Azure Event Hubs flavors multi-tenant offering and single-tenant Dedicated Event Hubs clusters. This single-tenant offering guarantees 99.99% SLA while letting you ingress in GB’s per second with guaranteed capacity and sub-second latency. Customers love the high-scale, low-latency capabilities that Dedicated Event Hubs clusters offer. Along with this rapid adoption of Azure, customers also want to access the data and services securely and within private network boundaries. We have been incrementally adding support for network isolation through VNet Service Endpoints and Firewall rules. Today we are extending this support and are excited to announce the GA of Azure Private Link support for Azure Event Hubs. Private Link support is available for both Standard and Dedicated SKU’s of Event Hubs.
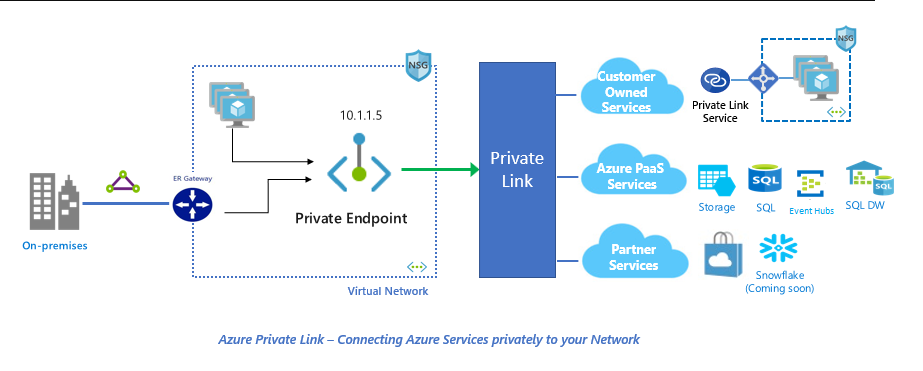
Azure Private Link enables you to access Azure PaaS Services (like Azure Event Hubs) and Azure hosted customer/partner services over a Private Endpoint in your virtual network. Traffic between your virtual network and the service traverses over the Microsoft backbone network, eliminating exposure from the public Internet. You can also create your own Private Link Service in your virtual network (VNet) and deliver it privately to your customers. The setup and consumption experience using Azure Private Link is consistent across Azure PaaS, customer-owned, and shared partner services. The technology is based on a provider and consumer model where the provider and the consumer are both hosted in Azure. This also simplifies the network configuration by keeping access rules private
Note: While VNet Service Endpoints provides a way to lockdown access to PaaS resources to a virtual network, this still accesses a public endpoint. With service endpoints you are locking down access to a particular service and not to the resource itself.
Below are a couple of benefits that Azure Event Hubs support to private link provides:
- A private IP for your PaaS resources – Since PaaS resources are mapped to private IP addresses in the customer’s VNet, they can be accessed via Azure ExpressRoute private peering. This effectively means that the data will traverse a fully private path even from on-premises to Azure. The configuration in the corporate firewalls and route tables can be simplified to allow access only to the private IP addresses.
- Traffic to PaaS resources now traverse through the Microsoft network – Traffic between your virtual network and the service travels the Microsoft backbone network. Exposing your service to the public internet is no longer necessary.
- Restricted user access to a specific resource – Azure Private Link is unique with respect to mapping a specific PaaS resource to private IP address as opposed to mapping an entire service as other cloud providers do. This essentially means that any malicious intent to exfiltrate the data to a different account using the same private endpoint will fail, thus providing built-in data exfiltration protection.
- Private endpoints can be created to resources in different region and even different tenants – Connect privately to services running in other regions. The consumer’s virtual network could be in region A and it can connect to services behind Private Link in region B.
How to setup private link for Azure Event Hubs
To learn more about how to setup Azure Private Links for Azure Service Bus using PS the Azure Portal, please refer to the below documentation.
- Integrate Azure Event Hubs with Azure Private Link
- Learn more about Azure Private Link
- Learn more about Event Hubs Dedicated clusters
- Have questions? Email us at askeventubs@microsoft.com
- Have comments? We would love to hear from you, please leave your comments below.