This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Hi everyone, it’s Gershon, back again with a follow up to my last blog where we were able to track changes to sensitive groups with Advanced Hunting in Microsoft 365 Defender. One of the questions I had from a customer after they read through the blog was “how can we be alerted directly when a group has been added to a sensitive group?”. This is a great question to focus on, as this scenario should not be commonplace in an established environment, as nested group memberships in sensitive groups should not be something that changes after initial set up. Additionally, adding a group to another group is a quick and easy way to add users to a sensitive group and making sure it’s highlighted quickly could stop an attacker from gaining persistence.
We will start by assuming that all the steps from my previous blog have been completed, where we can see all the changes to the groups we defined as sensitive.
In this blog, we will take things further by:
- Updating the advanced hunting query to focus on groups that are added to a sensitive group.
- Validating that the query works as expected.
- Creating a custom detection policy based on the advanced query.
- Testing out the custom detection policy.
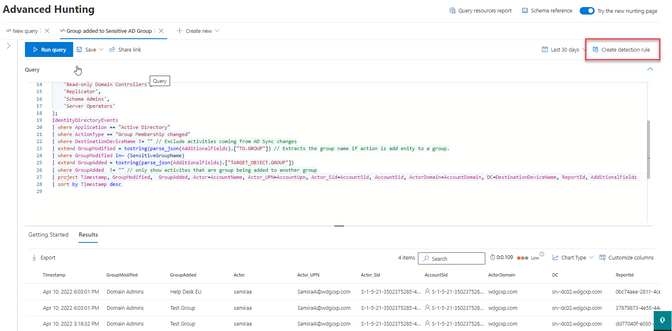
Updating the advanced hunting query to show additions of a group to a sensitive group.
Starting with the query from the last blog as a starting point, we will make a few changes that focuses on activities that occur when adding a group to a sensitive group.
In the last line, we will also add the “AccountSid” column as this can be used in the custom detection policy, covered later in this entry.
As you can see here, the results only show groups that have been added to a sensitive group.
If you don’t see any results when you run your query, you can either change the time range or add a group to one of the sensitive groups listed in the array at the beginning of the query.
Create a custom detection policy
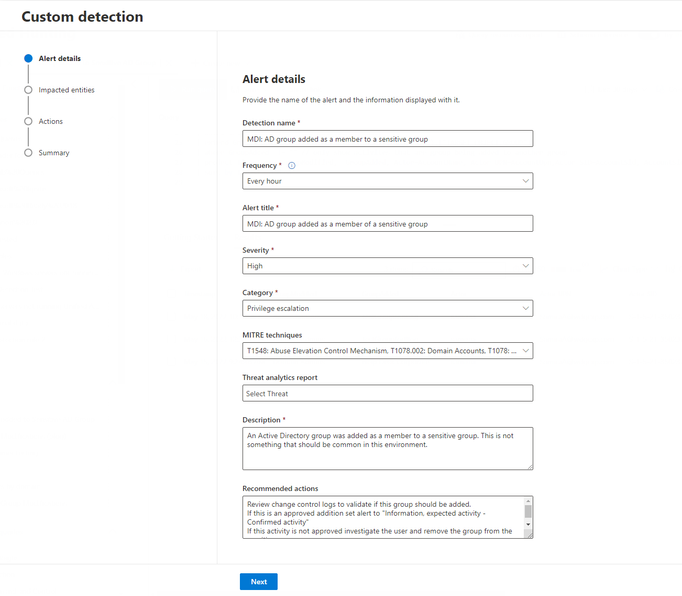
After you are comfortable with the query, we can now create the custom detection rule.
- Click “Create detection rule” on the top right corner.
- On the alert details page enter the required information and click Next. See the screenshot below.
The customer I was working with selected High for Severity as this is not something that should happen often, if at all, in their environment.
