This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Our recent advanced search capability supports the ability to retrieve incidents that match a search string and define the incident fields where you want to run the search.
With this feature becoming generally available, we are happy to provide a deep dive into several ways that you can use the advanced search to get further value from your incidents:
- Search for specific incidents
The advanced search helps you find any incidents in just seconds. With the new search field filtering, retrieve incidents based on almost any incident field, as well as main alert fields.
- Find all incidents related to an entity/bookmark
Use the advanced search to easily find all of the incidents related to a specific entity or bookmark. Whether if it is as part of an investigation or a hunt, search by one of the entity’s identifiers or a bookmark name to find all of the related incidents, whether they’re open or closed.
- Find incidents based on identifiers in external systems
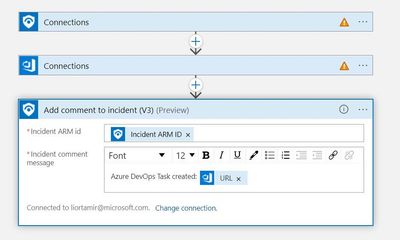
Use the new playbooks available in our playbook gallery to leverage automation and sync with external systems, such as Azure DevOps, Jira, and many more. Then, to retrieve the incident related to a specific DevOps task or Jira incident, search for the task or incident ID from the comment field.
The following image shows how you can use a playbook to add a DevOps task from an incident:
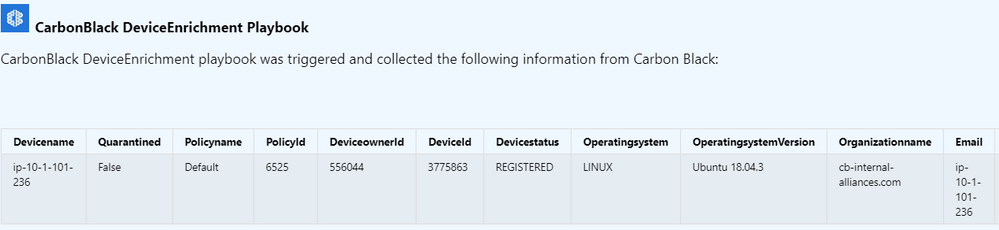
- Search by entity enrichments
Many of our OOTB playbooks offer entity enrichment from various products, such as CarbonBlack, Zscaler, CrowdStrike, Okta, and more. Each of these playbooks adds a comment with additional data on the incident info, which is searchable using the advanced search. For example:
Have an idea for additional ways you can use the advanced search to get value from your incidents? post them in the comment section below!