This post has been republished via RSS; it originally appeared at: SQL Server articles.
Set up an Azure Active Directory service principal using the Azure Portal
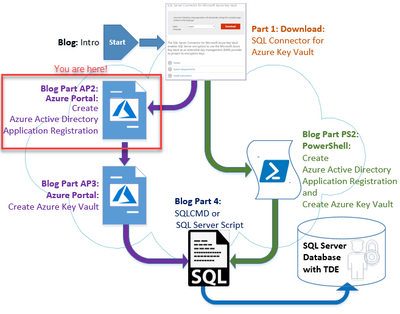
This is Part: AP2 (Azure Portal) of a 4-part blog series:
This blog in the series provides the step-by-step instructions to configure Azure Active Directory using the Azure Portal.
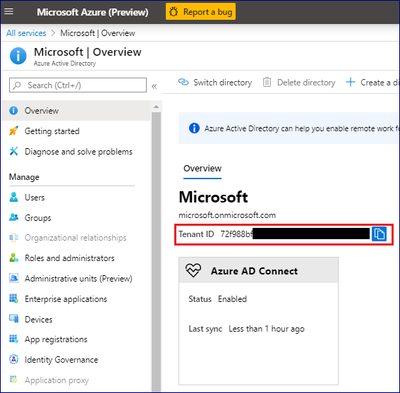
To grant SQL Server access permissions to your Azure Key Vault, you will need a Service Principal account in Azure Active Directory (AAD).
- Go to the Azure Portal, and sign in.
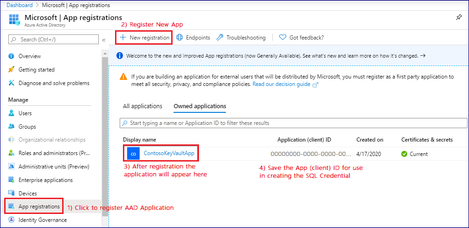
- Register an application with Azure Active Directory (AAD).
3. Copy the Application (Client) ID and Client Secret for a later step, where they will be used to grant SQL Server access to your key vault.
a) Step 1: Click on “App registrations” Node
b) Step 2: Create a ”+ New Registration”
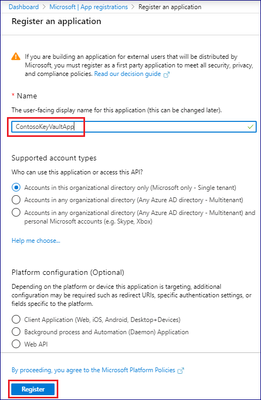
4. Registering the AAD application
a) Step 1: While registering the AAD application, enter a Name.
b) Step 2: You can leave all the additional options as default
i) i.e.: “Accounts in this organizational directory only (Microsoft only - Single tenant)”
c) Then click the “Register” button.
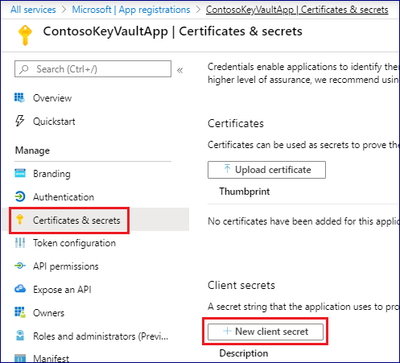
5. Certificates & secrets
a) Step 1: Next click the “Certificates & secrets” node:
b) Step 2: Then Create a “+ New client secret”
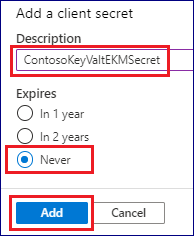
c) Step 3: Click on the “+ New client secret” button (expiration as appropriate) then "Add"
d) Step 4: Next enter a Description
e) Step 5: Select an “Expiration” value (i.e: Never)
f) Step 6: Click “Add”
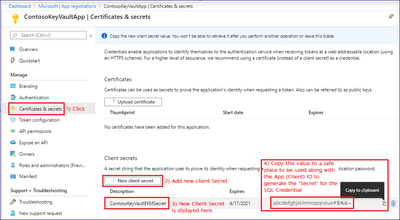
6. Save the Secret
a) Step 4: Copy and save the Secret Value along with the Application (Client) ID to be used in TSQL (to be used by SQL Server for Secret in the Credential) – this is a long string of letters, numbers and special characters that will not be visible in the Azure Portal after some time.
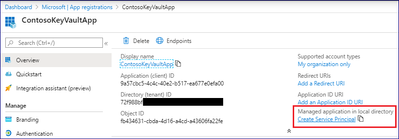
7. Create the Azure Active Directory Service Principal
a) Step 1: Click on the “Create Service Principal” link.
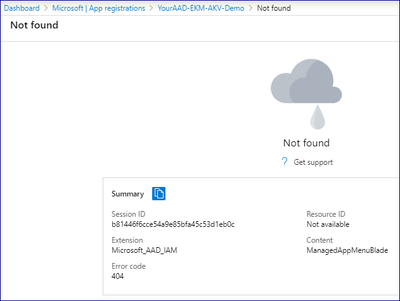
8) After clicking the “Create Service Principal”
a) the Portal may show “Not Found” – this is OK as the Service Principal was created in the background and there appears to be a bug in the portal that we are working on getting resolved.
9. Properties
a) Once the AD Service Principal is created, you will see this blade if you re-click on “Managed application in local directory” in the previous step.
Conclusion
Configuring Azure Active Directory is the second step in configuring SQL Server TDE to use Azure Key Vault. Continue the setup process for SQL Server using SSMS or SQLCMD.
See you at the next blog (Part: AP3)
Adrian
Next steps
| SQL Server Transparent Data Encryption and Extensible Key Management Using Azure Key Vault – Intro | |
|
SQL Server Connector for Microsoft Azure Key Vault (aka: SQL Server Connector) – Part: 1 |
|
|
Azure Portal Method |
PowerShell Method |
|
Set up an Azure Active Directory Service Principal – Part: AP2 (this document) |
Setup Azure Active Directory Service Principal and Azure Key Vault (one script) – Part: PS2 This script combines Part: AP2 & Part:AP3 |
|
Create an Azure Key Vault – Part: AP3 |
|
|
Configure SQL Server TDE EKM using AKV – Part: 4 |
|