This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Community Hub.
In the realm of cybersecurity, the ability to efficiently comprehend and utilize logs within Azure subscriptions for threat hunting is paramount. These investigations typically involve meticulous log analysis aimed at identifying the initial breach and the subsequent actions executed by the Threat Actor. This blog post delves into various strategies and methodologies designed to enhance our grasp of the scope and complexity of how threat actors' manoeuvre within Azure subscriptions, thereby fortifying our defenses against the ever-evolving landscape of cyberattacks.
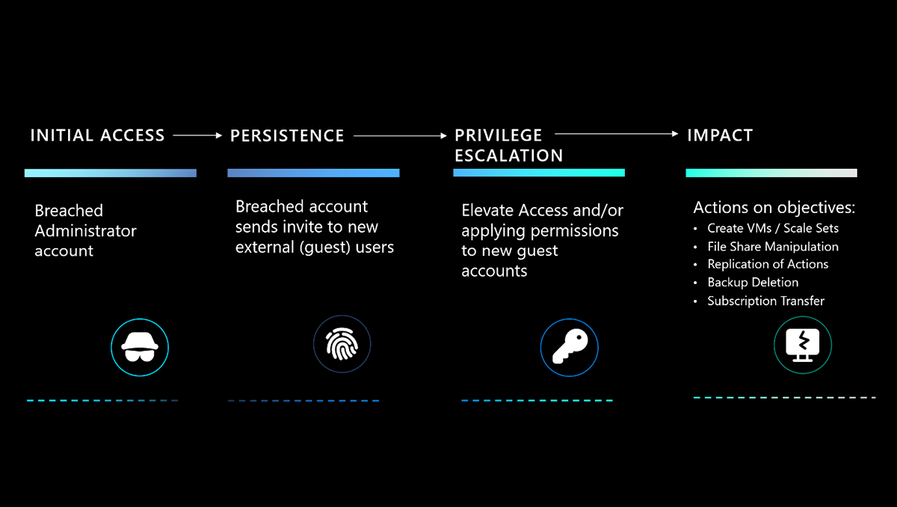
Example Azure attack scenario
To better understand the intricacies involved, let us consider a hypothetical attack scenario:
Figure 1: Diagram of hypothetical attack scenario
Breached Global Administrator Account: The attack commences with a "Pass the Cookie" assault on the global administrator's identity. This type of credential theft involves an adversary stealing a user's session cookie to gain unauthorized access to their account. With the compromised admin account, the adversary gains entry to the Azure subscription via the portal or Azure management API (application programming interfaces). For more information on “Pass the Cookie” attacks, check out Token tactics: How to prevent, detect, and respond to cloud token theft | Microsoft Security Blog
External user invite and privilege elevation: Leveraging the hijacked administrator account, the adversary proceeds to extend access to external users, elevating their privileges to authoritative roles such as a Subscription Owner or Contributor. This step aims to establish a persistent presence within the tenant, providing the adversary with a reliable re-entry point and sufficient permissions to fulfil their malicious objectives.
Action on objective: The adversary's commonly observed action on objectives may include:
- Virtual Machine Creation: Attackers often set up virtual machines or scale sets within the compromised environment, harnessing them for crypto-mining operations—a silent heist of computational resources.
- File Share Mounting: By mounting file shares, they lay the groundwork for further nefarious activities, setting the stage for data manipulation or exfiltration.
- File Share Encryption: A classic hallmark of ransomware, this tactic locks down file shares, holding data hostage in exchange for a ransom—a digital extortion that can bring businesses to their knees.
- Replication: Through replication, attackers ensure their presence is mirrored across subscriptions, a strategy that complicates eradication and bolsters their resilience within the network.
- Azure Backup Deletion: By deleting Azure backups, they aim to sever the lifelines of data recovery, pushing organizations towards the precipice of data loss.
- Subscription Transfer: When an attacker gains administrative access, they then could move subscriptions from the compromised tenant to one under their control.
Forensic data
For better forensic data analysis, it is important to know where Azure logs are and how to access them. By default, Azure saves control plane logs (also called Management Plane logs) in Azure Monitor which records operations like creating, deleting, or modifying a resource. But data plane logs which are specific to each resource, such as Blob Storage Access logs, are separate and need to be turned on for each resource through Azure Diagnostics Settings in the resource configuration. In this blog, we will focus on Azure Monitor Activity logs together with Microsoft Entra ID Audit Logs, however below you can see a data flow diagram for the default and potential locations of the different types of logs which may be useful during an Azure investigation.
Figure 2: Diagram of data flow for logs relating to Azure investigations
Pre-requisites to collect data for use in M365 Defender
To collect data, Defender for Cloud Apps requires the following connectors to be enabled:
- Azure connector for Azure Resources Management (ARM) events
- Office 365 connector for AAD (Azure Active Directory) management events
- Microsoft 365 Defender onboarded
Pre-requisites to collect data for use in Log Analytics
- Create a Log Analytics workspace in an Azure Subscription
- Set up Diagnostic settings in Microsoft Entra ID to configure Audit Logs to be sent to the Log Analytics workspace
- Set up Diagnostic settings in Azure Activity and configure the Logs to be sent to the Log Analytics workspace
Hunting guidance
In this section, we will delve into some key activities you can look out for to quickly identify potential security incidents. Some of these activities include:
- Detecting suspicious activities on existing accounts: Keep an eye out for user accounts used to create new guest accounts with privileged roles in your tenant or any activation of the ‘Elevate Access’ operation.
