This post has been republished via RSS; it originally appeared at: Azure Active Directory Identity Blog articles.
Howdy folks,
It’s awesome to hear from many of you that Azure AD Application Proxy helps you in providing secure remote access to critical on-premises applications and reducing load from existing VPN solutions. We’ve also heard about the need for Application Proxy to support more of your applications, including those that use headers for authentication, such as Peoplesoft, NetWeaver Portal, and WebCenter.
Today we’re announcing the public preview of Application Proxy support for applications that use header-based authentication. Using this preview, you can benefit from:
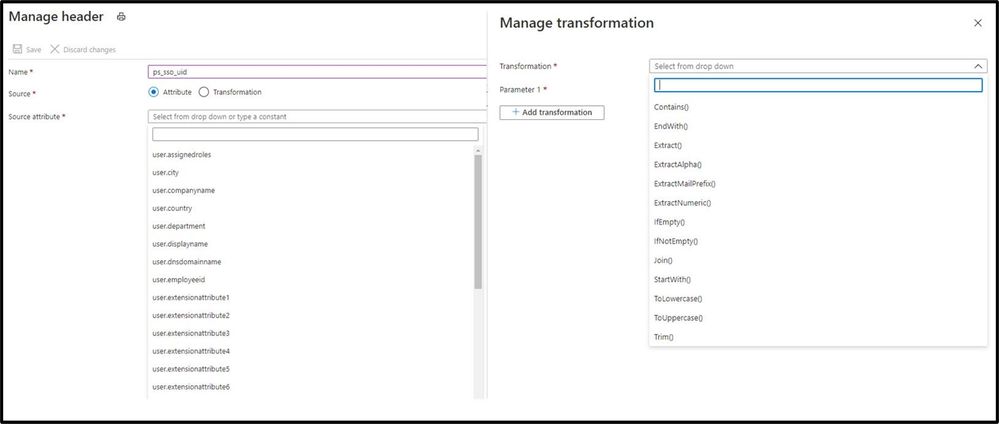
- Wide list of attributes and transformations for header based auth: All header values available are based on standard claims that are issued by Azure AD. This means that all attributes and transformations available for configuring claims for SAML or OIDC applications are also available to be used as header values.
- Secure and seamless access: These apps benefit from all the capabilities of Application Proxy, including single sign-on as well as enforcing pre-authentication and Conditional Access policies like requiring Multi-Factor Authentication (MFA) or using a compliant device before users can access these apps.
- No changes to your apps are needed: You can use your existing Application Proxy connectors and no added software needs to be installed.
Thanks to all the customers who have provided feedback in developing this capability. Here’s what one customer had to say about their experience using Application Proxy for their header-based authentication:
“App Proxy header-based auth support allowed us to migrate our header-based workloads to Azure AD, moving us one step closer to a unified view for application access and authentication. We have been able to retire our 3rd party header-based auth tools and simplify our SSO landscape. And it’s saved us a small fortune! Thank you.” – Barney Delaney, IAM Architect, Mondelez
Getting started
To connect a header-based authentication application to Application Proxy, you’ll need to make sure you have Application Proxy enabled in your tenant and have at least one connector installed. For steps on how to do install a connector, follow our tutorial here.
- First add a new application and configure Application Proxy for remote access by filling out the fields:
- Name: Display name for the application
- Internal URL: The URL used to access the application from inside your private network. This can be at the root path of the app or as granular as needed.
- External URL: The URL used to access the application remotely from the internet.
- Pre-authentication: Set to Azure Active Directory which ensures that all users must authenticate to access the app and Conditional Access policies are enforced.
- Connector Group: Select the connector group with line of site to the application.
