This post has been republished via RSS; it originally appeared at: Azure Database Support Blog articles.
Issue: After enabling the Storage Account firewall, Azure SQL Database audit logs are not being written.
Mitigation steps:
If your storage account meets all this pre-requisites in this documentation and the audit is still not being written, please follow the steps below:
- Configure the Storage Account firewall to “Allow access from: Selected networks” and “Allow trusted Microsoft services to access this storage account”
- Disable the audit in the Azure SQL Database server and save
- Wait for the deploy to finish
- Wait 5 minutes
- Enable the audit again and save
- Wait for the deploy to finish
- Check if now the audit is being successfully written to the Storage Account.
By turning the audit on the Azure SQL Server ON after the Storage Account firewall is enabled, if the user has appropriate permissions, it should perform the necessary configurations in terms of permissions to the service.
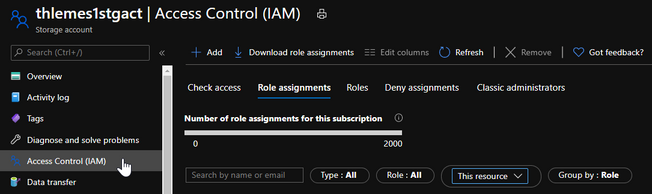
If the audit is still failing, please open a support request and let us know if you have received any error messages during the steps above and what permissions the server has in the Storage Account IAM, with the scope filtered by ‘This resource’:
Note: After performing the steps above, the Server should normally have the permission “Storage Blob Data Contributor” in the Storage Account