This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Microsoft Sentinel is a cloud native SIEM and SOAR solution that allows you to detect and hunt for actionable threats. Microsoft Sentinel allows various ways to import threat intelligence data and use it in various parts of the product like hunting, investigation, analytics, workbooks etc.
One of the ways to bring in threat intelligence data into Microsoft Sentinel is using the Threat Intelligence – TAXII Data connector. This data connector in Microsoft Sentinel uses the TAXII protocol for sharing data in STIX format which is one of the most widely adopted standard for sharing threat intelligence across the industry. This data connector supports pulling data from TAXII 2.0 and 2.1 servers. The Threat Intelligence – TAXII data connector is essentially a built-in TAXII client in Microsoft Sentinel to import threat intelligence from TAXII 2.x servers.
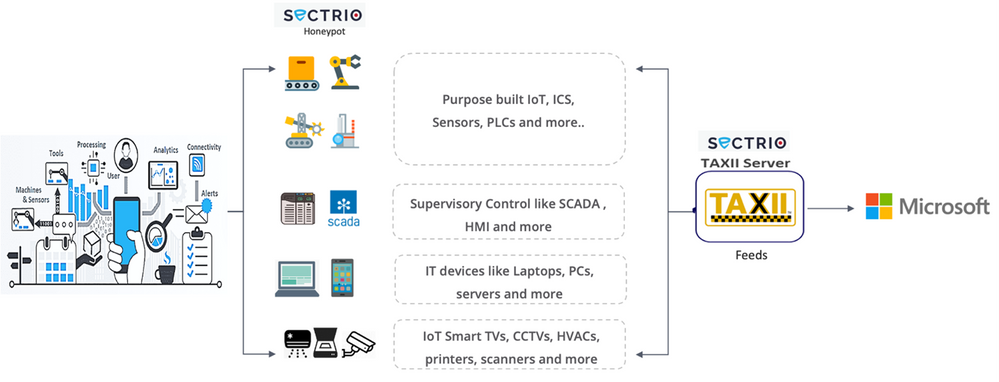
Today we are announcing the availability of the Sectrio TAXII server which allows you to get threat intelligence data from Sectrio into Microsoft Sentinel using the TAXII data connector.
Benefits of Sectrio + Microsoft Sentinel Integration
Sectrio and Microsoft Sentinel Integration enhances visibility of threats and attack surfaces that target non-traditional IT such as OT and IoT along with traditional IT. Sectrio provides rich IoT and OT cyber threat Intel indicators that target your industrial environments and attack vectors spanning across legacy devices and infrastructure. With Sectrio's threat intelligence integrated into your Microsoft Sentinel Platform, you get real-time updates on threat indicators captured from our global honeypot networks spanning over 75 locations analyzing over 12 million daily threat samples generated from IT-OT and IoT ecosystem. Sectrio once integrated into your Microsoft Sentinel Platform provides robust security measures leveraging MITRE ATT&CK framework and making it easier for Security teams to manage their incident response efficiently focused on their critical Infrastructure.
Connecting Sectrio to Microsoft Sentinel
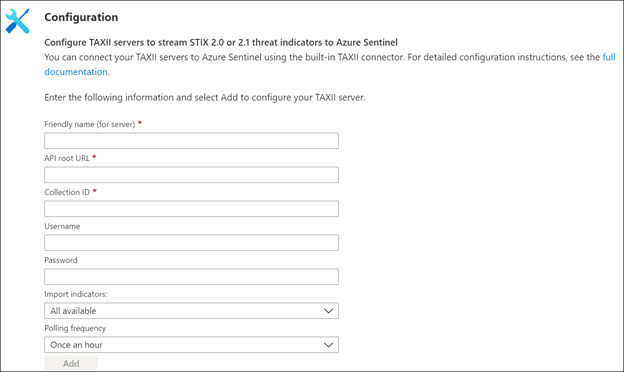
To connect Sectrio feeds to Microsoft Sentinel, visit https://sectrio.com/threat-intelligence/ and follow the sign-up process. Once successfully signed up, you will receive a secure automated email with the information containing the API root URL, collection ID, username and password and steps to configure the feeds with Sectrio Threat Intelligence guide document.
If you don’t receive an email within 24 hours, you can directly reach out to our customer success at ti.support@sectrio.com and one of the Sectrio customer success managers will respond back with the details.
Once you have the API root URL, Collection ID and credentials from Sectrio, you can configure the TAXII data connector in Microsoft Sentinel. For more details on how to configure the TAXII data connector in Microsoft Sentinel, please refer to the following documentation.
Once you import threat intelligence data from Sectrio into Microsoft Sentinel it shows up in the ThreatIntelligenceIndicator table of log analytics. The data also shows up in the Threat Intelligence menu in the product where you can search, sort, filter, and tag the data.
Put Sectrio threat intelligence to use in Microsoft Sentinel
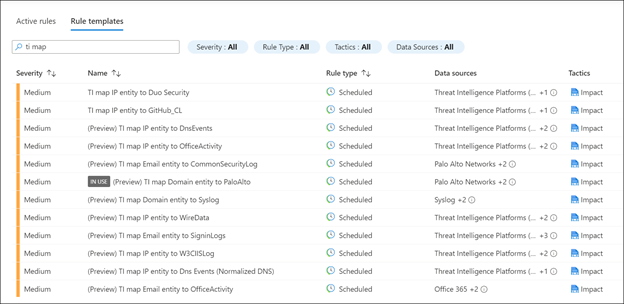
Once the threat intelligence from Sectrio is imported into Microsoft Sentinel, you can use it for matching against log sources. This can be done using the out-of-the-box analytic rules in Microsoft Sentinel. These completely customizable analytic rules are used to match threat indicators with your event data and all have names beginning with ‘TI map’.
To learn how to enable and create these analytic rules, follow the steps mentioned in this documentation.
Conclusion
With the release of the Sectrio TAXII server, it is extremely easy to bring in the threat intelligence feed from Sectrio into Microsoft Sentinel by leveraging the built-in TAXII client of Microsoft Sentinel. This data can be then be easily utilized by SOC analysts in your organization for further hunting, investigation and analysis of threats.