There are some use cases in the SIEM (Security Information and Event Management) world that require correlation with alerts from an expert system like Office 365 Advanced Threat Protection (ATP). Now you can use the built-in data connector to collect alerts from Office 365 Advanced Threat Protection into Azure Sentinel.
Office 365 Advanced Threat Protection (ATP) safeguards your organization against malicious threats posed by email messages, links (URLs) and collaboration tools. By ingesting Office 365 ATP alerts into Azure Sentinel, you can incorporate information about email and URL based threats into your broader risk analysis and build response scenarios accordingly.
The following types of alerts are supported with the data collector:
- A potentially malicious URL click was detected
- Email messages containing malware removed after delivery
- Email messages containing phish URLs removed after delivery
- Email reported by user as malware or phish
- Suspicious email sending patterns detected
- User restricted from sending email
These alerts can be seen by Office 365 customers in the Office Security and Compliance Center as well.
The Office 365 ATP data connector in Azure Sentinel uses the Automated Investigation and Response API and ingest only alerts which are triggered by automatic investigation in Office 365 ATP.
This blog post covers the required steps to ingest Office 365 ATP alerts into sentinel and how to use the ingested alerts.
How to Enable Office 365 ATP alert ingestion in Azure Sentinel
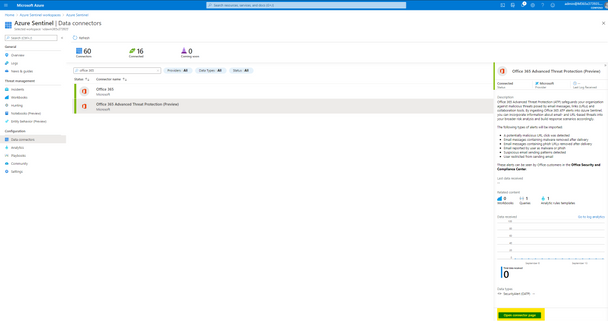
From the Azure Sentinel navigation menu, select Data connectors.
Select Office 365 Advanced Threat Protection (Preview) data connector, and then select Open Connector Page on the preview pane.
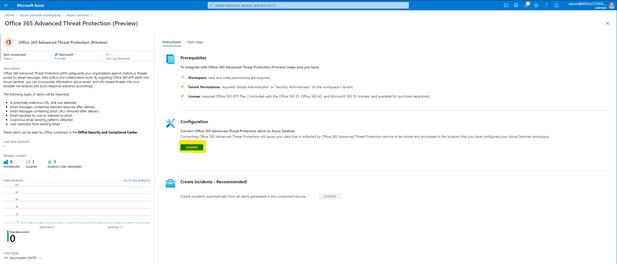
On the Office 365 Advanced Threat Protection (Preview) page, under Configuration select Connect.
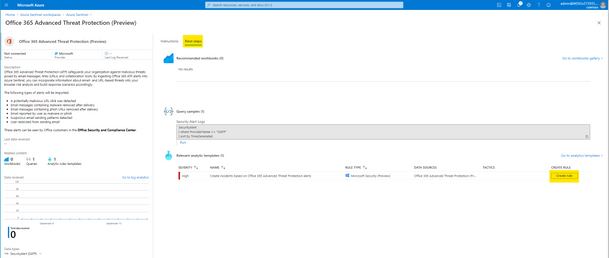
Select Next Steps and Create rule to enable and make adjustments for the relevant analytic rule template.
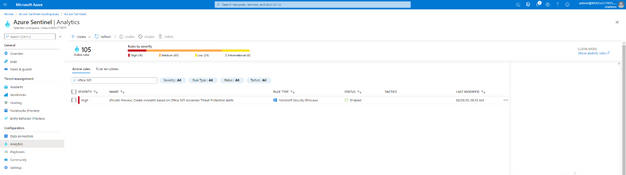
After successfully activation you will see the rule in your Active rules list in the Analytics page. This rule will make sure that all alerts generated by Office 365 ATP will also trigger an Incident in Azure Sentinel.
Now the Office 365 ATP alerts from your Office 365 tenant will be ingested into Azure Sentinel workspace and any generated alert in Office 365 ATP will also trigger an Incident in Azure Sentinel.
GIF Demonstration – How to enable the Office 365 ATP data connector
How to Use this Data
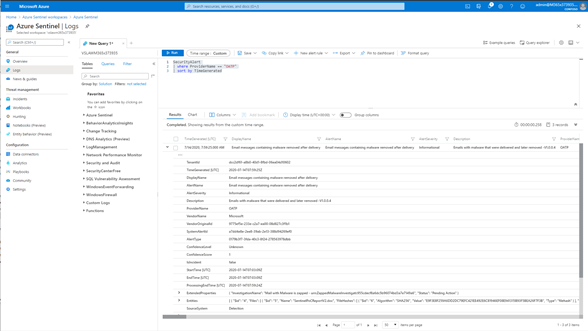
Once the data connector is functional you can query the Office 365 ATP alerts. The Office 365 ATP alerts will reside in the SecurityAlert table in Azure Sentinel workspace.
The following example query looks for the generated alerts for Office 365 ATP in Azure Sentinel.
SecurityAlert
| where ProviderName == “OATP”
| sort by TimeGenerated
GIF Demonstration – Query Office 365 ATP alerts in Azure Sentinel
GIF Demonstration – Sample Office 365 ATP Incident in Azure Sentinel
Summary
In this post I have shown how you can onboard Office 365 ATP alerts into Azure Sentinel and sample query how to use the data.
You can also contribute new connectors, workbooks, analytics and more in Azure Sentinel. Get started now by joining the Azure Sentinel Threat Hunters GitHub community and follow the guidance.