For the MITRE techniques the customer chose:
- T1078 Valid Accounts
- T1078:002 Domain Accounts
- T1548 Abuse Elevation Control Mechanism
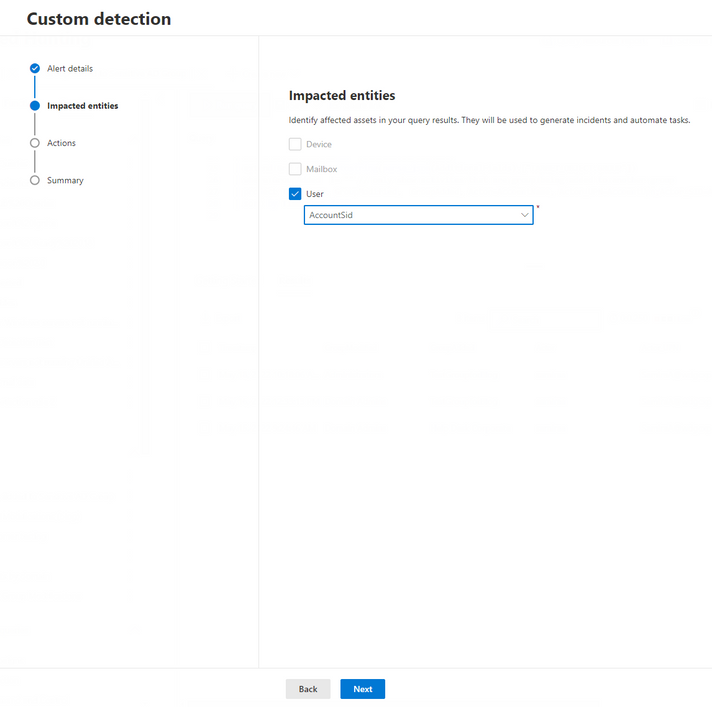
- On the Impacted entities page, select User and AccountSid and then click Next. This is the reason we needed to add the AccountSid column in the project line in the query earlier.
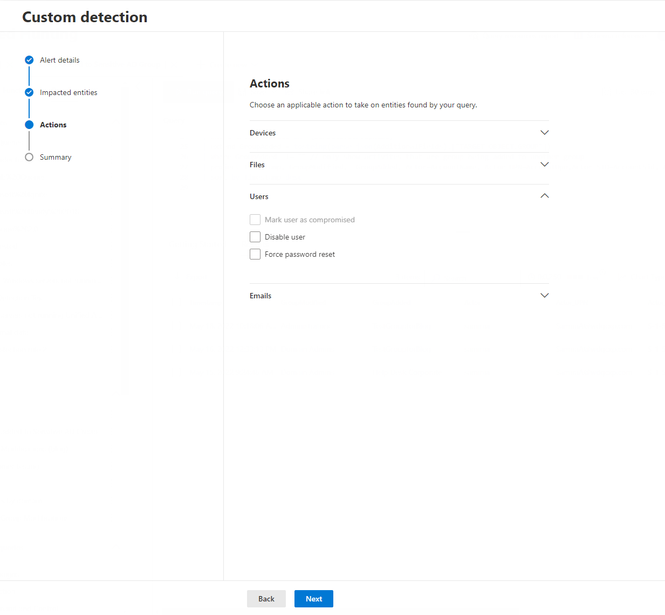
- On the Actions page expand Users. If you have configured an action account in the Defender for Identity settings page, you will have the option to select Disable user and Force password reset actions. If you select one of these actions, Microsoft Defender 365 will attempt to disable the user or reset the user’s password in Active Directory. Click Next to move to the Summary page.
- On the Summary page, review the rule you’ve created and click Submit.
- You will now see the custom detection listed on the Detection rules page
Test new custom detection rule
Now we want to test that the new rule is working as expected.
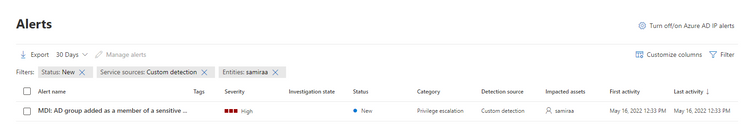
In Active Directory, create a new group and add this group to a sensitive group. In my lab I created a group named “TestGroupforBlog” and added it as a member of “Domain Admins.”
