This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Community Hub.
Organizations today face the continually changing and complicated task of protecting their ever-expanding attack surface from cyber-attacks. The move to the Cloud and remote workspaces has pushed the boundary of their digital ecosystem well beyond their traditional physical network. Data, users, and systems are in multiple locations, creating significant challenges for security operations teams tasked with defending their organizational assets. Information Security personnel need to be equipped with solutions to identify new adversaries and threats like ransomware.
It's now crucial for defenders to have unique visibility across both their organization's attack surface and the threat infrastructure used to target it. In this blog, I will highlight key capabilities in Microsoft Defender for Cloud (MDC) and Microsoft Defender Threat Intelligence (MDTI) that, when used together, enable analysts to quickly understand exposures and equip them with crucial context about threat actors likely to target them.
Microsoft Defender Threat Intelligence can help identify and mitigate modern threats and their infrastructure with dynamic threat intelligence by applying three key capabilities:
- Identify attackers and their tools.
- Accelerate detection, incident response, investigations, and remediation.
- Enhance security tools and workflows.
To watch an overview of MDTI, please review the episode here.
MDC is a cloud-native application protection that helps strengthen security posture, enabling protection against modern threats and helping reduce risk throughout the cloud application lifecycle across multi-cloud and hybrid environments. MDC works with security teams to efficiently reduce the risk of an impactful breach to their environment.
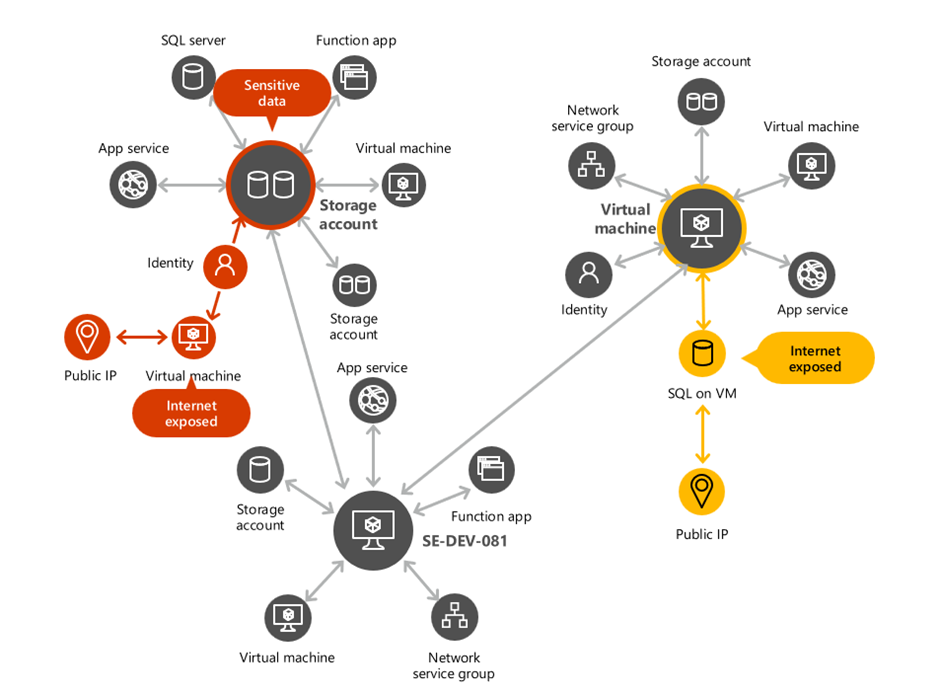
During Microsoft Ignite, MDC introduced new capabilities, including the cloud security graph and attack path analysis capabilities that enable analysts to assess the risk behind each security issue and identify and prioritize the highest-risk issues.
What is Cloud Security Explorer?
