This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Last week at Ignite, we announced the public preview of URL detonation in Azure Sentinel. This blog post provides more details on its benefits and how to enable it.
Security operations center (SOC) analysts constantly face the challenge of determining where to focus. URL detonation provides insights that can enable SOC analysts to triage alerts faster. For example, logs ingested by Azure Sentinel can contain URLs. For alerts that include a URL (e.g., a URL visited by a user from within the corporate network), that URL can be automatically detonated to gain added insight that can help accelerate the triage process.
With Azure Sentinel, URL detonation is built-in and is seamlessly integrated, eliminating the need to stitch together separate SIEM and detonation products.
The sections that follow provide a step-by-step overview of how to enable integrated URL detonation.
Enabling URL detonation
When creating scheduled alert rules, any URL data in the query results can be mapped to the newly available URL entity type. Whenever an alert containing a URL fires, the mapped URL is automatically detonated, and the investigation graph is immediately enriched with the detonation results.
Mapping URL entities
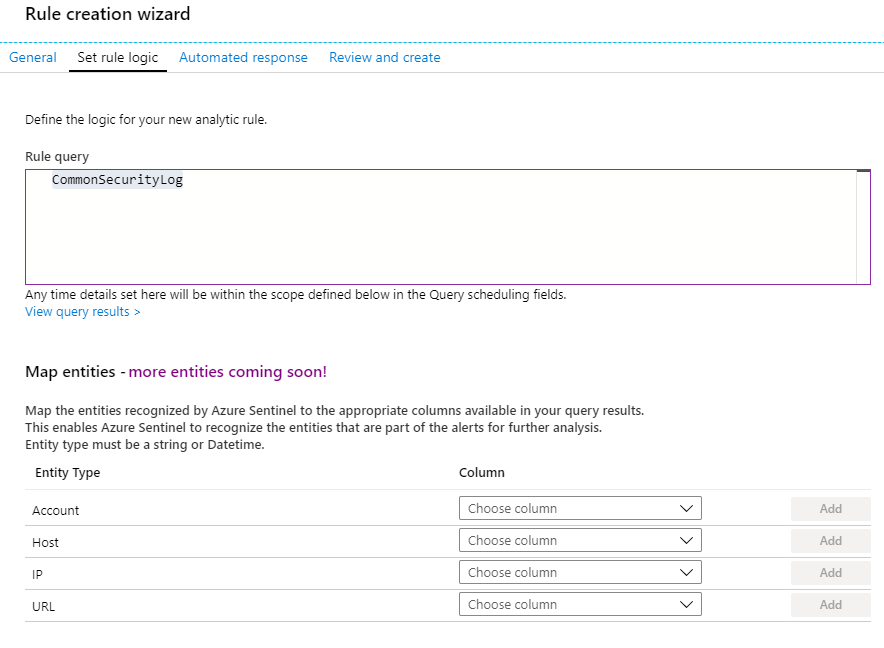
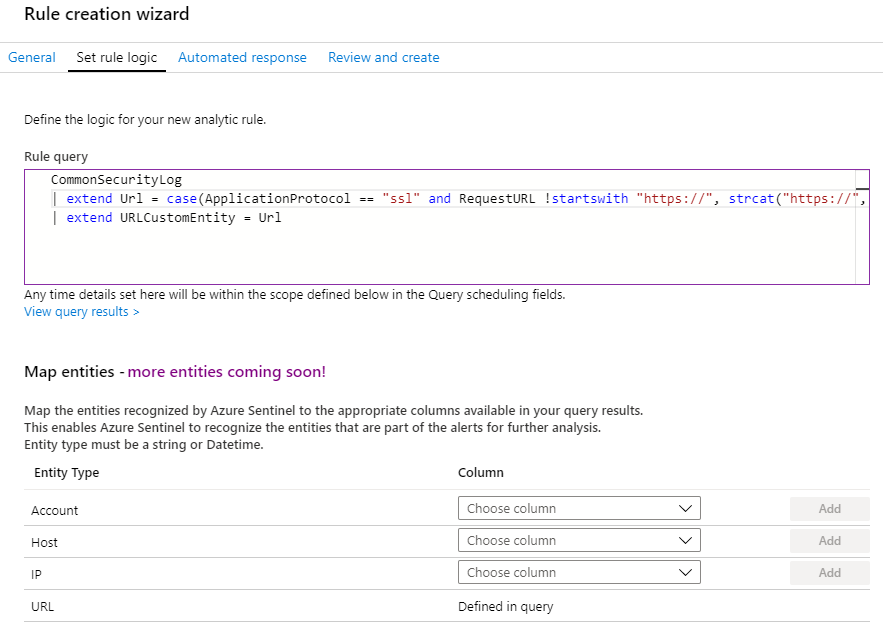
To map URLs from logs to the URL entity type, navigate to the Analytics blade. At the top of blade, click +Create and select Scheduled query rule to navigate to the Rule creation wizard. Click Set rule logic. In the Rule query field, you can reference any log that contains a column of URLs. We’ll illustrate this by entering “CommonSecurityLog” in the Rule query field. After entering “CommonSecurityLog”, you’ll notice that the Choose column drop down for the URL entity type in the Map entities section is enabled.
