This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Cyber security has become embedded in the day-to-day activities of every organization, and more so as organizations shift and adopt a hybrid working model. Organizations want customized security tools that fit their existing IT environment and meet their needs of efficiency and effectiveness. Keeping this in mind, we continue to invest in Microsoft Defender for Office 365 and offer the best protection tools to manage detected threats, possible misses, and focus on continually improving investigation and response capabilities.
Introducing consistent navigation to the email entity page
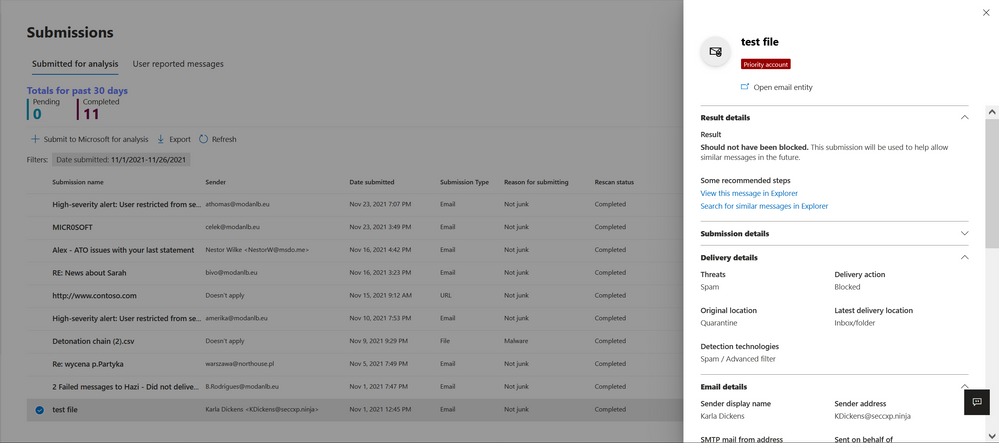
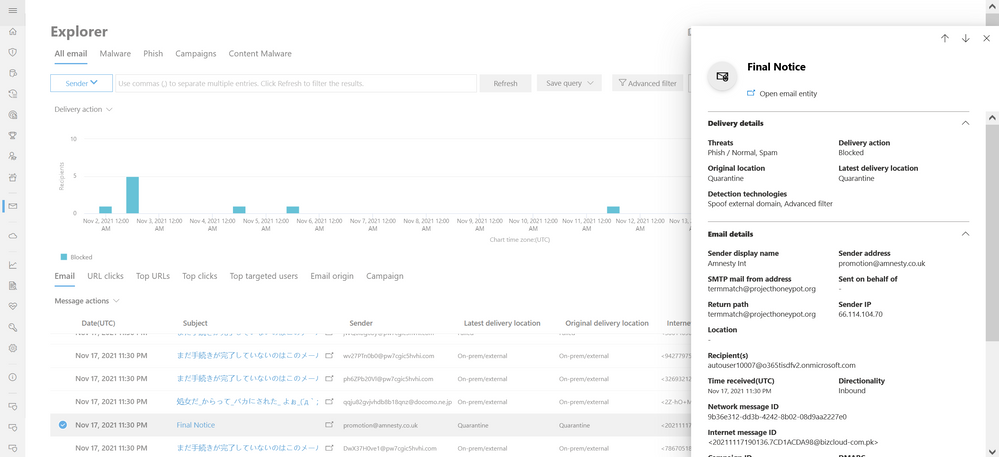
We’re making it easier to view a single, integrated, 360-degree view of an email through the email entity page and provide a more consistent experience across Microsoft Defender for Office 365 and Microsoft 365 Defender. The email entity page contains a summary panel with a condensed view containing standardized details about the email (e.g., detections) as well as context specific information (e.g., Quarantine or Submissions metadata). It replaces the traditional flyout that was integrated into Threat Explorer, Submissions, and Reporting.
In the 1st iteration, the summary panel will replace the traditional Explorer flyout or other flyouts with email summary panel information for the following experiences: Explorer, Real-time detections, Advanced Hunting, Threat Protection Status report, Submissions, and Quarantine. It will slowly expand to include other experiences like Unified Investigations, Alerts, and more. We will begin rolling out updates for Defender for Office 365 Plan 2 and E5 customers initially, and then extend this capability to P1 customers. For Exchange Online Protection (EOP) customers, the updates and rollout will happen later.