Cloud Security Explorer provides defenders with the ability to perform proactive exploration. With it, analysts can search for security risks within their organization by running graph-based path-finding queries on top of the contextual security data Defender already provides for Cloud, including cloud misconfigurations, vulnerabilities, resource context, lateral movement possibilities between resources, and more.
figure; Cloud Security Graph
Threat Intelligence Articles and the Cloud Security Graph
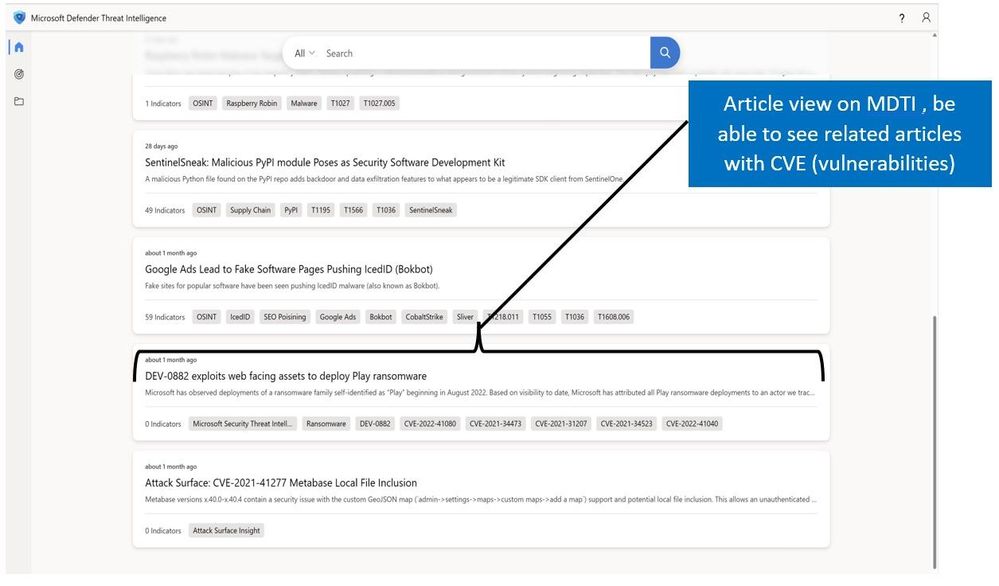
One of the critical features of MDTI is Articles. Articles are written by Microsoft research teams or curated open-source intelligence enriched by Microsoft's unique insight into threat actors, tooling, attacks, and vulnerabilities. MDTI intelligence includes actionable content and critical indicators of compromise to help security professionals act quickly against threats and continuously track threat actors, tooling, attacks, and vulnerabilities as they evolve.
The following image shows an overview of the different Articles created in MDTI with a Tag, which provides insight into an artifact and quickly links incidents and investigations with historical context for improved analysis.
Figure: article View on Microsoft Defender for Threat intelligence
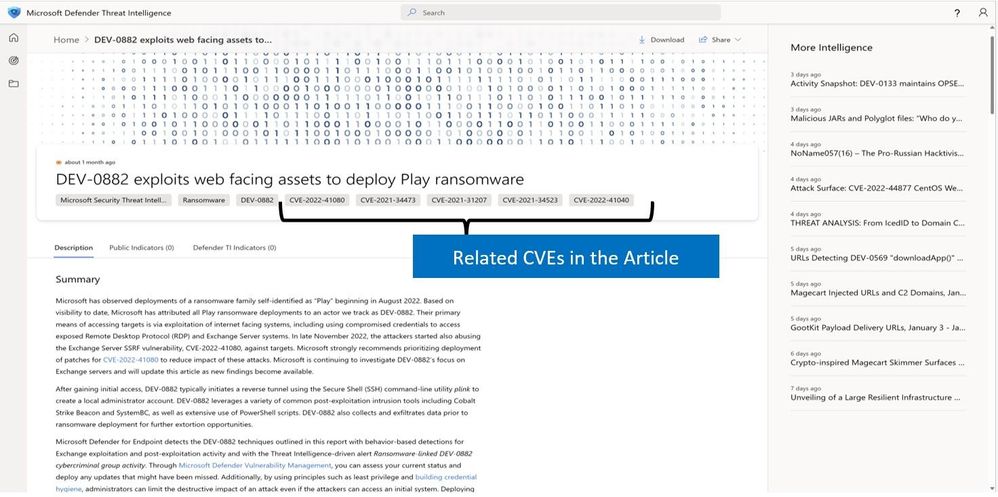
In this case, we are interested in the Article "DEV-0882 exploits web-facing assets to deploy ransomware" due to aligned Tags for ransomware and CVEs.
After clicking on the article, the analyst can obtain a deeper understanding of the threat actor identified and tap into crucial explanatory information ranging from a summary of the threat, an analysis of the infrastructure it targets, and information for post-compromise and mitigation tactics. In this situation, we can track the threat actor DEV-0882, which is consistent with ransomware campaigns.