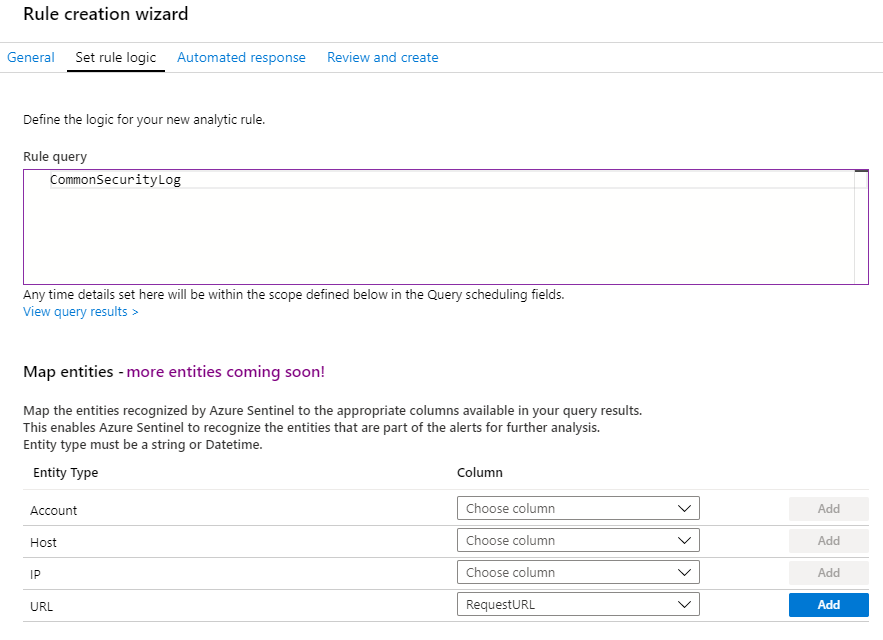
In “CommonSecurityLog”, there is a column called “RequestURL” that contains URLs. To map this column to the URL entity type, select it in the Choose column drop down and click Add.
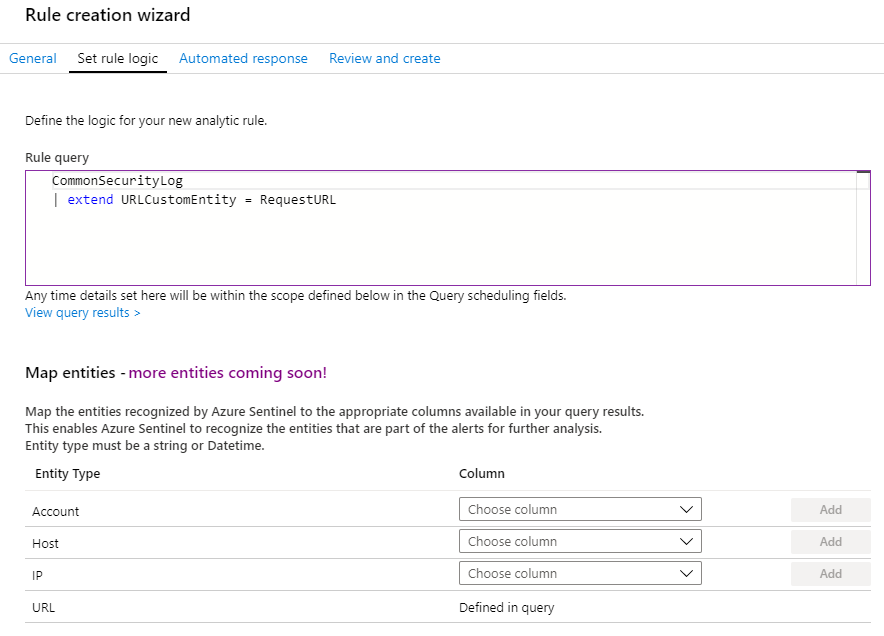
Once the column is added, the following code is automatically added to your Rule query. It maps the column of interest to the URL entity denoted by “URLCustomEntity”.
