This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
This month, Azure portal includes the ability to create custom RBAC roles, updates to Networking features and Azure Security Center.
Sign in to the Azure portal now and see for yourself everything that’s new. Download the Azure mobile app to stay connected to your Azure resources anytime, anywhere.
Here’s the list of updates to the Azure portal this month:
Management
Networking
- Azure Private Link now generally available
- Azure Virtual Network service endpoint policies
- Virtual Network NAT (preview)
Security
- Container Image Vulnerability Assessment now generally available
- Integration with Azure Monitor alerts
- Improved just-in-time experience
- Deprecation of two recommendations for web applications
Intune
Let’s look at each of these updates in greater detail.
Management
RBAC custom role creation (preview)
We are happy to announce that you can now create, edit, or delete a custom role without ever leaving the Azure Portal. This capability was only available in the past using command line tools.
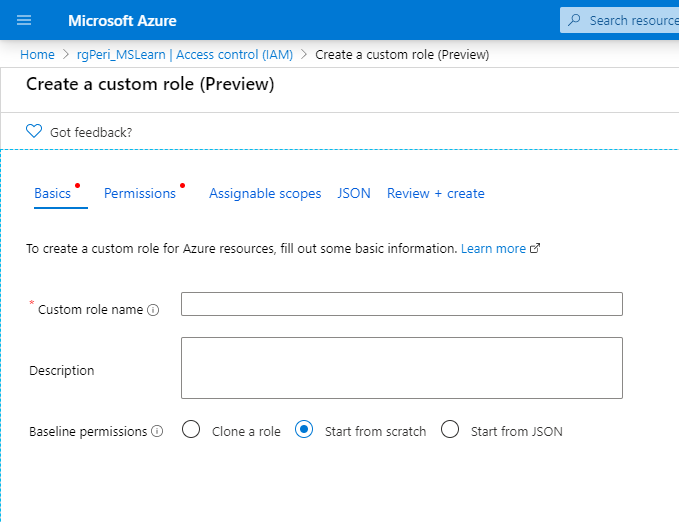
You can create a custom role by cloning an existing role, starting from scratch, or by starting with a JSON template.
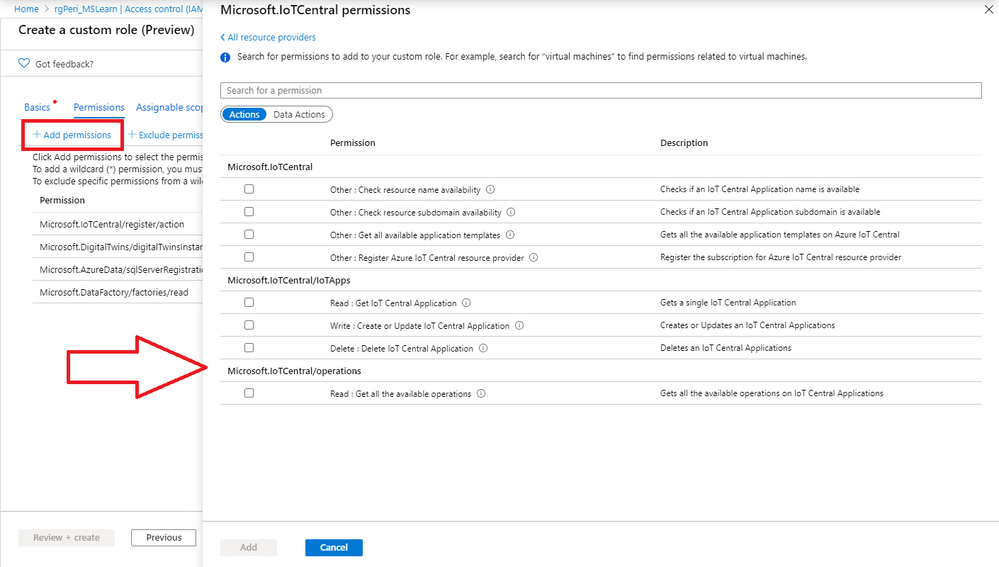
We’ve made it easy to add permissions to custom roles by using selectors.
