This post has been republished via RSS; it originally appeared at: Microsoft Tech Community - Latest Blogs - .
Microsoft Defender for Cloud (MDC) has been instrumental in offering proactive security management through its detailed Attack Path insights, helping organizations identify and mitigate potential vulnerabilities before they can be exploited. While these insights have long provided value within the MDC portal and through one-time snapshots via Azure Resource Graph, a significant update enhances how organizations can leverage this information. The introduction of continuous export capabilities for these insights represents a transformative step forward, enabling the integration of MDC's proactive security intelligence with external analytical tools and solutions over extended periods.
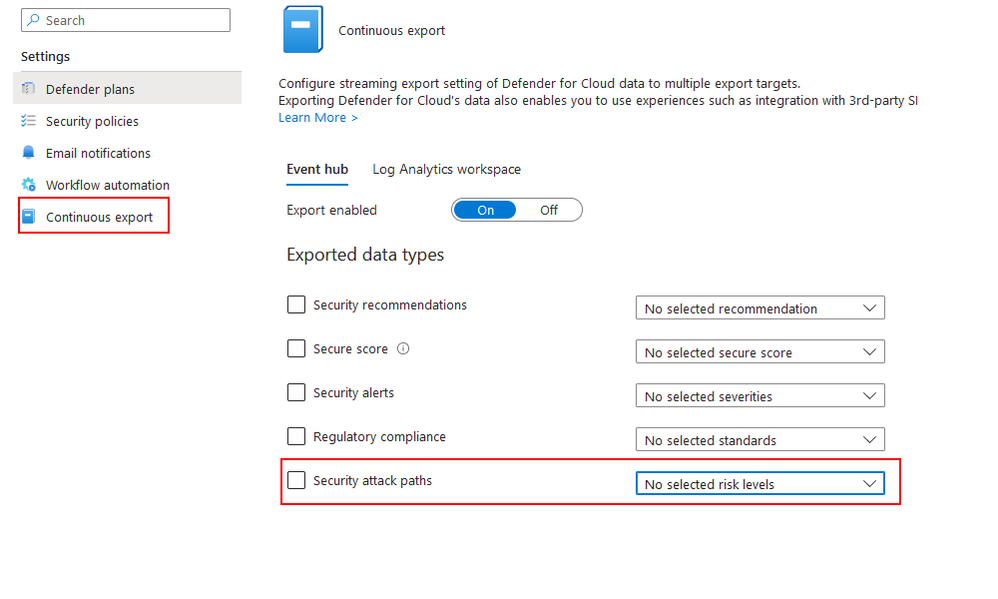
How to Enable Continuous Export in Defender for Cloud
To enable continuous export for Microsoft Defender for Cloud, you need to follow these steps:
- Sign in to the Azure Portal.
- Search for and select Microsoft Defender for Cloud.
- In the Defender for Cloud menu, select Continuous Export.
- Select the subscription or workspace that you want to export data from.
- Select the type of data you want to export (Security Attack Path).
- Select the export destination (Log Analytics workspace or Event Hub).
- Configure the export settings according to your needs.
- Select Save.
You can find more detailed instructions and screenshots in the official documentation.
Empowering Long-Term Security Analysis
The ability to continuously export Attack Path insights to a chosen destination, such as Azure Log Analytics or through Azure Event Hub to other repositories, empowers organizations with the capability to conduct long-term security analysis. Organizations can now collect and analyze Attack Path data over time, offering unprecedented visibility into the evolution of their security posture and the effectiveness of their mitigation strategies. This enduring analysis provides a dynamic view of how threat vectors evolve, enabling security teams to adapt their defenses in line with emerging trends and patterns.
A use case includes an organization using the continuous export feature to funnel Attack Path insights into a data repository such as Azure Log Analytics, an Azure Data Explorer, or a data lake where historical data accumulates over several months. By querying the data or applying machine learning models to this data, the organization can identify trends in vulnerability exploitation attempts and predict future attack vectors. This predictive analysis allows for the preemptive strengthening of security measures in areas most likely to be targeted next, based on the evolution of threat actors' tactics and techniques observed over time.
Custom Alerting and Notification Systems
With the continuous export of Attack Path data, organizations can establish custom alerting systems that are fine-tuned to their unique environment. By analyzing trends and detecting anomalies, these systems can trigger alerts for specific patterns that indicate a potential threat. For instance, an uptick in attack paths against a critical resource of an application or service could automatically generate a notification, prompting immediate action.