The Rule query will look like this and the URL entity type will be mapped as defined in the Rule query:
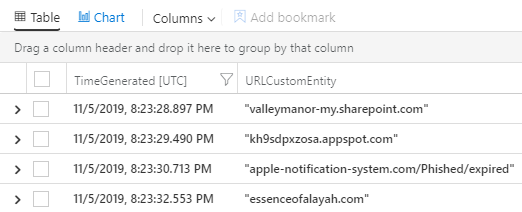
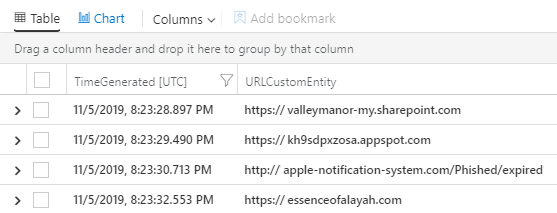
To verify that the selected column contains well-formed URLs required for detonation, click View Query results > located below the Rule query field to navigate to the Logs blade where you can run the query. Inspecting the query results, you’ll notice that the URLs in the “URLCustomEntity” column are missing the protocol identifier:
Here’s an example of how you can append the protocol identifier to the URL to create a well-formed URL for detonation (Note: As an example, you’ll need to do this step for Palo Alto logs in CEF format):
You can test this directly in the Logs blade to validate the formatting:
The final Rule query will look like this:
You can then configure the other parameters, review everything, and then finish creating your Rule.
Viewing detonation results in the Investigation blade
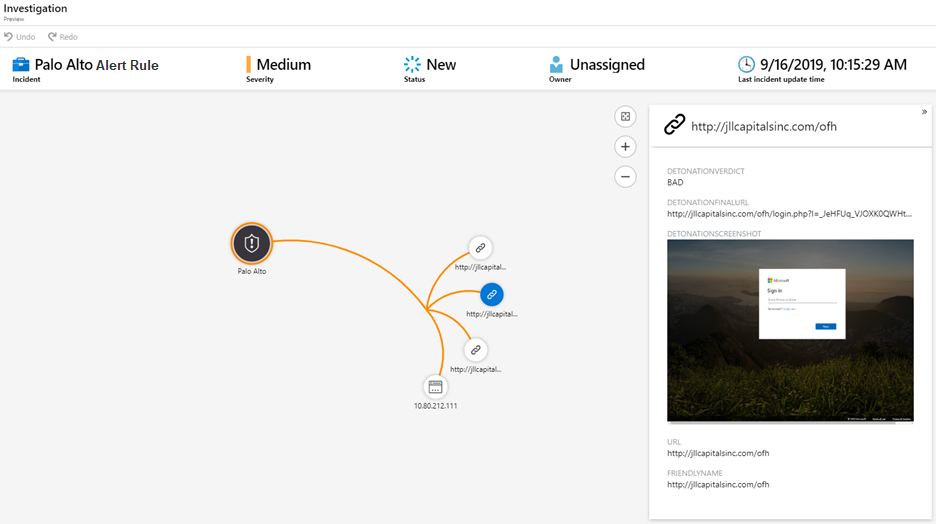
Once you’ve activated your Rule, you can navigate to the Incidents blade, select any Incident associated with your Rule, and click Investigate to view the detonation results in the Investigation blade.
The Investigation blade will include a graph with a node for the detonated URL as well as the following information:
- URL – the original detonated URL.
- DetonationVerdict – the high-level Boolean determination from detonation. ‘Bad’ means the site was classified as hosting malware/phishing content.
- DetonationFinalUrl – the final observed landing page URL after all redirects from the original URL.
- DetonationScreenshot – what the page looked like at the time the alert fired; you can click the screenshot to enlarge.
Conclusion
URL detonation provides deeper insights that enable faster triage of alerts. Moreover, with Azure Sentinel, it’s seamlessly integrated and easy to enable. As a final tip, if you don’t’ see URLs in your logs, check that URL logging (e.g., threat logging) is enabled for your secure web gateways, web proxies, firewalls, or legacy IDS/IPS. You can also create custom logs to channel URLs of interest into Azure Sentinel.