This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Community Hub.
Introduction
Microsoft Defender for Endpoint (MDE) is a unified endpoint security platform that helps protect your devices from advanced threats. MDE on iOS/iPadOS devices provides protection against phishing and unsafe network connections. To use MDE on iOS devices, you need to enroll them in Microsoft Intune, a cloud-based service that helps you manage and secure your mobile devices.
This blog post helps you prepare your environment for zero-touch aka silent enrollment of MDE on your Intune managed iOS/iPadOS devices. Zero Touch enrollment is not available for all scenarios, below is a matrix for reference:
In this post, we will discuss the two selected scenarios which support silent onboarding of MDE. This does not include Shared/Kiosk or user-less devices.
Prerequisites
Before you enroll MDE on iOS/iPadOS devices, make sure you have the following:
- An Intune enrolled device with a valid user license for MDE. For MAM (Microsoft Application Management) and 3rd party MDM’s there is a separate onboarding process I will discuss in a future blog post.
- An iOS/iPadOS version 15 or above.
Tip: You may want to create a Device group for these target devices since the configuration policies below are recommended to be deployed against devices.
Deploy the Defender App
You may choose to deploy the Microsoft Defender App from Intune either via VPP (volume purchasing programs) or the Public App Store. What’s important is to ensure that the App Configuration Policy you will create later targets the same app source (VPP Or Public App Store).
- Assign the App to the target User/Device Group for assignment.
Supervised Devices
These are company owned devices enrolled via the Apple Device Enrollment Program (ADE formerly DEP) or using Apple Configurator profiles. When you onboard a Supervised Device into MDE, it does not create a local loopback VPN.
At a high-level, you need an App Configuration Policy and a Device Configuration Policy targeted to these devices.
Step1: App Configuration Policy for Supervised Devices
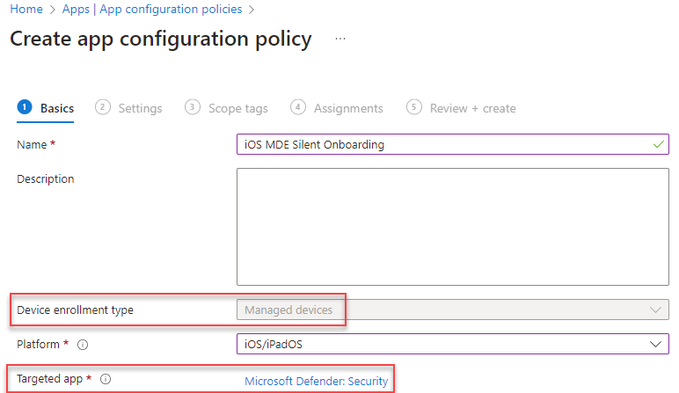
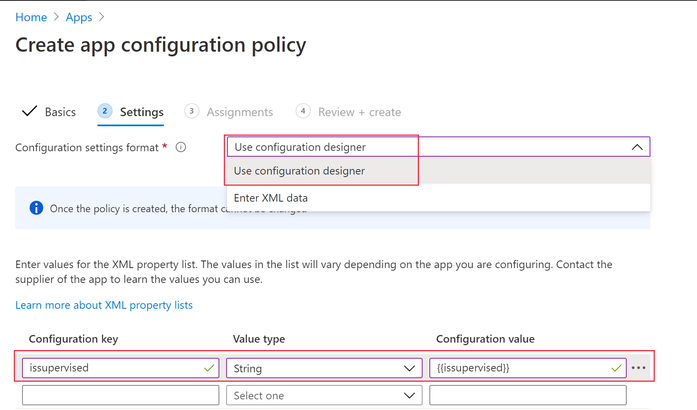
- From the Intune Console create an App Configuration policy of Managed devices type with Microsoft Defender as the target App.
- In the Settings page, select Use configuration designer and add issupervised as the key, value type as String, value as {{issupervised}}
- Assign the policy to the target Device Group for assignment.
Step2: Device Configuration Profile for Supervised Devices
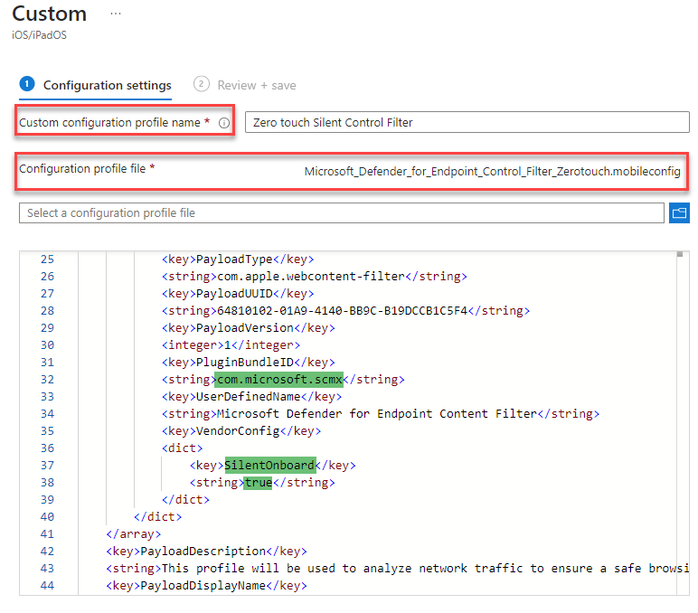
The next step is to create a Custom Configuration Profile which enables Web Protection without the need for any local loopback VPN.