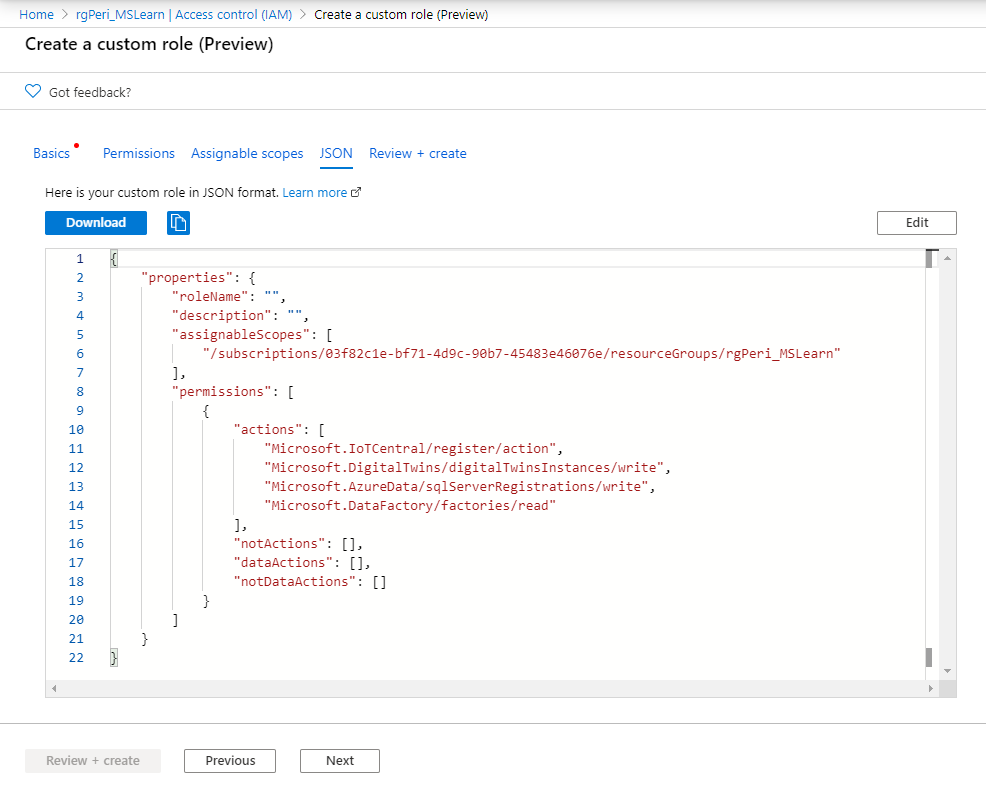
You can further edit your custom role using the JSON editor, or simply download it to use on CLI.
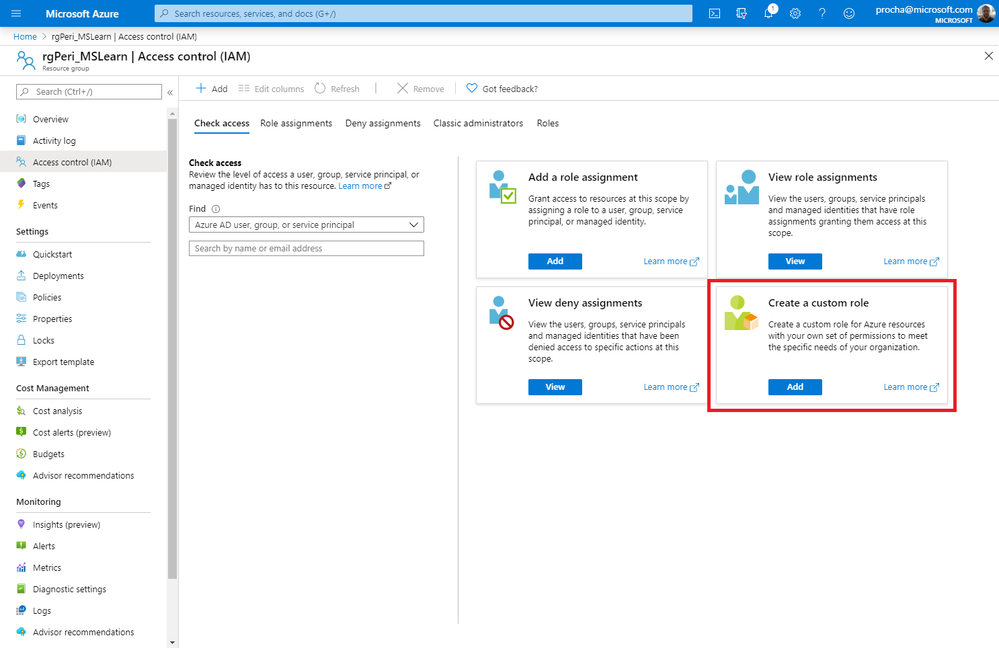
To try out custom RBAC roles:
- Go to a subscription or resource group
- Click Access control (IAM) on the resource menu
- Click Add under Create a custom role
Networking
Azure Private Link now generally available
Azure Private Link is a secure and scalable way for you to consume services (such as Azure PaaS, Partner Service, BYOS) on the Azure platform privately from within your virtual network.
