This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
APIs and Best Security Practices for Microsoft Defender for Cloud Apps update: November 2021
By Omri Amdursky, Microsoft Defender for Cloud Apps
Putting APIs in the forefront of security practices
It’s important to know how to utilize APIs in order to work with a CASB like Microsoft Defender for Cloud Apps. Let’s explore authentication, authorization, and utilization of the Defender for Cloud Apps API to streamline and customize your cloud security experience.
Why APIs?
When looking at the possible ways to consume information from Microsoft Defender for Cloud Apps, three major methods arise:
- Portal: By using the portal at portal.com, you can consume information detected, generated, and aggregated natively by Microsoft Defender for Cloud Apps. You can access data, set policies and governance actions, and investigate alerts. Note that the access to data and available actions are directly dependent on the role assigned to the user as designated by Defender for Cloud Apps in the SIEM connector.
- SIEM connector: Customers can utilize a Security Information and Event Management (SIEM) product to consume the data and enrichments offered by Microsoft Defender for Cloud Apps. Our customers frequently deploy a SIEM to aggregate alerts and raw data from several security products. For example, many of our customers use Microsoft Sentinel with the M365 Security suite to protect all facets of their organization while consuming alerts via a single interface, streamlining the SecOps experience while not compromising on protection.
- API: An Application Programming Interface (API) is a way for a developer or a technically savvy customer to access a security products’ information and assets through a customized programmatic approach. Using the API allows for pulling raw data as well as enhanced data (like alerts) while filtering and configuring custom-made behavior.
Out of these methods, API-based access is the most customizable and allows aggregation and analysis of data by the customer.
Benefits of leveraging APIs
- Security – Leveraging the security measures developed by Azure Active Directory, this authentication method allows for secure and highly manageable issuing of API tokens. These tokens are created for specific services – making them siloed and independent from each other. Additionally, these tokens can be set to be automatically refreshed, meaning that you can control the length of active duty that these tokens will serve.
- Stability – When issuing an API token using an application context, you’ll find that the permissions of the token are decoupled from the permissions of granting a stable, consistent, and predictable behavior by the token. The user is able to select specific permission scopes, preventing over-permissions of the token in process. If a token is over-permitted, it could create a risk of unintended use or potential insider behaviors inappropriate to that organization’s security policies.
- Ease of partner access – Since the tokens are issued in Azure Active Directory, they conform to the Microsoft standard, allowing partners and MSSPs to manage a customer’s security products across the Microsoft suite. Issuing an API token at a single point of security for a registered app and then granting it access to several Microsoft products allows for increased ease of integration with a security partner.
Best practices for using APIs
In order to connect to the Microsoft Defender for Cloud Apps APIs, you must first issue an API token, enabling your authentication and confirming your identity. This method enables Microsoft to release the data solely to the authenticated users from the customer tenant. Before creating an app to use with our API, please review it so you can select the correct permission scope. These endpoints allow for accessing data, configuring your tenant, and auditing your activities.
Step by step directions
Note: the flow below describes authentication in an application context, removing the dependency from a user entity.
- Sign in to Azure with a user identity that has the Global Administrator role.
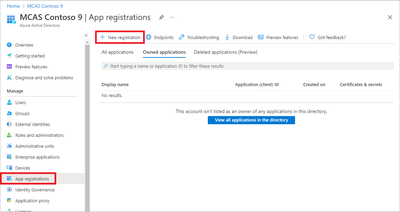
- Navigate to Azure Active Directory > ‘App registrations’ (in the left pane) > select ‘New registration.’
- In the registration form, create a name for your application, and then select ‘Register.’
