This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
October is my favorite time of year, between the change of season, Major League Baseball playoffs, and with football underway. It’s also National Cybersecurity Awareness Month, though with so many cyberattacks and incidents in the news, one month of dedicated focus hardly seems sufficient. For that reason, we will continue to invest heavily in SCI management technologies that work across, not just your Microsoft investments, but that also extends to your third-party technology systems.
I’ll start with interoperability. Your environment will no doubt remain hybrid, with multiple providers mutually committed to supporting your digital transformation efforts. Of all the made at IGNITE, two are most indicative of our commitment to deliver world-class security technologies in conjunction with other market partners, in increasingly critical segments:
- Microsoft and FireEye/Mandiant announced a partnership to combine Microsoft’s security products and technologies with Mandiant’s on-the-ground expertise in incident response and threat intelligence; our companies will partner in incident response and SecOps. This is a great example of our willingness to partner and work with security companies across the globe; we may well compete in some areas, but in the end this community of practice is dedicated to protecting our users. Look here for more information on the Microsoft Intelligent Security Association.
- Our security investments and partnerships by no means are limited to traditional IT management; we’re very much focused on operational technologies as well. Microsoft and AT&T announced a new joint cellular guardian device solution built on Azure Sphere, which will advance secure cellular connections with lower operating costs.
- Another important management offering that advances interoperability is , which enables cross-customer management capabilities, allowing a partner or service provider, or large organizational authority, to consolidate and centralize management and visibility of disparate resources.
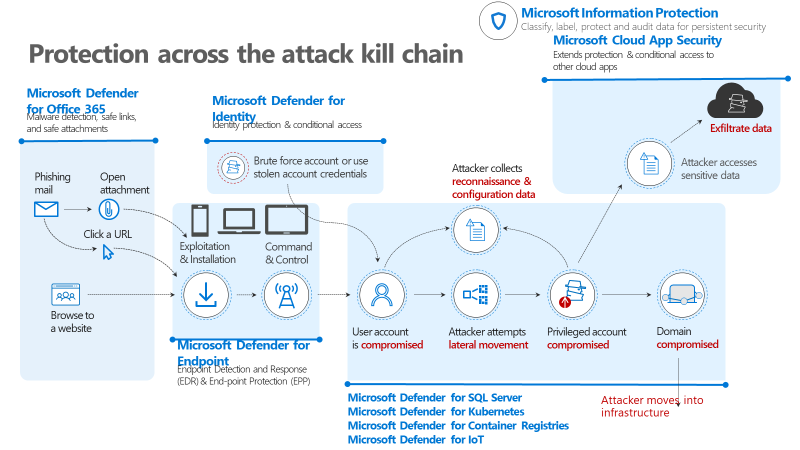
Other updates coming out of IGNITE include a rebranding of sort of our threat protection portfolio: Microsoft Defender is a combined set of offerings, combining Microsoft 365 Defender and Azure Defender, protecting and responding to threats across an attacker kill chain, from identities to endpoints, applications, email, infrastructure and cloud. Thinking left to right, through an attacker lifecycle, this is how our “Microsoft Defender” suite works:
- Microsoft Defender for Office 365 complements standard Office 365 gateway and anti-spam capabilities with additional pre-breach protections for user accounts, especially those that might be most visible and therefore attractive to attackers via spear- or whale-phishing. This capability uses isolated detonation “sandboxing” technologies to analyze incoming attachments and URLs.
- Microsoft Defender for Endpoint functions as both a pre- and post-breach management and detection tool for not only your Windows devices but iOS and Android. The service’s Threat and Vulnerability Management capabilities help protect your environment from attack by staying current on configurations; and it provides post-breach management by giving your analysts the ability to isolate a compromised endpoint, force authentication, take a forensics image, and respond to the attacker.
- Microsoft Defender for Identity offers user entity behavior analysis protections for credentials and provides link analysis insight into victims’ relationships and interactions with other users. This helps your analyst teams understand, respond to, and get ahead of threats to user groups.
- Azure Defender extends Azure Security Center’s cloud security posture management capabilities with important new capabilities:
- Defender for SQL Server.
- Azure Defender for Kubernetes.
- Azure Defender for Container Registries.
- Azure Defender for IoT is an exciting new offering as part of our recent acquisition of CyberX labs. This extends IT protection to your OT/connective device environment. As we expect to see more attacks against physical devices, for example ransomware, this is an important development.
- Azure Sentinel is an OpEx SIEM/SOAR service that manages not only your Microsoft investments, but many third-party ones as well. Sentinel now offers UEBA insights to assist with SecOps.
Here’s a view:
Figure 1: Illustration of Microsoft Defender protection across attack kill chain
Microsoft continues to update and consolidate this suite of offerings to help you centralize and automate more of your security operations, taking advantage of the scale and cost benefits that Cloud can bring. We will continue to integrate our technologies internally and will continue to partner with others around the security community, to protect our customers. One final example, an important resource for partners and customers alike, is this GitHub repository for security operations defenders. Start here to find log analysis queries, sample data sets, SDKs, scripts, connectors, and other resources to accelerate your work. More importantly, use this as an opportunity to join a community of practice , a network of defenders who are working across industries and geographies to protect users, systems, and data.
This being National Cybersecurity Awareness month, I’ll close with a link to a blog that I recently published, with advice on how to accelerate your cybersecurity career and make immediate impact by using default security tools. We and many other security providers remain committed to defending our users and the ecosystem, but we humans, the 8th OSI layer, implement these technologies and solutions. The more we can “move left” and build basic hygiene tools INTO what we deliver and help you implement, the more secure and productive we will be.