This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
The integration of Azure Advisor with Azure Kubernetes Service (AKS) means you can can get telemetry based - proactive + actionable - recommendations for your AKS clusters enabling you to follow best practices towards maintaining cluster hygiene.
This is the active set of Advisor recommendations for AKS -
- Use of Pod Disruption Budgets
- Expired Service Principals
- Unsupported Kubernetes Versions
- Expired cluster certificates
- Deleted OMS workspace for Azure Monitor
and with more on the roadmap like -
- Resource requests/limits not set
- Namespace quotas not set
- Subnet running out of IP addresses
- Service address range overlapping with another CIDR range in the VNET
Let us take a look at a couple of such scenarios and related recommendations -
Ensure cluster is running a supported version
I have a relatively older demo cluster running Kubernetes version [1.16.7] which means my cluster is out of support.
Not upgrading the cluster to a AKS supported Kubernetes version means missing out on one of the key reason to use managed service - support.
Also, there is the risk of running a cluster with crtitical security vulnerabilities.
Learn more about the version support policy here and the related FAQ section - here .
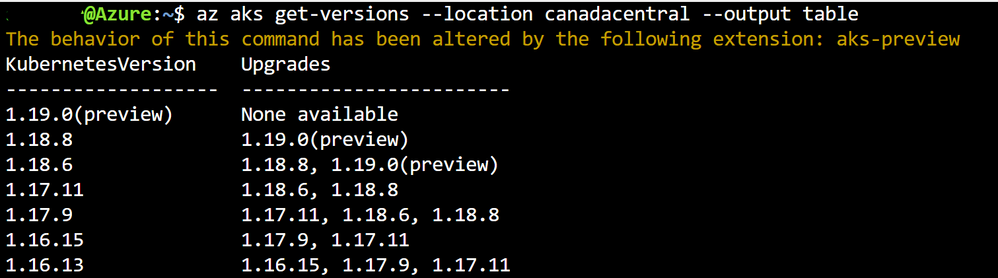
Let us list the supported versions for my cluster's region with the Azure CLI command
This results in showing us the supported versions and possible upgrades each one of those versions could have. Note that v1.16.7 does is not listed.
So, how does Azure Advisor help here ?
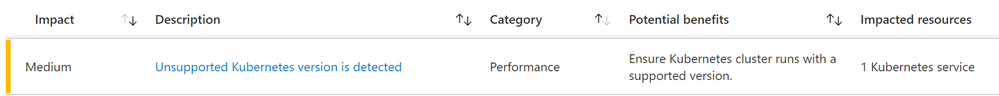
By providing a proactive recommendation based on detecting the unsupported version -
Pod Disruption Budget recommended
I have not setup PDBs for a set of my active deployments in the cluster - which means I essentially run the risk of application / service unreliability by not following the best practice.
More details of PDBs an related best practice here -
Azure Advisor now recommends as depicted -
References:
Microsoft Videos : Bringing Kubernetes best practices to everyone | Video 1 | Video 2