Consider an e-commerce platform where transaction security is paramount. The company could configure alerts for attack paths trends involving their payment processing system. Early warning of these potential vulnerabilities could be the difference between a minor incident and a significant breach, preserving customer trust and business continuity.
Strategic Advancements in Compliance and Reporting
The ability to analyze Attack Path insights over extended periods significantly streamlines compliance and reporting efforts. Organizations can demonstrate sustained compliance with regulatory requirements by providing historical data that showcases ongoing security management and vulnerability mitigation efforts, making audit processes more efficient and comprehensive.
Proactive Incident Response with Historical Context
Integrating continuous Attack Path insights into incident response strategies enriches the context for security investigations. By examining how hypothetical attack vectors have evolved and been addressed over time, security teams can better predict attacker behavior and refine their defensive strategies. This historical perspective not only aids in responding to incidents but also in preparing for potential future threats, enhancing overall security resilience.
For example, during an incident, a security team quickly queries the historical Attack Path data to identify if the current threat vector has been previously predicted or observed. Discovering a match, they leverage established remediation steps that were formulated based on past insights, significantly speeding up the response time. Furthermore, this historical data provides clues to potential lateral movement paths, enabling the team to proactively secure likely next targets.
Benchmarking and Security Performance Metrics
Data-driven decision-making is at the heart of modern cybersecurity strategies. By leveraging the continuous export of Attack Path data, organizations can benchmark their security performance against industry standards or historical performance. Metrics such as Mean Time To Remediate (MTTR) or the rate of high-severity vulnerabilities identified and remediated become powerful indicators of progress and areas needing attention. By understanding how vulnerabilities emerge and evolve, security teams can prioritize their efforts more effectively, reducing MTTR and strengthening their defenses against potential attacks.
A financial institution uses benchmarking to discover that their MTTR for critical vulnerabilities is above the industry average. This insight drives a targeted initiative to streamline their incident response processes, resulting in a measurable decrease in MTTR over the following year.
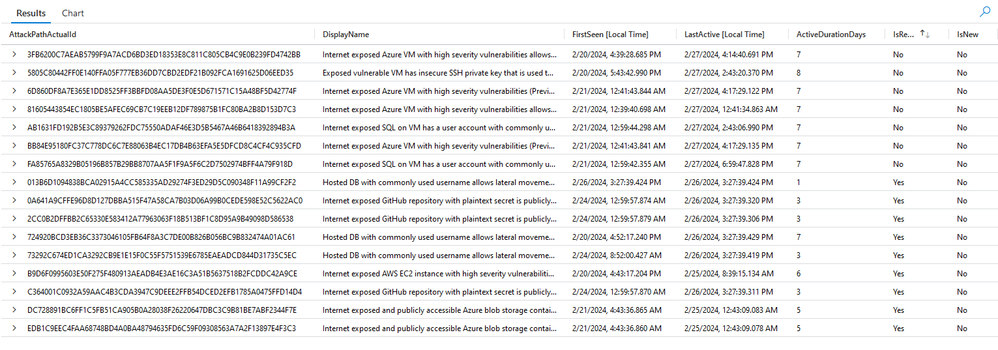
Imagine storing the data in an Azure Log Analytics workspace. An organization can utilize a KQL query to extract meaningful insights and monitor the MTTR of the attack vectors discovered, an essential metric that reflects the security team's efficiency.
