This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
A common question we get from organizations that use Microsoft Information Protection is, how can we receive a single pane of glass across not only DLP and other information protection events but correlate with the entire IT estate? How can I effectively use the richness of data for incident management and reporting?
In this post we will focus on how this can be achieved with Azure Sentinel, by utilizing a custom Azure Function for ingestion. Let's start with a few teasers.
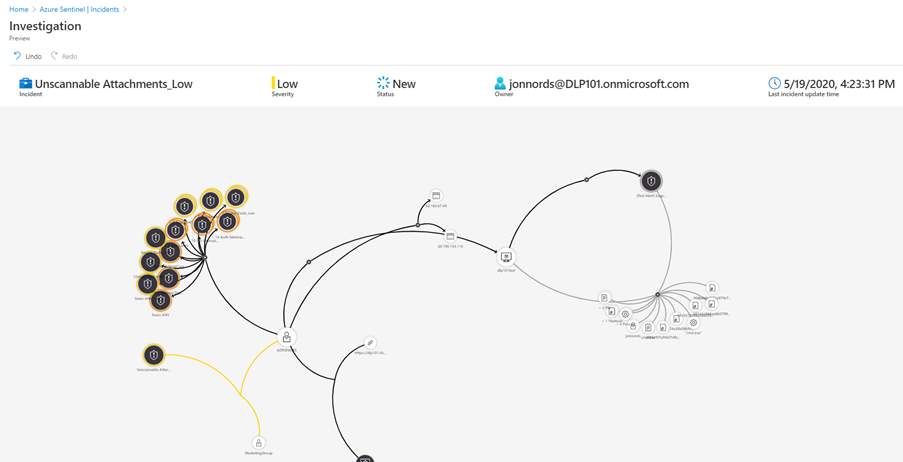
Below is a sample where an Office DLP incident is connected with other incidents as well as the Microsoft Defender for Endpoint alerts from the device. Over time this native Azure Sentinel feature will evolve to support more entities for automated correlation.
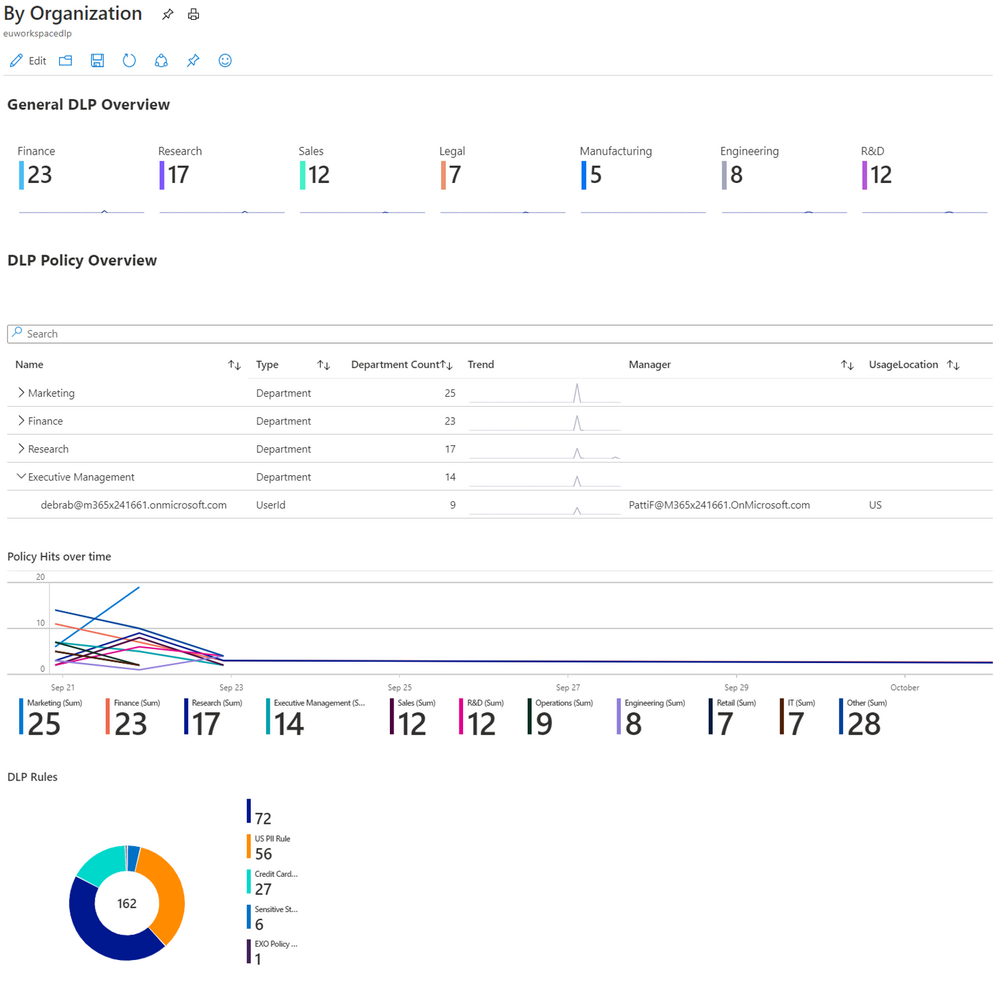
This is a Workbook sample of reporting of DLP incidents across departments and geography.
