This post has been republished via RSS; it originally appeared at: IIS Support Blog articles.
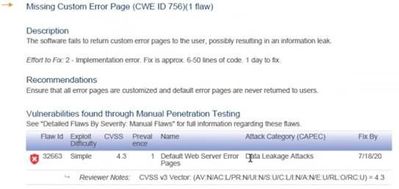
IIS comes with default error pages. In order to help troubleshooting issues, these error pages may provide detailed information about the application and server. Therefore, some penetration testing tools may flag this situation as a vulnerability. An example pentest report:
Missing Custom Error Page (CWE ID 756)
The software fails to return custom error pages to the user, possibly resulting in an information leak.
Solution
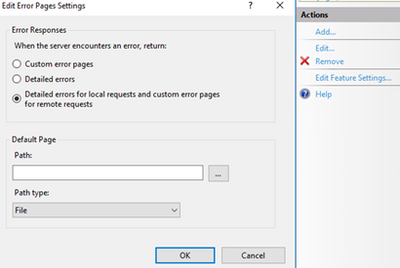
Unless detailed error pages are enabled for remote requests in IIS, I wouldn’t classify this situation as a critical vulnerability.
If you want to have a clean security scan report (and you want your users to see more meaningful error pages), you can create custom error pages.
In the case I worked on, the tool brought up this report for a folder that doesn’t have a default page. For this situation, there are a few easy workarounds:
- Add an index.html file to the folder. This should prevent that URL to be flagged again
- Customize IIS defaullt page for 403 error (C:\inetpub\custerr\en-US\403.html). Pentest tool is likely to mark the URL pass if that page is customized
- Enforce custom error pages in web.config