Figure: identified related CVEs within Article "DEV-0882 exploits web-facing assets to deploy ransomware"
The article can also contain a detailed analysis of the threat actor and its underlying infrastructure. In this case, we get information on the infrastructure targeted by the threat actor and their post-compromise tactics.
Figure: Analysis information for article "DEV-0882 exploits web-facing assets to deploy ransomware"
Some of the articles will also contain information detailing mitigation tactics that customers can apply to their environment:
Figure: Mitigation procedures described in the Article "DEV-0882 exploits web-facing assets to deploy ransomware"
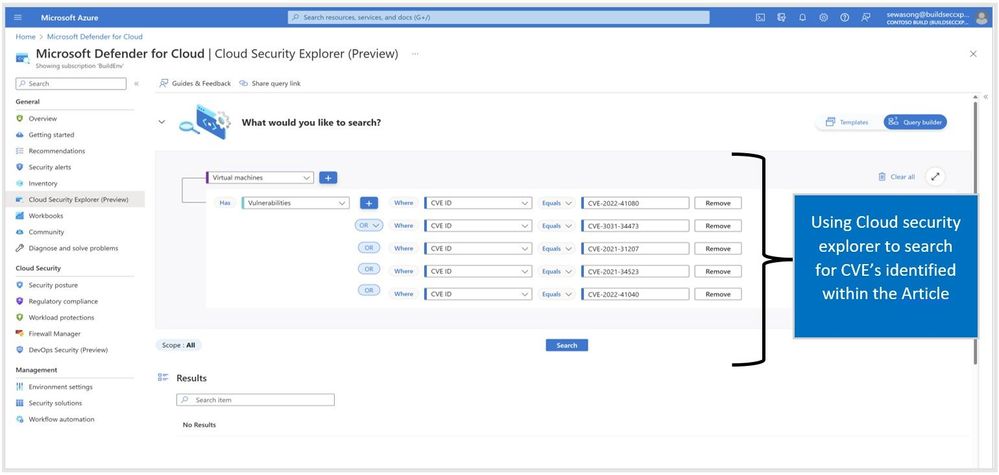
In this case, we have identified the CVEs related to the article "DEV-0882 exploits web-facing assets to deploy Play ransomware." They are CVE-2022-41080, CVE-3031-34473, CVE-2021-31207, CVE-2021-34523, and CVE-2022-41040. Proactively, a SOC analyst can proceed to the cloud Security explorer blade in MDC and run a query searching virtual machines that each vulnerability could impact. This can be seen in the following approach:
Figure: Using cloud security explorer to search for Vulnerabilities based on CVEs identified in MDTI
MDTI Enriches Alerts in MDC
As analysts triage alerts generated within MDC (paid plans will need to be enabled for this to occur), they can use MDTI to quickly investigate entities' information to promptly identify the following:
- If an artifact (IP, domain, or host) exists in any threat intelligence articles.
- The artifact's reputation: MDTI generates proprietary reputation scores for any Host, Domain, or IP address to help provide quick information about the activity of these entities, such as First and Last-Seen timespans, ASN, country, associated infrastructure, and a list of rules that impact the reputation score (when applicable).
- Analyst Insights: These insights distill Microsoft's vast data set into a handful of observations that simplify the investigation and make it more approachable to analysts of all levels. Insights are small facts or observations about a domain or IP address and enable Defender TI users to assess the artifact queried and improve a user's ability to determine if an indicator being investigated is malicious, suspicious, or benign.
To get started with the investigation in this scenario, we will begin with the security alerts blade on MDC to identify the alert of interest and the alert's full details.
