This post has been republished via RSS; it originally appeared at: ITOps Talk Blog articles.
Some great new announcements and an important certificate change to tell you about this week.
Azure Communication Services (SMA and Telephony) is now available in public preview. There's an important change to the root certificate authority of the TLS certificates used by Azure services. Conditional Access to the Office 365 Suite is now generally available. And we look at managing Azure Policies as code in GitHub. Let's go!
Azure Communication Services SMS and Telephony now available in Public Preview
Azure Communication Services makes it easy to add voice and video calling, chat, and SMS text message capabilities to mobile apps, desktop applications, and websites with just a few lines of code. While developer friendly APIs and SDKs make it easy to create personalized communication experiences quickly, without having to worry about complex integrations.
These capabilities can be used on virtually any platform and device. Build engaging communication experiences with the same secure platform used by Microsoft Teams.
View the announcement
Learn more about Azure Communication Services
IMPORTANT: Azure TLS certificate changes
Microsoft is updating Azure services to use TLS certificates from a different set of Root Certificate Authorities (CAs). This change is being made to comply with one of the CA/Browser Forum Baseline requirements.
This exercise will conclude on October 26, 2020. This will impact customers who use certificate pinning (to explicitly specify a list of acceptable CAs) or customers with specific operating systems that talk to Azure services and may require steps to correctly build the cert chain to the new roots (e.g. Linux, Java, Android etc).
For more information, see Azure TLS certificate changes
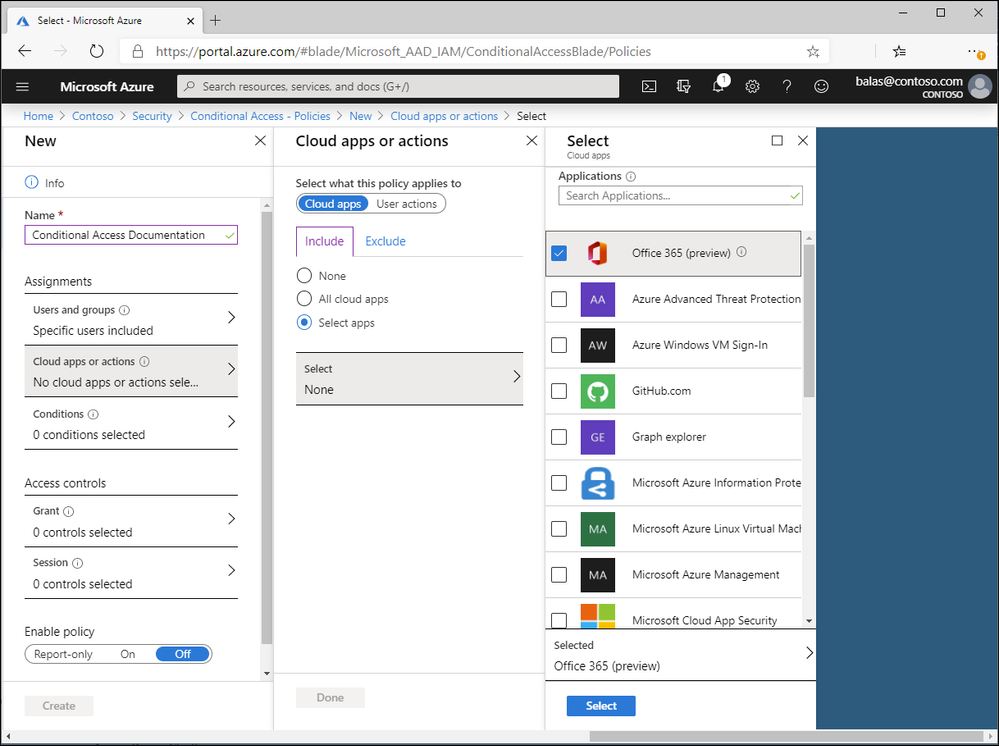
Conditional Access for the Office 365 Suite now in GA
Conditional Access Policies give you a greater level of control over enforcing security requirements when accessing Office 365 applications, but with the apps sharing many underlying services, it can be hard to keep these policies consistent. You can now set conditional access policy requirements across the entire suite of Office 365 apps, including Exchange Online, SharePoint Online, and Microsoft Teams, as well as micro-services used by these well-known apps.
Premiered in public preview in Feb 2020, this capability is now Generally Available.