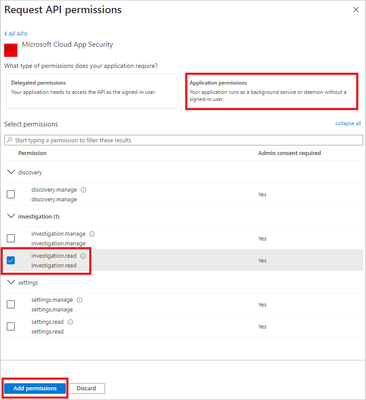
- Select ‘API Permissions ‘> select ‘Add Permission’ > select ‘APIs my organization uses’ > type 'Microsoft Defender for Cloud Apps', and then select ‘Microsoft Defender for Cloud Apps.’
- Select ‘Application Permissions’ and choose from the given options for the permissions best suited to your need. The available permissions include the following:
|
Permission name |
Supported actions |
|
Investigation.read |
Activities list, fetch, feedbackAlerts list, fetch, mark as read/unreadEntities list, fetch, fetch treeSubnet list |
|
Investigation.manage |
Activities list, fetch, feedbackAlerts list, fetch, mark as read/unread, closeEntities list, fetch, fetch treeSubnet list,create/update/delete |
|
Discovery.read |
Alerts list, fetch, mark as read/unreadDiscovery list reports, list report categories |
|
Discovery.manage |
Alerts list, fetch, mark as read/unread, closeDiscovery list reports, list report categoriesDiscovery file upload,generate block script |
|
Settings.read |
Subnet list |
|
Settings.manage |
Subnet list, create/update/delete |
6. Select ‘Grant Admin Consent.’
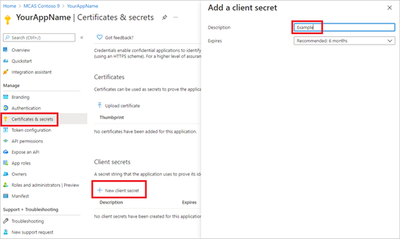
7. To add a secret to the application, select ‘Certificates & Secrets,’ select ‘New Client Secret,’ add a description to the secret, and then select ‘Add.’
Note: Don’t forget to copy your secret value when it is shown, as it will not be available later.
8. Take note of your application ID and your tenant ID. On your application page, go to ‘Overview’ and copy the Application (client) ID and the Directory (tenant) ID.
Congrats! You now have a registered application. APIs are the most customizable method of consuming data from Microsoft Defender for Cloud Apps. Managing API access with Azure Active Directory allows you to do it in the most secure manner. APIs provide increased security and mitigate more risk from inappropriate use of tokens as well as authentications and authorizations within Microsoft Defender for Cloud Apps. Streamline and customize your cloud security experience today.
To learn more about APIs in Defender for Cloud Apps, see this technical documentation page.
To experience the benefits of full-featured CASB, sign up for a free trial—Microsoft Defender for Cloud Apps.
Feedback
We welcome your feedback or relevant use cases and requirements for Defender for Cloud Apps by emailing CASFeedback@microsoft.com. Please mention APIs in the subject line.
Learn more
For further information on how your organization can benefit from Microsoft Defender for Cloud Apps, connect with us at the links below:
|
Join the conversation on Tech Community. Stay up to date—subscribe to our blog. |
Upload a log file from your network firewall or enable logging via Microsoft Defender for Endpoint to discover Shadow IT in your network. |
|
Learn more—download Top 20 use cases for CASB. |
Connect your cloud apps to detect suspicious user activity and exposed sensitive data. |
|
Search documentation on Microsoft Defender for Cloud Apps. |
Enable out-of-the-box anomaly detection policies and start detecting cloud threats in your environment. |
|
Understand your licensing options. |
Continue with more advanced use cases across information protection, compliance, and more. |
|
Follow the Microsoft Defender for Cloud Apps Ninja blog and learn about Ninja Training. Go deeper with these interactive guides:
|
|
Follow us on LinkedIn as #CloudAppSecurity or our new name, #DefenderforCloudApps. To learn more about Microsoft Security solutions visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity on Twitter, and Microsoft Security on LinkedIn for the latest news and updates on cybersecurity.