This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Community Hub.
In previous blogs, we've emphasized the importance of multifactor authentication (MFA). Today, organizations and end users are using various authentication methods, providing varying levels of security. Users often choose less secure MFA methods, despite having access to more secure options due to a range of factors such as convenience, lack of awareness, or technical limitations.
To encourage users to authenticate with the strongest method available to them, we’re announcing system-preferred authentication for MFA. This system prompts the user to sign in with the most secure method they’ve registered and the method that’s enabled by admin policy. This will transition users from choosing a default method to use first to always using the most secure method available. If they can’t use the method they were prompted to use they can choose a different MFA method to sign in.
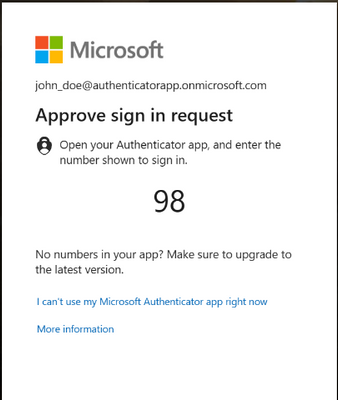
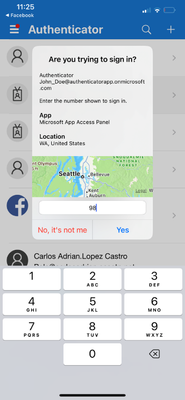
Administrators can roll out the feature by using the admin UX in the Azure Portal or via GraphAPI. For example, the user "John Doe" has registered both SMS and Microsoft Authenticator, and SMS is the default option that they used to sign in with. Once this feature has been enabled, the system-preferred method (Authenticator) will be presented to the user.
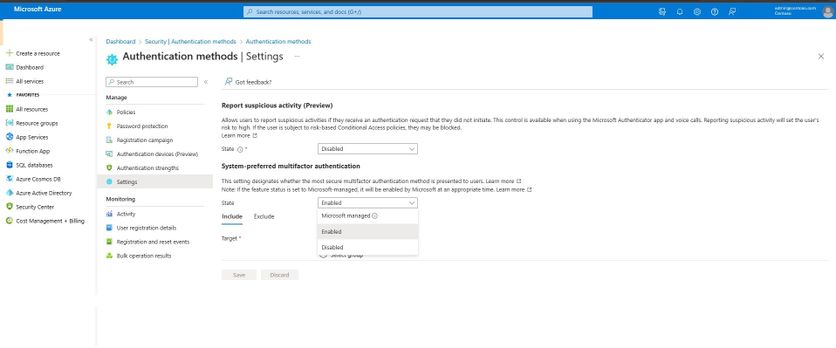
Admins can enable system-preferred MFA in Settings for Authentication methods.
This is how the Security info page appears when a user is enabled for system-preferred MFA:
The most secure method for the user in this example is Microsoft Authenticator:
With an ever-changing threat landscape, it’s now more important than ever for organizations to stay ahead of bad actors. With that in mind,
- This feature was introduced in April 2023, set to Microsoft managed (Disabled) by default.
- After this initial phase, the feature will be rolled out as Microsoft managed (Enabled) for all tenants, with admins retaining the option to disable it as needed.
- Finally, the feature will be set to Microsoft managed (Enabled) for all tenants, and the control to disable the feature will be removed.
To ensure organizations have adequate time to prepare for the rollout, we plan to share more detailed timelines by June.
To best secure your organization and its end users, we highly encourage you to use the rollout controls and deploy this new feature as soon as you can. It’s now available in your tenant, making it easy to ensure users always use the most secure authentication method first.
As always, we want to hear from you! Feel free to share your comments or reach out to us on aka.ms/AzureADFeedback.
Best regards,
Alex Weinert (@Alex_T_Weinert)
VP Director of Identity Security, Microsoft
Learn more about Microsoft identity:
- Authentication strength – choose the right auth method for your scenario! - Microsoft Community Hub
- Get to know Microsoft Entra – a comprehensive identity and access product family
- Return to the Microsoft Entra (Azure AD) blog home
- Join the conversation on Twitter and LinkedIn
- Share product suggestions on the Entra (Azure AD) forum