This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
If you enjoyed working on alerts in the alert queue of Microsoft 365 Defender or Microsoft Defender for Endpoint, we are excited to tell you that we have expanded the features of our incident queue. Now you can benefit from the sophisticated incident correlation logic of the incident queue without losing the capabilities you had in the alert queue.
This includes:
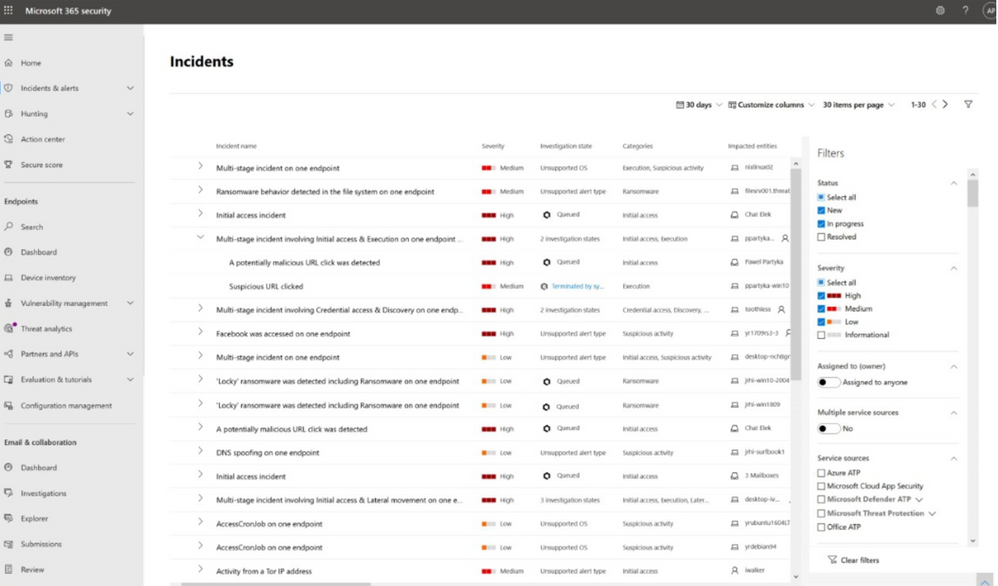
- Nested list of alerts grouped by incident
Enables you to quickly view which alerts make up each incident and easily drill down to each alert - Extended list of filters
Improves your ability to analyze incidents using more types of filters including investigation state, device groups, OS platforms, and more - Full alignment with Microsoft Defender for Endpoint alert queue
The new and improved incident queue now includes all the related alerts within the same queue. This means that right from the incident queue you can view all the associated alerts and open them directly. We also added more valuable columns like investigation status and device groups, filter capabilities that applies on the incidents based on any of the alerts’ attributes including investigation state, alert status, classification and more.
This capability can help you quickly assess, narrow down, and prioritize among incidents. For example, you can filter the incidents by device group to immediately see if sensitive devices have been affected--and spend your first few hours of the day analyzing those.