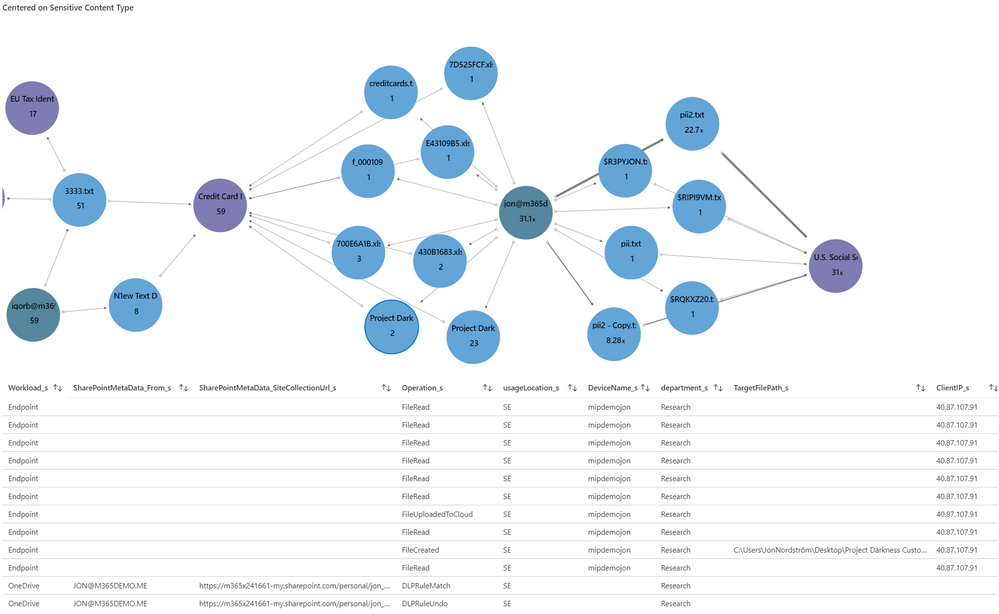
In this GRAPH sample using an Workbook, we have selected a document node (Darkness), which expands a table with SharePoint DLP alerts as well as SharePoint Activity for that document to instantly go deeper in the investigation.
The code and instructions for ingestion of Endpoint and Office DLP events can be found here, https://github.com/OfficeDev/O365-ActivityFeed-AzureFunction/tree/master/Sentinel/EndPointDLP_preview (Although the naming is endpoint it includes both Office and Endpoint data). Please note that the code for endpoint will change as soon as the endpoint DLP events are included in dlp.all.
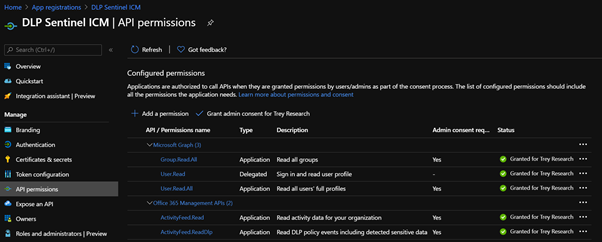
- Register a new application in Azure AD https://docs.microsoft.com/en-us/azure/active-directory/develop/quickstart-register-app
- Microsoft GRAPH (Application permissions)
- Group.Read.All
- User.Read.All
- Office 365 Management APIs (Application permissions)
- ActivityFeed.Read
- ActivityFeed.ReadDlp (Needed for detailed DLP events)
- Microsoft GRAPH (Application permissions)
- Collect the identity and secret for the new App created in step 1. For production, store the secret in Azure Key vault https://docs.microsoft.com/en-us/azure/app-service/app-service-key-vault-references, generate the keys now delegate access to the function in step 7.
