This post has been republished via RSS; it originally appeared at: SharePoint Support Blog articles.
Issue :
You are using Google Chrome 80, and when you have ADFS/SAML configured site, you notice that intermittently, users logging in fails and goes into a login loop.
The following error is received on ADFS :
"An error occured. Contact your administrator for more information"
Cause :
This behavior is because of Chrome’s new security feature :
A cookie associated with a cross-site resource at <URL> was set with the `SameSite` attribute. It has been blocked, as Chrome now only delivers cookies with cross-site requests if they are set with `SameSite=None` and `Secure`. You can review cookies in developer tools under Application>Storage>Cookies.
Ref: https://blog.chromium.org/2020/02/samesite-cookie-changes-in-february.html
Testing/Troubleshooting to understand the behavior :
- First test by passing any load balancer and check if you have the issue
- We need to collect a fiddler trace, and look for the frame in fiddler which is a GET request to the site, and in request header you will see that the ‘Fedauth’ cookie still exists.
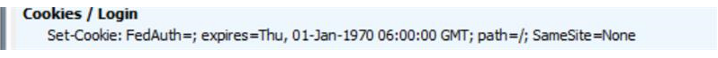
- This is the response from the server, a "Set-Cookie" Header, that sets the FedAuth to blank, this is because the user is browsing the site with an expired FedAuth cookie :
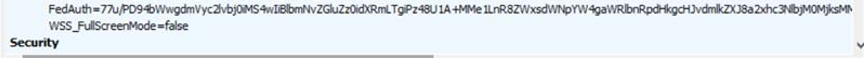
- Even after setting it to blank by SharePoint Server, Chrome does not deliver the blank Fedauth cookie(due to the same changes in it's cookie handling behavior), and in the next POST to the site it sends the same old expired cookie, you can see it in the request header in next request :
- When we use "Set-Cookie" to set theFedauth to blank, we also see the ‘SameSite=None’ attribute, but Chrome will deliver the cookie only if it has ‘SameSite=None’ alongwith ‘Secure’ attribute
Resolution :
Step 1 -- Recommendations by Microsoft
Ref: https://docs.microsoft.com/en-us/office365/troubleshoot/miscellaneous/chrome-behavior-affects-applications
Microsoft customers who use Active Directory Federation Services (AD FS) or Web Application Proxy must deploy one of the following Windows Server updates:
|
Product |
KB Article |
Release Date |
|
Windows Server 2019 |
January 14, 2020 |
|
|
Windows Server 2016 |
January 14, 2020 |
|
|
Windows Server 2012 R2 |
January 14, 2020 |
The following Microsoft server or client products must also be updated. The updates will be added to this article when they're available. We recommend that you revisit this article regularly for the latest updates.
|
Product |
KB Article |
Release Date |
|
Exchange Server |
|
March 2020 Cumulative Update |
|
Project Server 2013 |
March 10, 2020 |
|
|
Project Server 2010 |
March 10, 2020 |
|
|
SharePoint Foundation 2013 |
(Cumulative Update: KB 4484278)1 |
March 10, 2020 |
|
SharePoint Foundation 2010 |
March 10, 2020 |
|
|
SharePoint Server 2019 |
February 11, 2020 |
|
|
SharePoint Server 2016 |
March 10, 2020 |
|
|
SharePoint Server 2013 |
March 10, 2020 |
|
|
SharePoint Server 2010 |
March 10, 2020 |
This Cumulative Update contains the fix for the SameSite cookie issue, plus additional fixes unrelated to the SameSite cookie issue. Microsoft recommends installing the Cumulative Update rather than the individual update to ensure your environment has all of the fixes available at the time the Cumulative Update was released.
Reference : https://docs.microsoft.com/en-us/office365/troubleshoot/miscellaneous/chrome-behavior-affects-applications
Step 2 -- If you still see issue continues after March 2020 CU update
If you still see issues with Load Balancer in place, you will have to contact your load balancer vendor for having an iRule created to add the SameSite=None and Secure parameter in the "Set-Cookie" header.