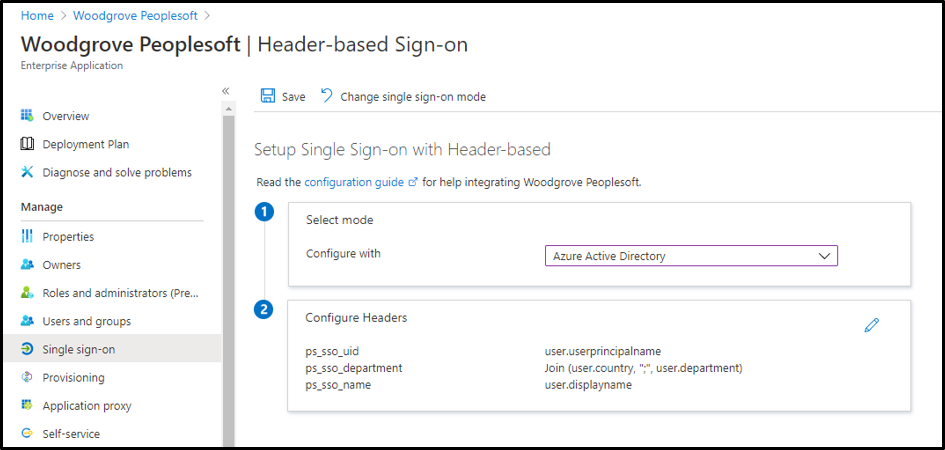
- Enable header-based authentication as the single sign-on mode for the application. You can configure any attribute synced to Azure AD as a header. You can also use transformations to craft the exact header value the application needs.
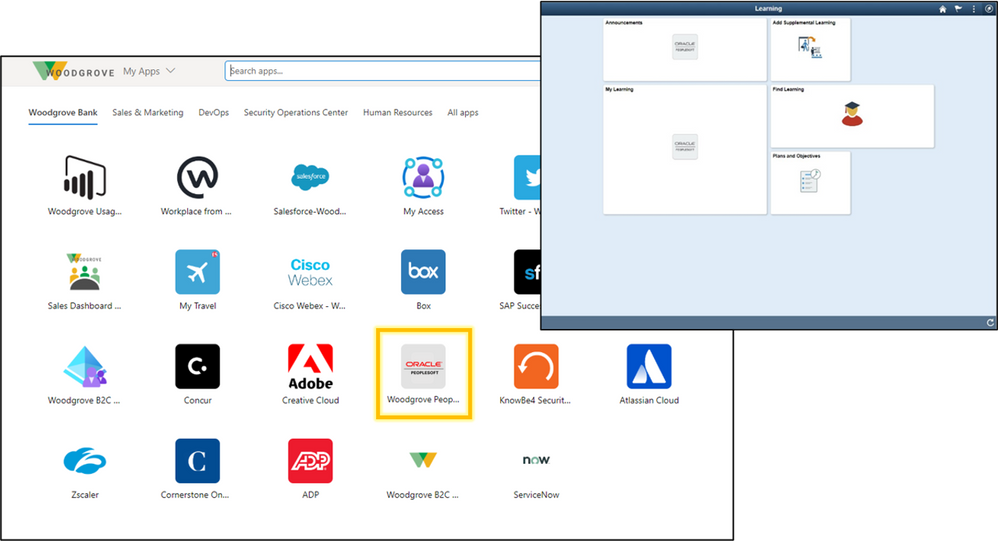
- After configuration, the app can now be launched from the My Apps portal just like any other cloud application or directly via the external URL.
In just a few steps, you've enabled the app for remote access from any browser or device, enabled single sign-on for header-based authentication, and protected the app with any Conditional Access policies you've assigned to the app. To learn more, check out our technical documentation.
Making it easier to connect your header-based authentication applications to Azure AD is just another step we are taking to helping you secure and manage all the apps your organization uses. We are excited to keep releasing new functionality and updates to make this journey even easier based on your feedback and suggestions.
As always, we’d love to hear from you. Please let us know what you think in the comments below or on the Azure AD feedback forum.
Best regards,
Alex Simons (twitter: @alex_a_simons)
Corporate Vice President Program Management
Microsoft Identity Division