The organization can develop a simple query like this:
let endDate = startofday(datetime_add('day', 0, now())); // Sets the end date to the start of today
let startDate = datetime_add('day', -30, endDate); // Sets the start date to 30 days before the end date
let lastFullDay = startofday(datetime_add('day', -1, now())); // The last full day covered by the analysis
let today = startofday(now());
let yesterday = startofday(datetime_add('day', -1, now()));
SecurityAttackPathData
| where TimeGenerated >= startDate and TimeGenerated < endDate
| extend AttackPathActualId = tostring(split(AttackPathId, "/attackPaths/")[1])
| summarize FirstSeen=min(TimeGenerated), LastActive=max(TimeGenerated) by AttackPathActualId, DisplayName
| extend ActiveDurationDays = datetime_diff('day', LastActive, FirstSeen) + 1
| extend IsResolved = iff(LastActive < lastFullDay, "Yes", "No")
| extend IsNew = iff(FirstSeen >= yesterday, "Yes", "No")
| project AttackPathActualId, DisplayName, FirstSeen, LastActive, ActiveDurationDays, IsResolved, IsNew
| order by AttackPathActualId asc
or:
// Define the time frame for analysis
let endDate = startofday(datetime_add('day', 0, now())); // Sets the end date to the start of today
let startDate = datetime_add('day', -30, endDate); // Sets the start date to 30 days before the end date
let lastFullDay = startofday(datetime_add('day', -1, now())); // The last full day covered by the analysis
// Query to fetch and process Attack Path data
SecurityAttackPathData
| where TimeGenerated >= startDate and TimeGenerated < endDate
| extend AttackPathActualId = tostring(split(AttackPathId, "/attackPaths/")[1])
| summarize FirstSeen=min(TimeGenerated), LastSeen=max(TimeGenerated) by AttackPathActualId, DisplayName
| extend IsResolved = iff(LastSeen < lastFullDay, "Yes", "No")
| extend IsNew = iff(FirstSeen >= datetime_add('day', -1, endDate), "Yes", "No")
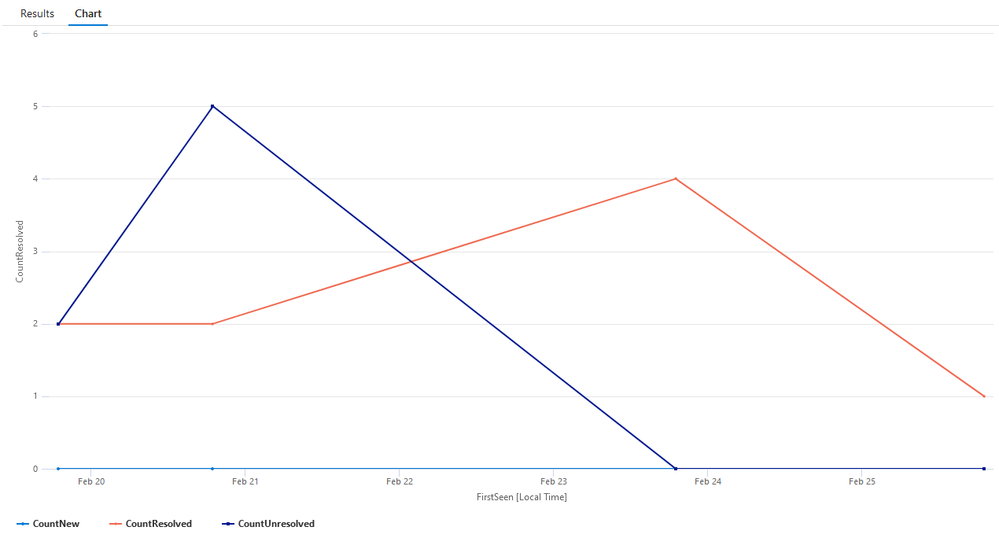
// Count the occurrences of resolved, unresolved, and new statuses for each day
| summarize CountResolved = countif(IsResolved == "Yes"), CountUnresolved = countif(IsResolved == "No"), CountNew = countif(IsNew == "Yes") by bin(FirstSeen, 1d)
// Plot the counts over time
| render timechart
and been able to monitor how long it has been taken for the attack vector to be fully remediate (MTTR), an important metric to measure the efficiency of the Security Team.
Security Posture Dashboarding
The real-time nature of continuous export means that security dashboards can now reflect the most current data on an organization's security posture. These dashboards can become the central hub for monitoring key security metrics, such as the number of active versus resolved attack paths and the average MTTR. Such at-a-glance visibility ensures that all stakeholders, from technical teams to executive leadership, are aware of the organization’s security status and can make informed decisions.
Enhancing Security Integration and Automation
With the new export capabilities, Attack Path insights can be seamlessly integrated into a broader security ecosystem, including SIEM systems, automation tools, and custom analytical platforms. This integration allows for the automation of response actions based on specific Attack Path data, improving the efficiency and effectiveness of security operations.
Conclusion
The enhanced capability to continuously export Attack Path insights from Microsoft Defender for Cloud marks a pivotal development in cybersecurity management. It extends the value of these proactive insights beyond the MDC portal, enabling organizations to analyze and leverage this data over time and integrate it with other security solutions. This update not only enriches the existing security workflows but also opens up new possibilities for strategic security analysis, compliance reporting, and incident response, ensuring that organizations can maintain a robust defense against evolving cyber threats.
Reviewers
Yuri Diogenes, Principal PM Manager, CxE, Microsoft Defender for Cloud
Tal Rosler, Senior PM Lead, Microsoft Defender for Cloud