Learn more about Conditional Access for the Office 365 Suite
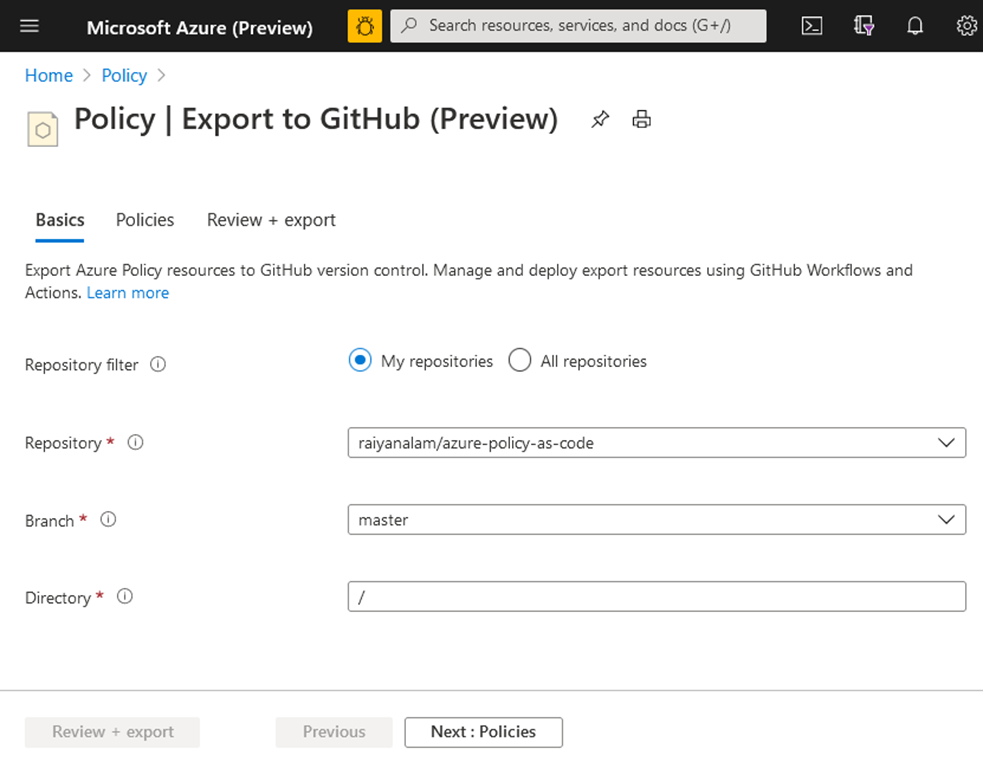
Enabling resilient DevOps practices with code to cloud automation
Thanks to Pixel Robots (Discord) for bringing this one to our attention.
As you progress on your Cloud Governance journey, there is an increasing need to shift from manually managing each policy in the Azure portal to something more manageable, collaborative, and repeatable at enterprise scale. We are announcing that we made the integration between Azure Policy and GitHub even stronger to help you on this journey.
You can now easily export Azure policies to a GitHub repository in just a few clicks. All exported policies will be stored as files in GitHub. You can then collaborate and track changes using version control and push policy file changes to Azure Policy using Manage Azure Policy action. See Managing Azure Policy as Code with GitHub to learn more and go to Azure Policy to access the feature.
View the full product group blog on enabling resilient DevOps practices with code to cloud automation.
MS Learn Module of the Week
Build a cloud governance strategy on Azure
Keeping a Cloud environment controlled and consistent can be challenging, as it expands and as more teams have access to deploy and change resources. Enable teams to have the control they need, within the boundaries you set, and avoid configuration drift by implementing a cloud governance strategy. This module is part of a newly updated set of Azure Fundamentals training, and includes exercises in the free Azure sandbox environment.
After completing this module, you'll be able to:
- Make organizational decisions about your cloud environment by using the Cloud Adoption Framework for Azure.
- Define who can access cloud resources by using Azure role-based access control.
- Apply a resource lock to prevent accidental deletion of your Azure resources.
- Apply tags to your Azure resources to help describe their purpose.
- Control and audit how your resources are created by using Azure Policy.
- Enable governance at scale across multiple Azure subscriptions by using Azure Blueprints.
Let us know in the comments below if there are any news items you would like to see covered in next week show. Az Update streams live every Friday so be sure to catch the next episode and join us in the live chat.