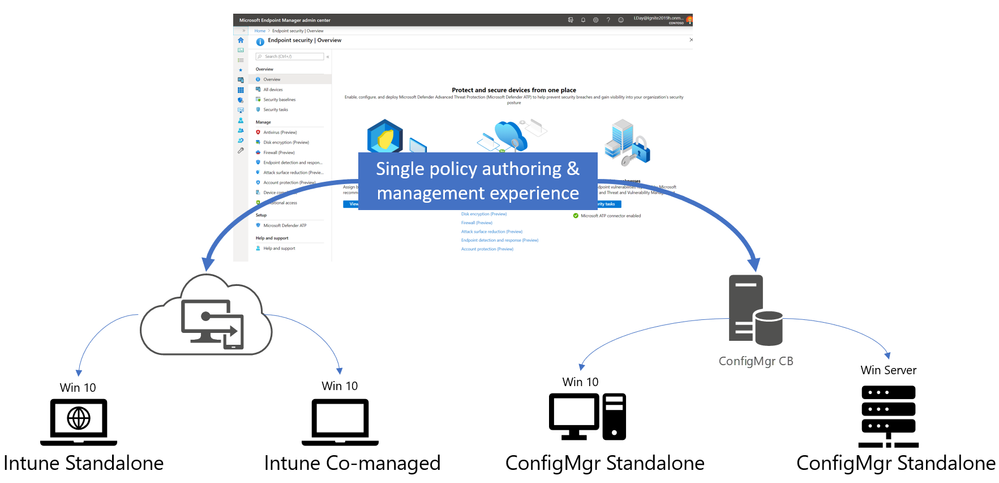
This creates a single Microsoft Defender ATP onboarding experience for Microsoft 365 customers, for any client supported by Microsoft Endpoint Manager be they Configuration Manager, Intune, or co-managed (when a Windows 10 device has the Configuration Manager client and is enrolled to Intune).
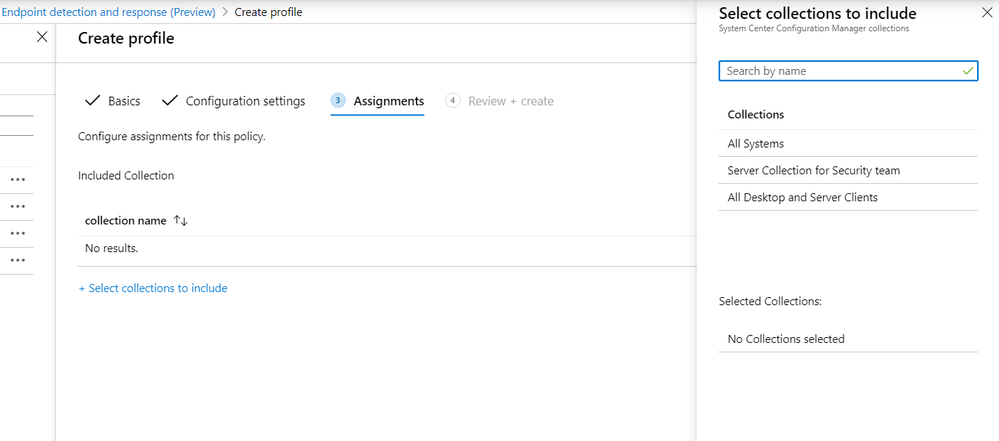
From the Microsoft Endpoint Manager admin center, Security administrators can configure and target Microsoft Defender ATP onboarding policies to Configuration Manager collections for on-prem managed devices, or Azure Active Directory groups for cloud managed clients.
The policy can even be deployed to Windows Server clients managed by Configuration Manager, ensuring your security team have full coverage of every enterprise managed device all from the Endpoint security node in Endpoint Manager.
This is the first of several new Defender ATP configuration policies which will be made available to Configuration Manager only clients. In future, we plan to add support for Antivirus, Tamper Protection, Attack Surface Reduction and other security workloads, allowing your security and IT teams to securely configure their endpoints from a single management experience.
To read more about how to use this feature, please see our technical documentation.