There are different ways that we can search for the alert. Here is one way:
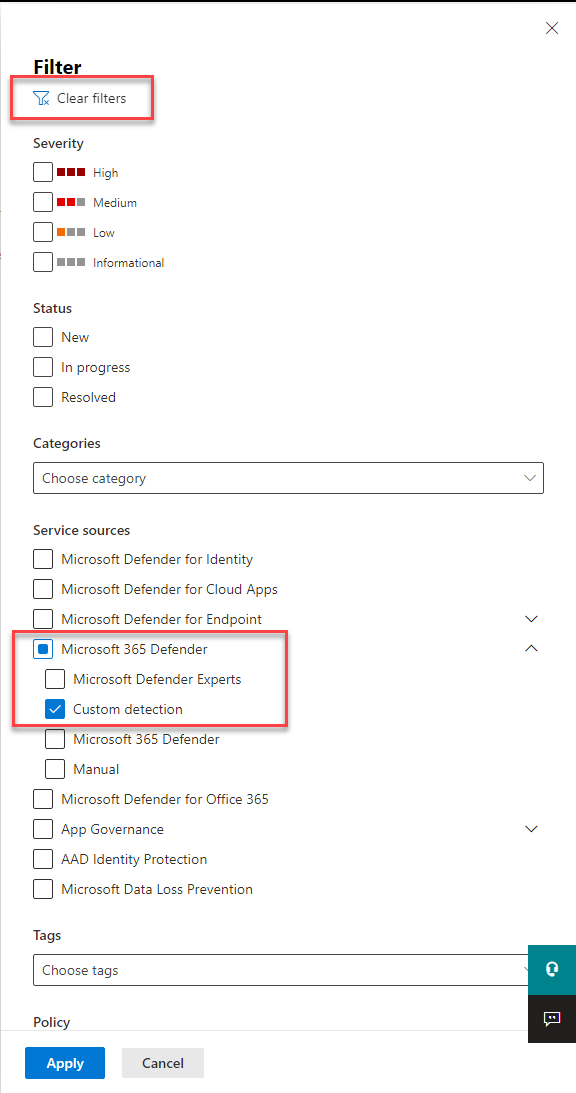
- In the Microsoft 365 Defender portal, click on Alerts and then click on Filters.
- In the filter pane, click Clear filters, and under Service Sources expand Microsoft 365 Defender and select Custom Detection.
- Click Apply.
- Find the alert with title given when you created the custom detection policy earlier and click on the alert to see the details.
-
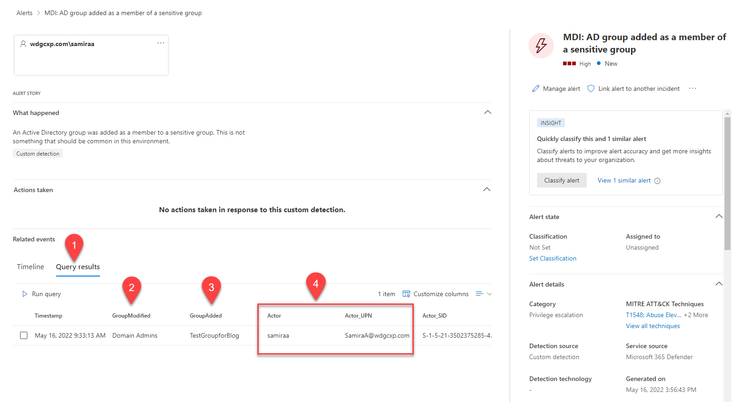
To see the activities that triggered this alert click Query results (1). You can see the sensitive group that was modified (2), the group that was added to the sensitive group (3) and the user who made this change (4).
If this is an approved legitimate change, we would want to update the Advanced Hunting query to include this group in the list of sensitive group list for this query and for the query from the previous blog.
If this was an unauthorized change, we should continue to investigate the user to see:
- additional activities they have performed
- additional alerts open for the user
- devices the user has logged in to
We can do this using data from all the products in Microsoft 365 Defender.
For more information on investigating threats see, https://docs.microsoft.com/en-us/microsoft-365/security/defender/incidents-overview?view=o365-worldwide.
So to recap, you just created a query to show activities when a group is added to a sensitive group and then you created a custom detection policy. Congratulations! Feel free to save this query, then customize it further to suit your organization’s needs.
If you find the query and custom detection policy helpful, please leave a comment, or use the comment space to tell us what you’ve done to make this query even more powerful in your organization. Please let us know what areas you want to see us tackle next in Advanced Hunting. We can’t wait to hear your ideas. Happy hunting!