- clientID
- clientSecret
- TenantGuid
- exuser (User account to allow for mapping to sensitive info types, it should only have the permissions to run Get-DlpSensitiveInformationType)
- Azure Sentinel Workspace Name
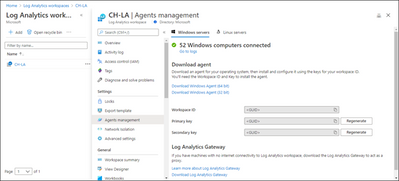
- Get the WorkSpace ID and Workspace Key for your Sentinel Workspace.
- Select the workspace from the Log Analytics workspaces menu in the Azure portal. Then select Agents management in the Settings section.
- Select the workspace from the Log Analytics workspaces menu in the Azure portal. Then select Agents management in the Settings section.
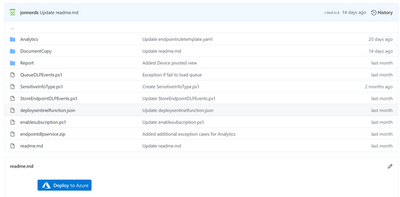
- Click deploy to Azure in the repo https://github.com/OfficeDev/O365-ActivityFeed-AzureFunction/tree/master/Sentinel/EndPointDLP_preview
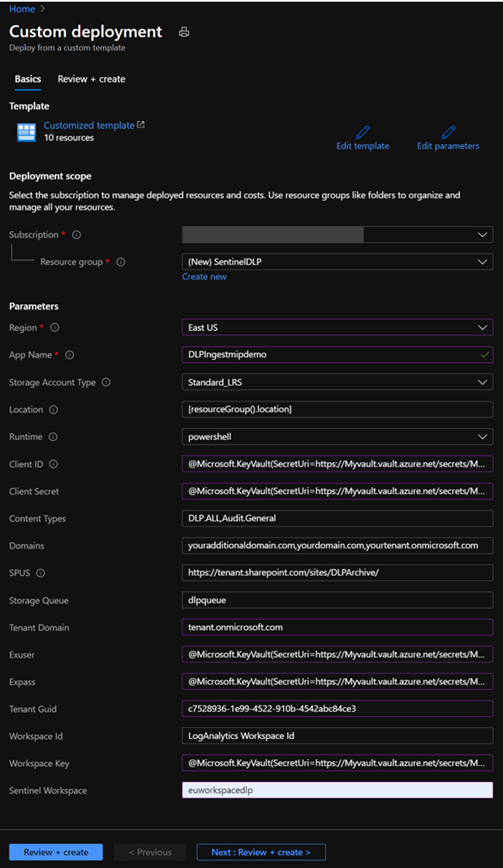
- Provide the parameters needed for the function.
- SPUS is only used if you are going to deploy ingestion of emails to SharePoint to be able to retrieve a full copy of the emails from the incidents.
- Click Review and create
- Click Create, if all parameters passed
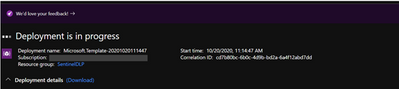
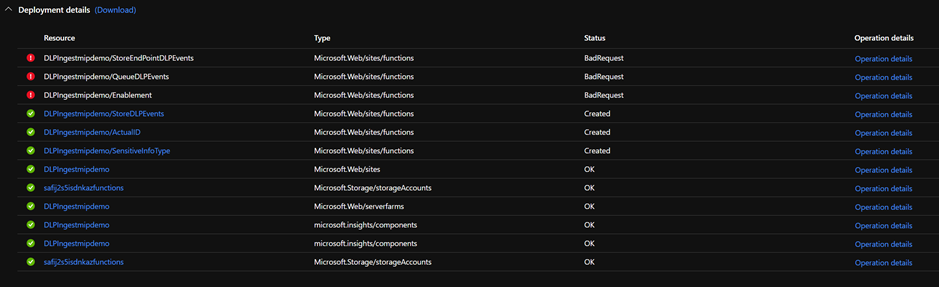
- The Deployment will start
- On completion it is likely that several of the functions will have an error. The actual function code is deployed in the next step so the errors are expected.
- SPUS is only used if you are going to deploy ingestion of emails to SharePoint to be able to retrieve a full copy of the emails from the incidents.
- Go to the Resource Group where you deployed the app, you will see the core services deployed. Click the Function App, we will come back here in a moment
- To enable the app to automatically synch DLP policies to Sentinel run the following commands it will allow the APP to fully manage Sentinel. You need to define the RG where the Log Analytics database is hosted for Sentinel.
- Start Powershell and ensure that the Az module is installed.
