This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
In a discussion with one of my customers, there was a requirement to ingest Box activity events into Azure Sentinel.
There are several possible ways to reach this goal; however, thanks to Microsoft Cloud App Security my customer already had an integration with Box by using the concept of "App connector".
The "App connector" in Microsoft Cloud App Security supports the following activity events in Box - Link.
- List accounts
- List groups
- List privileges
- User governance
- Log on activity
- User activity
- Administrative activity
- DLP - Periodic scan
- DLP - Near-real-time scan
- Sharing control
- File governance
- Apply Azure Information
Microsoft Cloud App Security streams only alerts into Azure Sentinel. The ingestion of Cloud Discovery logs is in public preview, though not the activities for "connected apps".
https://docs.microsoft.com/en-us/azure/sentinel/connect-cloud-app-security
This blog describes a steps by step guide how to ingest Box activity events via Microsoft Cloud App Security into Azure Sentinel, and how to use it.
Preparation & Use
The following tasks describe the necessary preparation steps.
- Install an Ubuntu server
- Deploy and configure a CEF connector server for Azure Sentinel
- Validate the connectivity between connector server and Azure Sentinel
- Setup the SIEM integration for Microsoft Cloud App Security
- Ingest data into Azure Sentinel
- How to use the ingested data in Azure Sentinel
Installation of Ubuntu Server
The installation of the connector server is quite straight forward. After successful installation, make sure that the connector server is deployed with latest updates and includes Python and Java.
The connector server does not require an incoming connection, it should only have an outside connection to the Azure Sentinel instance.
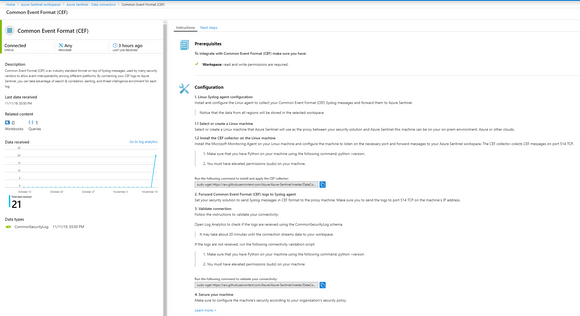
Deploy and validate the CEF connector for Azure Sentinel
The CEF connector page describes the required steps for installation and validation – Link.
Setup the SIEM integration for Microsoft Cloud App Security
The SIEM integration in Microsoft Cloud App Security requires a connector and an agent. When the agent is deployed it pulls the data types that where configured in connector configuration. Once the agent retrieves the data, it then sends it to the SIEM.
For this blog, I prepared the environment to pull Box activity events from Microsoft Cloud App Security Restful API and forward the events to an installed Syslog listener on the connector server. The Syslog agent forwards the Events to Azure Sentinel and ingests in CEF format.
The required configuration is detailed described in following link.
https://docs.microsoft.com/en-us/cloud-app-security/siem#integrating-with-your-siem
Configuration parameter for the connector:
- SIEM format: Micro Focus ArcSight
- Remote syslog server: 127.0.0.1
- Remote syslog port: 514
- Remote syslog protocol: TCP
- Data type configuration:
- Alerts: disable (which is part of the Microsoft Cloud App Security connector in Azure Sentinel)
- Activities: App equal Box
- Save the key for later usage
Ingest data into Azure Sentinel
Start the Microsoft Cloud App Security agent, which is based on Java on the connector server as follows.
sudo java -jar /home/user/mcas-siemagent-0.111.126-signed.jar [--logsDirectory /home/user/] [--proxy 127.0.0.1[:514]] --token QhwZGlccGBwWHBoBWlwcAV9AXVtOQwFMQ0BaS05fX1xKTFpdRltWAUxAQlNJHRtLHh5KShwdTEkfSR0WTUsZHxYaSxoXGhgZGB5JGRwaqweqwzeqwgeqwezwqgRWEUEZWUWErgakasdt
To validate whether the CEF events are received by Syslog server, use the following command line.
sudo tac /var/log/syslog | grep CEF -m 10
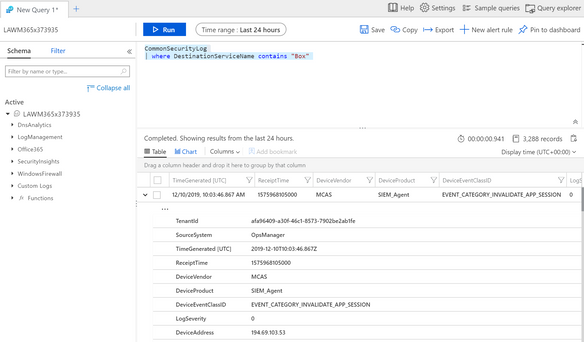
How to use the ingested data in Azure Sentinel
Once the ingestion is processed, you can query the data. The Box activity events will reside within the data in the CommonSecurityLog table.