This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
The extensive use of collaboration tools during the COVID-19 remote work era is putting many organizations at even higher risk for phishing attacks: via business emails or video conferencing solutions. This may be a good opportunity to refresh your workflows in investigating Microsoft Defender for Office 365 alerts, which can assist in catching cyberattacks in early stages.
What is an alert?
In Microsoft Defender for Office 365, we create billions of signals daily, for every phishing email we defuse. If the email was automatically blocked, deleted or neutralized in other methods – we do not create an alert for it, as no additional action is required from the security team. You can review the blocked phish or malware events in the Threat Explorer.
If we detect a suspicious activity, which was not blocked before delivery due to various reasons, and we think it requires your attention, we generate an alert for it. The common reasons that malicious activities are not blocked include a misconfiguration of the product, a delayed threat intelligence signal like Zero-hour Auto Purge (ZAP), user reported phishing emails, URLs weaponized at time-of-click and more. All of these cases trigger alerts when a suspicious activity is detected, and these alerts require an investigation by the security operations team.
Alert policies
Every alert is created because of an alert policy, which helps you to determine what suspicious activities you want to be notified of. For this purpose, we have created many out of the box alert policies, which generate alerts. You can enable or disable these policies, update recipients, update category, severity level and other parameters that will help your SOC with day-to-day operations while working with the alerts. For more information, see our docs article on alert policies.
Customers that are interested in investigating more granular alerts can create custom alert policies, that trigger custom alerts. A custom policy can be configured to trigger for a specific attachment type, a ZAP operation, or when a specific audited operation occurs in Office 365. For more information on managing alerts, see managing alerts on docs.
Manual alerts investigation by the Security Operations team
Since every alert is a call-for-investigation by the security operations team, these teams need to determine the next step required to mitigate the threat of malicious content, or dismiss the alert. Such an investigation usually follows one of these workflows:
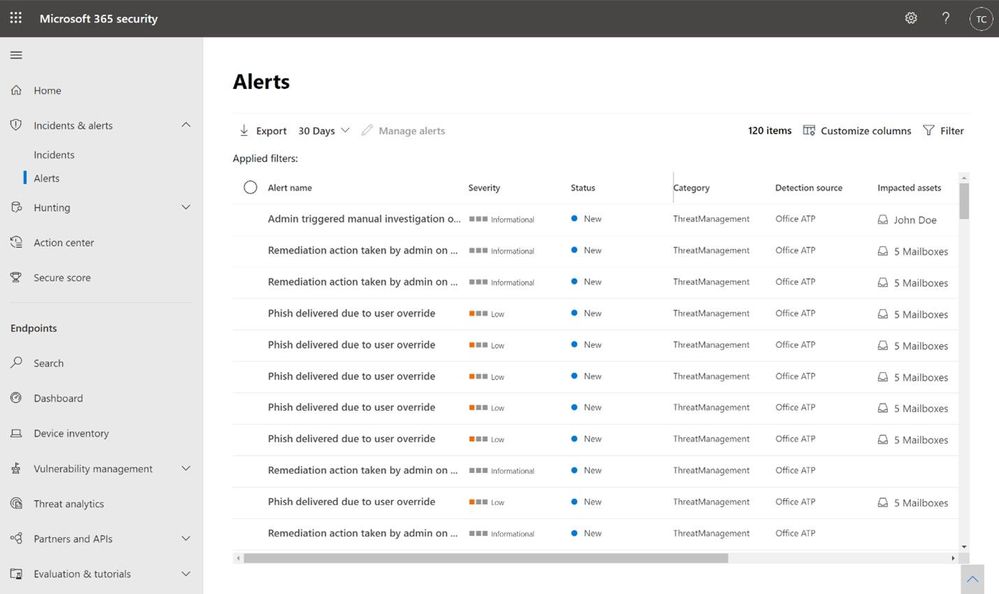
Analyze the alerts queue
The alerts queue allows security teams to investigate each alert, by drilling down in Threat Explorer or in Advanced Hunting, or to follow the relevant playbooks for remediation. The Microsoft 365 Defender alerts queue will provide a prioritized view of all alerts from multiple Microsoft security products: Defender for Office 365, Defender for Endpoint, Defender for Identity and Microsoft Cloud App Security. For more information on alerts in Microsoft 365 Defender, see our Ignite session on leveraging automated incident correlation to make Defender for Office 365 even more efficient.
If you are using a custom reporting or SIEM solution, you can also look to ingest information about Alerts surfaced through the Office 365 Management API to construct your own experience, and correlate it with additional data within your solutions.
