This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Community Hub.
Nowadays, more and more registries are evolving to enable users to store, pull, distribute, and view OCI artifacts not only container images. Containers Secure Supply Chain initiatives also drove the need for distributing supply chain artifacts like signatures, vulnerability reports, and signed Software Bill of Materials (SBOM), and attestations alongside container images in the registry, without mutating the existing content.
How to efficiently build the reference relationship by associating the container images with its supply chain artifacts in the OCI registry? What is the right posture to distribute container images with its supply chain artifacts across registries and file system?
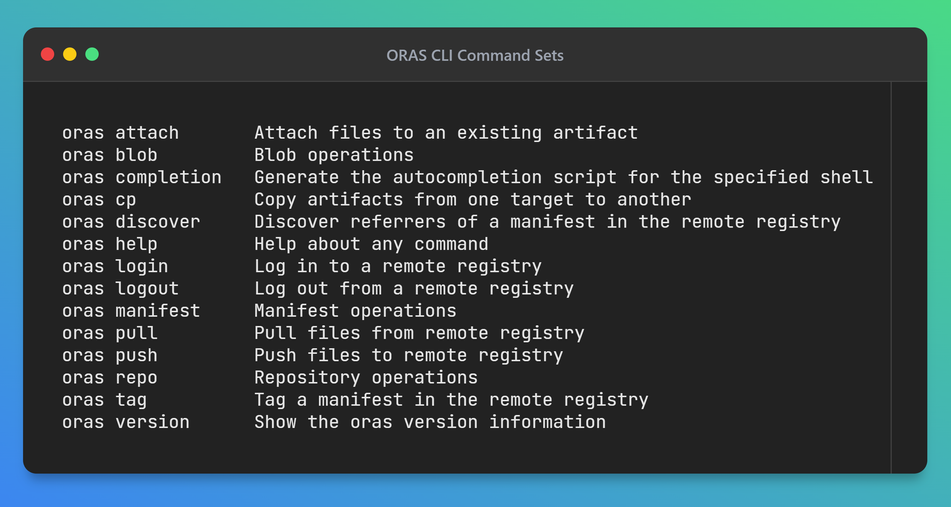
ORAS is a client tool for working with OCI artifacts and registries. It allows you to distribute OCI artifacts across OCI registries and file system. ORAS works similarly to tools you may already be familiar with, such as Docker. What ORAS does differently is shift the focus from container images to other types of artifacts.
ORAS was established and open-sourced in Dec 2018 and joined CNCF as a Sandbox project in June 2021. It has been adopted by a lot of well-known products and organizations. ORAS provides a CLI tool for users to distribute OCI artifacts across registries with ease. For developers who want to develop their own user experience on top of ORAS, there are also multiple ORAS client libraries including Golang, Python, .Net SDK.
Use ORAS to associate SBOM and lifecycle metadata with container image
SBOM improves the visibility, transparency, security and integrity of container images and open-source software in software supply chains. Image lifecycle metadata shows the validity of a container image. Distributing container images along with SBOM and image lifecycle metadata enables users to validate images before using them, thus increasing the security posture of containers supply chain.
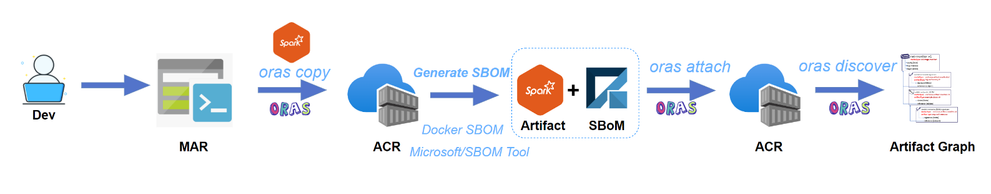
An example use case of ORAS is to copy a base image from one registry to another registry, then generate an SBOM file for and attach the SBOM to the container image. Users can easily view the reference relationship graph between them.
Copy the container image from the public Microsoft Artifact Registry to my private Azure Container Registry.
Generate an SBOM for the image and attach the SBOM to the image.
Display the attached SBOM alongside the image in a tree graph.
Add the image lifecycle metadata as an annotation to an image.
Want to learn more?
In this follow-up episode, we delve deeper into the world of containers supply chain security, examining the CNCF ORAS project's latest developments. We'll explore the intricacies of the OCI registry and OCI image layout and its integration with tools like Helm and Notation, emphasizing their role in enhancing container supply chain security. Additionally, we discuss the significance of image lifecycle annotations in maintaining a secure and efficient supply chain.
Join us as we demonstrate how to use ORAS CLI to distribute supply chain artifacts across registries and manage image metadata in the containers secure supply chain scenario.
How to get started?
Try ORAS within minutes: https://oras.land. Learn concepts and best practices of containers secure supply chain in Containers Secure Supply Chain Framework: https://aka.ms/csscframework