- $id = (Get-AzADServicePrincipal -DisplayNameBeginsWith YourAPP).id
- New-AzRoleAssignment -ResourceGroupName YOURRGWITHSENTINEL -RoleDefinitionName "Azure Sentinel Contributor" -ObjectId $id
- You can use the UI as well under Identity of the function, this process can also be used granting access to your key vault on completion of the setup of the function.
- Deploy the code used for the functions.
- Download the deployment zip (endpointdlpservice.zip )
- Start Powershell and ensure that the Az module is installed.
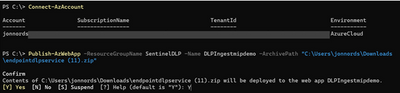
- Connect-AzAccount
- Run Publish-AzWebApp -ResourceGroupName REPLACEWITHYOURRG -Name REPLACEWITHYOURAPPNAME -ArchivePath C:\path\enpointdlpservice.zip
- To initialize the variables in the app
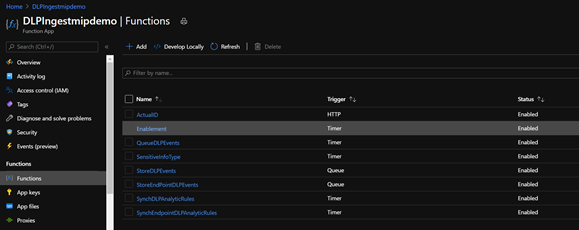
- Navigate to the Enablement function in your Function App
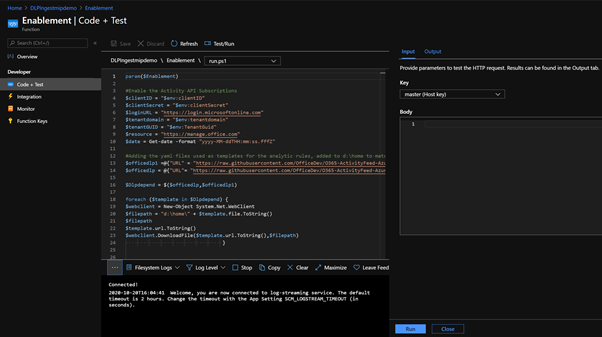
- open the function under functions, open "Code + Test" , click Test/Run, click Run
- Navigate to the Enablement function in your Function App
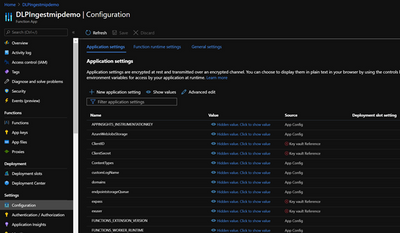
- Note if there are any errors generated in this run, you will see it in the logging window. If there is a typo or similar in your configuration files. Go back to the main window for the App and click Configuration to update the parameter
- Note, the Analytic Rules functions will not be successful until you have ingested both SharePoint, Exchange events and in the case of Endpoint you need Endpoint events.
- The API actively refuses queries that are in-valid.
- If the Log Analytic rules that corresponds to DLP Policies aren't created after data ingestion, run the Enablement function again. It will reset the time scope of the functions.
- If you want to ingest original email content to SharePoint please see https://github.com/OfficeDev/O365-ActivityFeed-AzureFunction/tree/master/Sentinel/logicapp.
- To setup the reporting please follow
- https://github.com/OfficeDev/O365-ActivityFeed-AzureFunction/tree/master/Sentinel/EndPointDLP_preview/Report
- EndPoint DLP
- https://github.com/OfficeDev/O365-ActivityFeed-AzureFunction/tree/master/Sentinel/Report
- Exchange & Teams DLP Report
- SharePoint & OneDrive DLP Report
- Organization Reporting
- https://github.com/OfficeDev/O365-ActivityFeed-AzureFunction/tree/master/Sentinel/EndPointDLP_preview/Report
- If you want to try out ingestion of documents from endpoints look at this https://github.com/OfficeDev/O365-ActivityFeed-AzureFunction/tree/master/Sentinel/EndPointDLP_preview/DocumentCopy
- In the repo see the "Important Additional Customization"
Summary
This is just a starting point to get DLP incident data in to Azure Sentinel. There is enrichment code to add details from Microsoft GRAPH that can be customized. You can customize the code to send events to different Azure Sentinel Workspaces based on geography and other details. In Azure Sentinel you can start to create automated actions using Playbooks, you can create your own Kusto queries to receive new insights. More on that in a later post. And yes, we are investigating the option to provide native integration with Azure Sentinel as well.