This post has been republished via RSS; it originally appeared at: SQL Server articles.
Create a Key Vault using the Azure Portal
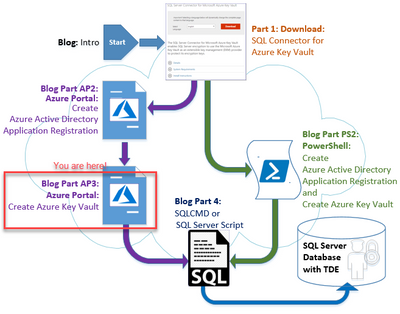
This is Part: AP3 (Azure Portal) of a 4-part blog series:
This blog in the series provides the step-by-step instructions to create an Azure Key Vault using the Azure Portal.
To grant SQL Server access permissions to your Azure Key Vault, you will need a Service Principal account in Azure Active Directory (AAD) (created in Part: AP2). The Azure Portal can be used to create the Key Vault and add an Azure Active Directory Principal to the Key Vault.
- Go to the Azure Portal, and sign in.
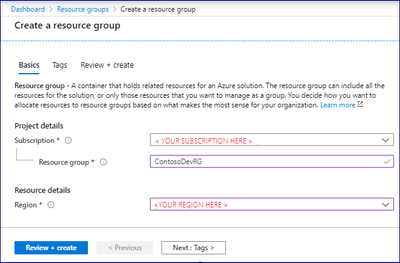
- Create a new resource group. All Azure resources created in Azure must be contained in resource groups. Create a resource group to house your key vault. This example uses ContosoDevRG as the Resource Group. Choose your own unique resource group and key vault name as all key vault names are globally unique.
a) Optionally: You may use an existing Resource Group as well.
- Using the Azure Portal: Create a Resource Group (if one does not already exist that you want to use)
a) Step 1: Select your subscription
b) Step 2: Name a new Resource Group (or select an existing Resource Group)
c) Step 3: Select the Region
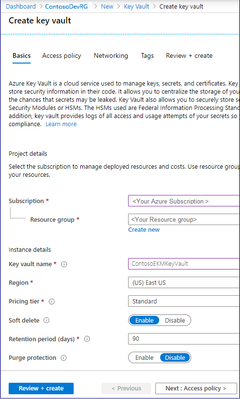
- Create the Key Vault
a) Step 1: Select your subscription
b) Step 2: Name a new Resource Group (or select an existing Resource Group)
c) Step 3: Enter a Key Vault Name (26-character limit)
d) Step 4: Select the Region
e) Step 5: Select Pricing Tier: OK to default
f) Step 6: Select Soft delete: OK to default (Key Vault's soft-delete feature allows recovery of the deleted vaults and vault objects)
g) Step 7: Enter Retention Period (days): OK to default (or set as appropriate for your needs)
h) Step 8: Select Purge protection: OK to default (or set as appropriate for your needs. Purge protection can only be enabled once soft-delete is enabled. When purge protection is on, a vault or an object in the deleted state cannot be purged until the retention period has passed).
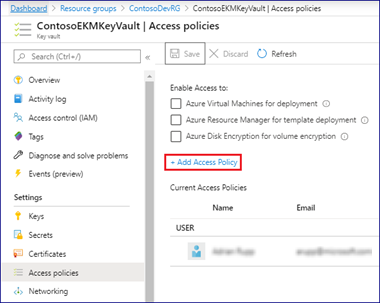
- Add Access Policy to Azure Active Directory Principal (Application)
a) Step 1: Select “Access policies” node
b) Step 2: Click on “+Add Access Policy”
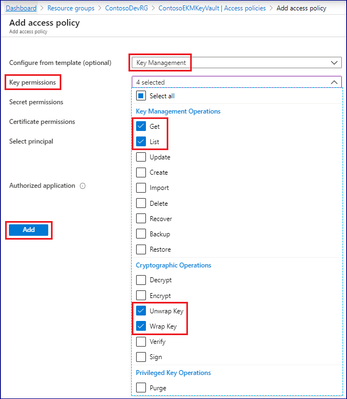
- Access Policies: Get, List, Unwrap Key, Wrap Key
a) Step 1: Configure from template: Select dropdown = “Key Management”
b) Step 2: Select permissions in dropdown(Get, List, Unwrap Key, Wrap Key)
c) Step 3: Click “Add”
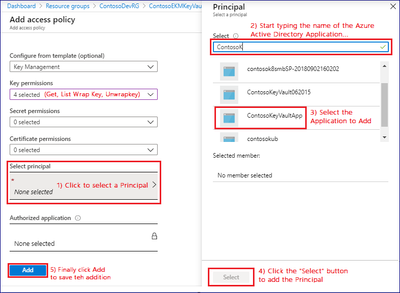
- Add a Principal (Azure Active Directory Application) to the Key Vault.
a) Step 1: Click Select principal (to bring up the Principal dialog)
b) Step 2: Search for the same Azure Active Directory Application you registered in the previous blog (SQL Server TDE EKM Using Azure Key Vault – Part:2AP).
c) Step 3: Once the Principal appears, select the Principal
d) Step 4: Click the “Select” button to accept
e) Step 5: Click the “Add” button
Conclusion
Configuring Azure Key Vault is the third step in configuring SQL Server TDE to use Azure Key Vault. Continue the setup process for SQL Server using SSMS or SQLCMD.
See you at the next blog (Part: 4)
Adrian
Next steps
| SQL Server Transparent Data Encryption and Extensible Key Management Using Azure Key Vault – Intro | |
|
SQL Server Connector for Microsoft Azure Key Vault (aka: SQL Server Connector) – Part: 1 |
|
|
Azure Portal Method |
PowerShell Method |
|
Set up an Azure Active Directory Service Principal – Part: AP2 |
Setup Azure Active Directory Service Principal and Azure Key Vault (one script) – Part: PS2 This script combines Part: AP2 & Part:AP3 |
|
Create an Azure Key Vault – Part: AP3 (this document) |
|
|
Configure SQL Server TDE EKM using AKV – Part: 4 |
|