An improved experience for guided hunting
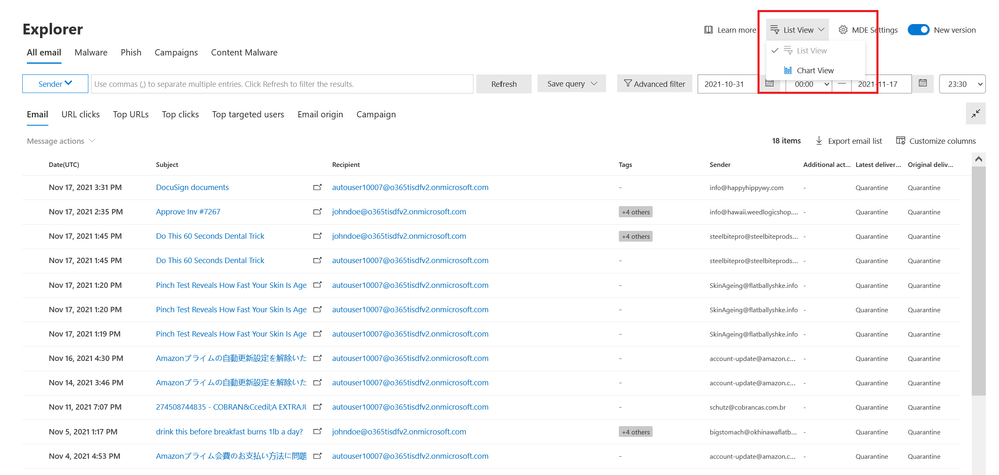
We are working towards modernizing the guided hunting experience in Explorer and real time detections. There is no change in functionality when it comes to core experiences like filtering, export, and saving queries; this is only an experience update to improve the workflows, as well as align with modern accessibility standards.
For a short while, as we roll out updates, you will be able to toggle between the old experience and new experience. Note that toggling impacts only your account and does not impact anybody else within your tenant.

All-email becomes the default view
The All-email view becomes the default view for Threat Explorer (Note: Malware view continues to remain the same for real-time detections), with the default time range set to 2 days , which is an update from the current default time range of 7 days (you can still extend the search period to a maximum of 30 days). You can also tab across different views to get to the desired Phish or Malware view.
You will be able to access the new email summary panel (once available) by clicking on the Subject in the grid. Alternatively, by clicking on the icon in Subject, you can navigate directly to the email entity page through the grid.
Within the view, you can also toggle between the Grid View and the List View to maximize your result set, as well as export the chart or the grid data through a single click.
The different entities like Email, URL, and IP move to a new, single tab-based view, and you can expand and collapse the different sections based on how you want to view the data.
We are also updating the experience around Threat Trackers for Saved queries, Tracked queries and Trending campaigns.

Note: In this new experience, we would be retiring noteworthy campaigns.
For Noteworthy campaigns, we recommend you navigate to the Campaigns view, where you can view the different campaigns as well as detailed writeups for those campaigns. You can also view additional details within Threat analytics, which is a set of reports from expert Microsoft security researchers covering the most relevant threats, including Active threat actors and their campaigns, popular and new attack techniques, critical vulnerabilities and more.
What’s next?
We will continue to integrate the email summary panel with more unified experiences like Alerts, Incidents, and Investigations. Additionally, we will continue to update Threat Explorer and Realtime detections, with additonal updates to filtering and actions. In the future, we plan on introducing remediation actions in Email entity, which allows you to take actions from the email entity page.
We will continue to share more updates as we near the rollout.
Do you have questions or feedback about Microsoft Defender for Office 365? Engage with the community and Microsoft experts in the Defender for Office 365 forum.