Figure: Alert generated by Microsoft Defender for Cloud "Suspected brute force attack attempt using a valid user "
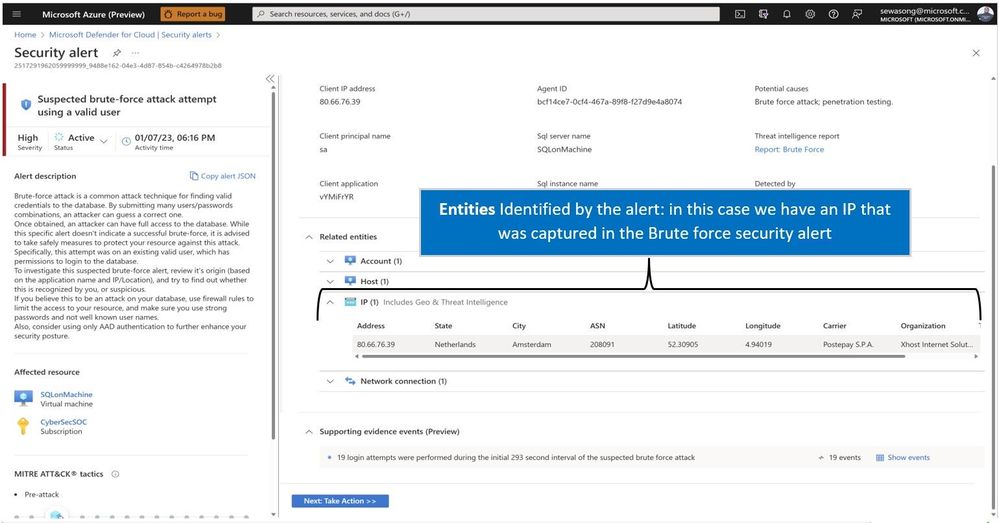
Clicking on the 'View full details' option of the alert, an analyst gets more information and can see the severity information, description, and affected resources. They get crucial visibility of the related entities identified and can pivot to MDTI for further investigation.
Figure: Alert view on Microsoft Defender for Cloud, highlighting the entities involved in the alert.
On the MDTI workbench, the analyst can search for the IP address (80.66.76.39) identified in the alert.
Figure: Heading over to MDTI and searching the artifact (IP~ 80.66.76.39)
On searching the artifact, MDTI provides information an analyst can use to determine the entity's validity. In this case, we see data that confirms the IP is potentially used for malicious activity. The reputation score indicates suspicious activity.
Figure: Artifacts results capturing reputation scoring, analyst insights, and Articles View
The MDTI workbench also provides the user with the ability to pivot to the data blade, where they can identify a series of datasets categorized into two groups: Traditional (Resolutions, Whois, SSL Certificates, Subdomains, DNS, Reverse DNS, and Services) and Advanced (Trackers, Components, Host Pairs, and Cookies. Trackers, Components, Host Pairs, and Cookies). The primary focus is to collect data about the internet infrastructure to support the investigation process.
Figure: Proceed to the Data tab: Who IS information for Suspicious Artifact
In this case, the analyst can determine if the IP used in the suspected brute force attack is synonymous with malicious activity and use it to identify other entities that could serve as investigative leads for incident response and threat hunting.
In summary, there are a variety of scenarios where Microsoft Defender for Threat Intelligence can work hand in hand with MDC. The scenarios above offer proactive and reactive methods for SOC analysts, Threat hunters, and Vulnerability managers to leverage both tools to improve their operations and processes.
Questions?
We hope you found this blog helpful in understanding the value MDTI can provide. If you have inquiries regarding threat intelligence use cases mentioned or not mentioned in this blog and are not currently working with an MDTI Technical Specialist or Global Black Belt, please email mdti-pm@microsoft.com.
Feedback?
We would love to hear any ideas you may have to improve our MDTI platform or where our threat intelligence could be used elsewhere across the Microsoft Security ecosystem or other security third-party applications. Feel free to email mdti-pm@microsoft.com to share that feedback as well. If you are currently working with an MDTI Technical Specialist or Global Black Belt through this PoC, please communicate your requested use cases and product feedback to them directly.
Learn About New MDTI Features
Please join our Cloud Security Private Community if you're not a member and follow our MDTI Private & Public Preview events in our MS MDTI channel. You will not have access to this Teams channel until you are a Cloud Security Private Community member. Users that would like to help influence the direction/strategy of our MDTI product are encouraged to sign-up for our Private Preview events. Those participating will earn credit towards respective Microsoft product badges delivered by Credly.
Work With Our Sales Team
If you are interested in working with an MDTI Technical Specialist or Global Black Belt, please get in touch with our Sales team by filling out this form.
Resources
What is Microsoft Defender Threat Intelligence (Defender TI)? | Microsoft Learn
Microsoft Defender Threat Intelligence Blog - Microsoft Community Hub
Become a Microsoft Defender Threat Intelligence Ninja: The complete level 400 training