- Download the Configuration file from: https://aka.ms/mdeiosprofilesupervisedzerotouch
- Specify a profile name and browse to the location of .mobileconfig file you downloaded from the link above.
- Assign the policy to the target Device Group for assignment.
Screenshot of the custom .mobileconfig file highlighting the silent onboarding configuration.
Onboarding Experience
Since this is a silent enrollment of MDE, the end user would only notice the MDE App installed. They do not need to launch the app for any activation. In the GIF below you will notice before the MDE App is installed, I am able to browse a malicious site (https://smartscreentestratings2.net) and after the deployment and silent configuration of MDE the same site is immediately blocked by Defender.
Unsupervised Devices
These devices are primarily BYOD or Corporate owned devices however not enrolled via Apple ADE/Configurator profiles. These devices are enrolled through App or Web-based Device Enrollment scenario.
Please note that Apple User Enrollment does not support MDE Zero-Touch silent enrollment, refer my previous blog post for deployment guidance: Onboarding Intune Managed iOS User Enrollment Devices to Microsoft Defender for Endpoint - Microsoft Community Hub
A VPN is created for Web Protection Feature on Unsupervised devices. This is not a regular VPN and is a local/self-looping VPN that does not take traffic outside the device.
VPN FAQ: Will this conflict with my corporate VPN?
Guidance: Use a Per-App VPN profile to allow your Enterprise Apps access to corporate resources while leaving the Defender Device-Wide VPN to protect the device. Alternatively, if you switch to Microsoft Tunnel as your corporate VPN gateway, the Defender App will suffice both the requirements.
Configuration
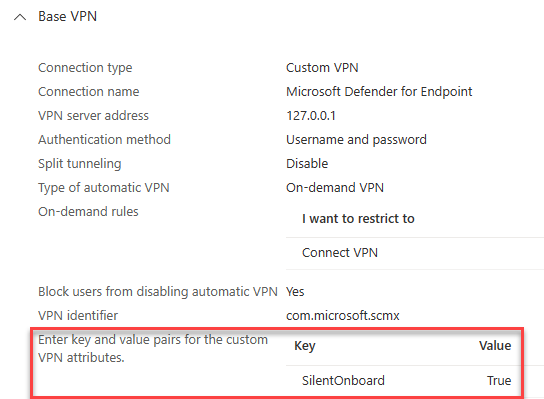
For these devices all you need is a Configuration Profile of type VPN.
- This is a Custom VPN profile, for instructions refer our learn docs here.
- Assign the policy to the target Device Group for assignment.
The key differentiator is the Key-value pair highlighted in the screenshot below which enables Silent onboarding of the Defender VPN profile.
Onboarding
The device onboarding experience is like Supervised device as called out in the GIF above. As an end user one would only notice the MDE App installed. They do not need to launch the app for any activation.
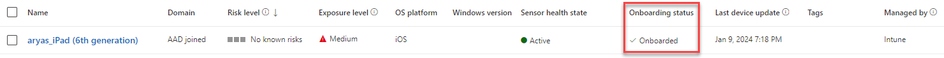
Post enrollment the device reports to the Microsoft Defender Security Portal.
The device name in Defender for Endpoint console is of the format <username_iPhone/iPad model>. You can also use Microsoft Entra device ID to identify the device in the Defender for Endpoint console.
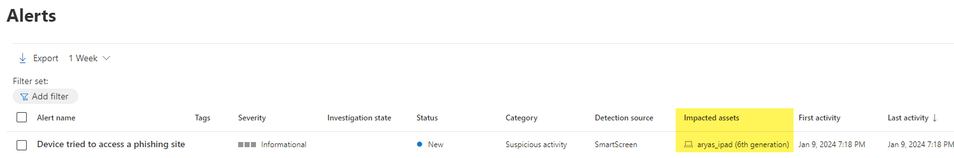
Additionally, you will see an active Alert from the suspicious site browsed by the user on that device.
Things to know.
- MAM Conditional App launch requirement for Defender App existence will interfere with the zero-touch experience since it requires the user to launch the app.
- New devices leveraging JIT Registration or Setup Assistant with Modern Auth may have an initial delay of around 5 minutes before MDE zero touch silent onboarding. This is the time between the Authenticator app registering the device and triggering MDE onboarding.
Thanks,
Arnab Mitra
Special thanks to Michael and Yuji for their valuable inputs in this blog post.