Private Link landing page
You can learn more about Azure Private Link on this page.
To try out Azure Private Link:
- Click + Create a Resource
- In the Search the Marketplace box, type “Private Link”
- Select Private Link in the search results
Azure Virtual Network service endpoint policies
Azure Virtual Network service endpoint policies enable you to prevent unauthorized access to Azure Storage accounts from your virtual network. It enables you to limit access to only specific Azure Storage resources by applying endpoint policies over the service endpoint configuration.
This feature is now generally available in all Azure public regions. To learn more, visit this blog.
To try out service endpoint policies:
- Click + Create a resource
- In search pane, type "service endpoint policy" and select Service endpoint policy
- Select Create
Virtual Network NAT (preview)
Virtual Network NAT (network address translation) simplifies outbound-only Internet connectivity for virtual networks. When configured on a subnet, all outbound connectivity uses your specified static public IP addresses. Outbound connectivity is possible without load balancer or public IP addresses directly attached to virtual machines.
To learn more about Virtual Network NAT, visit this page.
Security
Container Image Vulnerability Assessment – General Availability
The vulnerability scanning (powered by Qualys) for container images stored in Azure Container Registry is now generally available.
Security Center’s image scanning parses the packages or other dependencies defined in the container image file, then checks for known vulnerabilities in those packages or dependencies.
Whenever you push an image to your registry, Security Center automatically scans that image. To trigger the scan of an image, push it to your container registry. When the scan completes (typically after approximately 10 minutes), findings are available in Security Center recommendations and included in the Secure Score together with information on how to remediate the issues and protect the vulnerable attack surface.
Integration with Azure Monitor alerts
Azure Security Center now supports integration with Azure Monitor alerts.
By leveraging Security Center's continuous export capabilities to Log Analytics Workspace, you can configure Azure Monitor Log Alert rules for recommendations and alerts exported from Security Center. They will then be reflected directly as alerts in Azure Monitor. You can also configure the alert rules to trigger an Action Group to enable automation scenarios supported by Azure Monitor.
Improved just-in-time experience
The features, operation, and UI for Azure Security Center’s just-in-time tools that secure your management ports have been enhanced as follows:
- Justification field – When requesting access to a VM through the just-in-time page of the Azure portal, a new optional field is available to enter a justification for the request. Information entered into this field can be tracked in the activity log.
- Automatic cleanup of redundant JIT rules – Whenever you update a JIT policy, a cleanup tool automatically runs to check the validity of your entire ruleset. The tool looks for mismatches between rules in your policy and rules in the NSG. If the cleanup tool finds a mismatch, it determines the cause and, when it's safe to do so, removes built-in rules that aren't needed any more. The cleaner never deletes rules that you've created.
Deprecation of two recommendations for web applications
The following two security recommendations related to web applications are being deprecated:
- The rules for web applications on IaaS NSGs should be hardened
(Related policy: The NSGs rules for web applications on IaaS should be hardened) - Access to App Services should be restricted
(Related policy: [Preview]: Access to App Services should be restricted)
These recommendations will no longer appear in Azure Security Center’s list of recommendations and their related policies will no longer be included in the ASC Default initiative.
Intune
Updates to Microsoft Intune
The Microsoft Intune team has been hard at work on updates as well. You can find the full list of updates to Intune on the What's new in Microsoft Intune page, including changes that affect your experience using Intune.
New videos on Azure portal “how to” video series
The following new videos are available to help you make the most out of the Azure portal:
- How to use Azure Monitor workbooks. Watch here.
- How to filter your resource list view. Watch here.
- How to use auto-refresh for dashboards. Watch here.
- Troubleshoot common virtual machine issues. Watch here
Have you checked out our Azure portal “how to” video series yet? The videos highlight specific aspects of the portal so you can be more efficient and productive while deploying your cloud workloads from the portal. Keep checking our playlist on YouTube for new videos.
Next steps
The Azure portal has a large team of engineers that wants to hear from you, so please keep providing us your feedback in the comments section below or on Twitter @AzurePortal.
Don’t forget to sign in the Azure portal and download the Azure mobile app today to see everything that’s new. See you next month!