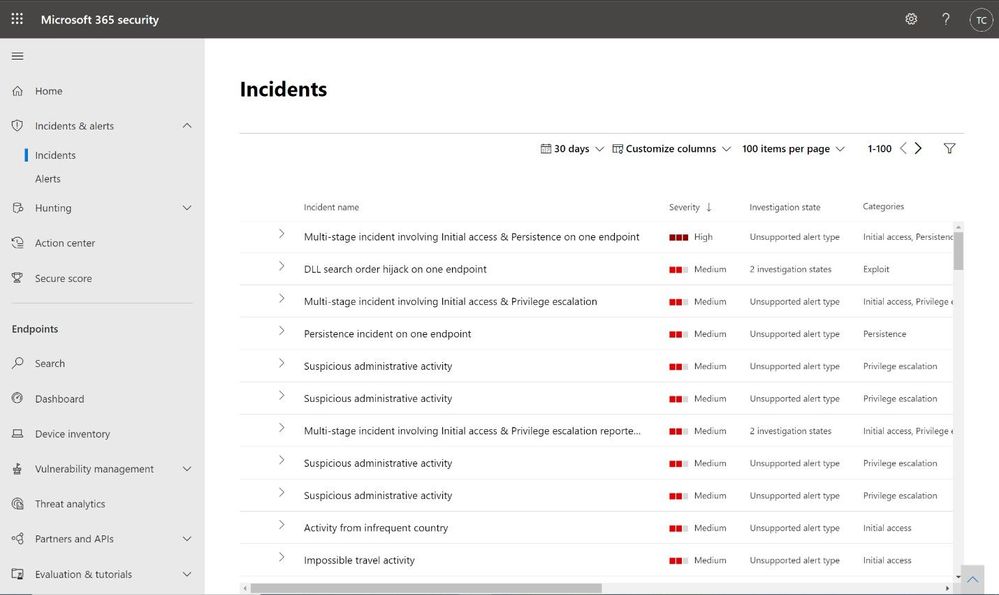
Analyze incidents
Incidents are a set of correlated alerts from various Microsoft security products. Microsoft Research creates correlation across alerts and events, taking care of the heavy lifting for the SOC team and helping them understand the overall impact of the attack on the organization across its digital estate and assets. Incidents help customers manage fewer items in their queue. On average, customers report an 80% reduction in Office 365 cases as a result of correlation during the first month alone.
The unified portal of Microsoft 365 Defender shows the entire incident overview, based on MITRE ATT&CK tactics: initial access, execution, lateral movement, and exfiltration. It also shows the timeline of the event, to provide a better understanding of the attack flow. This cross-product investigation fits into one unified view, like an email issue becoming an endpoint issue, or identity compromise resulting in cloud app resources utilization. Surfacing these incidents in a central place helps many organizations save time tackling the same attack that spreads via multiple tactics, triggering suspicious alerts by multiple products. You can learn more about Incidents in Microsoft 365 Defender in the Ignite session.
You can also look to ingest incidents within your custom solutions through the MTP Incident API (currently in Public preview).
The prioritization challenge
In both of the scenarios above, most organizations still have a very high volume of alerts to analyze. Many customers choose to prioritize the alerts that involve their most visible and most targeted users. With Priority Account Protection in Defender for Office 365, security teams can prioritize alerts for Priority Accounts, and ensure that these threats are addressed, even when alert volumes are high. Learn more about Priority Account Protection to ensure these priority accounts are always protected.
Additional prioritization methods may be based on threat Intelligence or focus on the latest or most common threats. And finally, we allow customers to add custom alerts, to identify specific threats that are relevant to the organization.
Automated investigation of alerts
Defender for Office 365 includes powerful automated investigation and response (AIR) capabilities that can save your security operations teams time and effort. Instead of reviewing, prioritizing, and responding to the continuous flood of incoming alerts, you can automate some of this to increase efficiency. An automated investigation can trigger a security playbook, depending on the incident type. Another option is for the security analyst to start an automated investigation using Threat Explorer.
Customers that investigate alerts using a third-party SIEM solution can use the Office 365 Management Activity APIs for the investigation. You can follow this detailed example of an organization that uses this integration for alerts investigation from a recent blog post on improving the effectiveness of your SOC with Defender for Office 365 and the O365 Management API. For additional information about the public APIs, see our documentation.
Malicious activity or false alarm?
For each alert, we provide additional information to help the security team to determine if this is indeed a malicious activity or not. We also provide governance actions to Resolve, Suppress and Notify users upon this alert, for further investigation. The decision regarding the appropriate governance action can be made after additional review of the alert details and context information in Threat Explorer or in Advanced Hunting.
Investigating suspicious alerts, more relevant than ever
In this time that many organizations are in historic rates of remote work, many customers experience an abundance of alerts that indicate suspicious activity. This can put pressure on the Security Operations teams to be more effective than ever in analyzing alerts created by Defender for Office 365. This is a good time to refresh the workflows around alerts investigation, to make sure the alerts are handled according to their real priority in the eyes of the organization. Moreover, it is a good opportunity to revise your use of the Automatic Investigation and Response (AIR) tools, to automate workflows that can reduce the manual investigation time by the Security Operations teams, and to reduce alerts which requires investigation by fully resolving some of these alerts automatically.