- Monitoring guest account privilege changes: Be vigilant about guest accounts being promoted to privileged Microsoft Entra ID roles. Sudden privilege escalations can be a red flag for malicious activities.
- Tracking guest account modifications: Set up Kusto queries to monitor guest accounts involved in modification operations (create, update, or delete) on cloud resources. Any unauthorized changes should be investigated promptly.
- Investigating suspicious ARM activities: Pay close attention to any unusual ARM activities, especially those that deviate from expected patterns. Anomalies in resource provisioning or configuration changes may indicate a security incident.
- Identifying High-Risk sign-ins: Utilize Kusto queries to pinpoint users who have experienced 'high risk sign-ins' and have also been involved in creating resource groups. This correlation can help identify potentially compromised accounts or malicious actors within your environment.
Investigating using Microsoft Defender for Cloud Apps
Microsoft Defender for Cloud Apps is an advanced security solution that fortifies cloud-based applications across Microsoft 365 and additional SaaS providers. It offers a suite of investigative features that are particularly beneficial in the context of the case study mentioned above, including:
Activity log: Keep track of all activities by external user accounts with administrative privileges by utilizing the Microsoft Defender portal "Cloud Apps" tab, then navigate to "Activity log." Apply a filter for "Microsoft Azure" and “External Users” and select the appropriate "Action type." These filters can also be used to create custom new policies.
Figure 3: Diagram showing a Defender for Cloud Apps filter for external users performing actions against Azure
Advanced Hunting: Another powerful tool at your disposal is Advanced Hunting, which can help you hunt for unusual activities within your Azure subscriptions. The Advanced Hunting portal will display results from historical data spanning 30 days.
By watching out for these activities using Advanced Hunting queries, you can proactively detect and respond to security threats in your Azure environment. Remember, staying ahead of potential incidents is key to maintaining a secure and resilient cloud infrastructure. Incorporate these strategies into your security operations to strengthen your defense against evolving cyber threats.
Example useful Advanced Hunting queries:
Figure 4: Screenshot of output from query
Figure 5: Screenshot of output from high risk activities in Azure queries
Detecting suspicious activity with Activity policies: A crucial tool in cloud monitoring, Activity policies in Microsoft Defender for Cloud Apps allow you to track your organization's cloud activities effectively. Notifications are triggered based on policy results, and users can be suspended from cloud apps as needed. An Activity policy comprises the following components:
- Activity filters: These enable the creation of precise conditions based on metadata.
- Activity match parameters: These allow you to define thresholds for activity repetition to trigger policy matches. For instance, you can set a policy to alert when an external user creates multiple virtual machines in Azure.
- Repeated activity settings: Here, you can configure the number of repeated activities needed and the timeframe for these to occur to trigger the policy.
- Actions: The policy includes a range of governance actions that can be automatically enforced upon detecting violations.
Figure 6: Example Activity policy
Investigating using Microsoft Azure
Microsoft Azure is Microsoft’s public cloud computing platform, providing a broad range of configurable security options and the ability to control them so that they can be customized to meet unique requirements. We will take a closer look at two of these security options using the above case study:
Azure Monitor Activity Log: The Azure Monitor Activity Log is a comprehensive log within Azure that offers visibility into actions taken at the subscription level. The entries in Activity Logs include control plane changes only. It records all modification operations (create, update, or delete) on cloud resources, a good example being when a virtual machine is started or stopped. The activity logs can be filtered at the subscription level or resource-level. Activity log events are retained in Azure for 90 days and then deleted but for more functionality, the diagnostic settings can be used to increase retention based on your needs. By default, the control plane logs are collected. To collect data from the data plane, diagnostics settings need to be enabled on each resource.
Figure 7: Snippet of Azure Monitor activity log
Continuously monitor for any unusual activities and verify their legitimacy. Additionally, keep an eye on the Metrics tab for any unexpected spikes in activity. A significant increase in outbound data transfer, measured in megabytes, could signal unauthorized data exfiltration. Similarly, a series of consecutive virtual machine creations warrants further investigation.
Azure Log Analytics: Azure Log Analytics stands out as another powerful tool in your arsenal. It's a service designed to monitor your resources and applications across both cloud and on-premises environments. This tool empowers you to perform crucial tasks such as searching, analyzing, and visualizing data using the powerful Kusto Query Language (KQL).
Setting up a log analytics workspace is the first step, acting as a virtual container to store logs efficiently. These logs can originate from diverse sources like Activity logs, ARM logs, and Microsoft Entra ID Audit Logs, boasting extended retention periods for your convenience.
Figure 8: Example showing Microsoft Entra ID logs being sent to a Log Analytics workspace
For investigating the previously described attack scenario using Azure Log Analytics, you'll want to direct both Microsoft Entra ID Audit logs and Azure Activity logs to Log Analytics. In the Advanced Hunting feature, these logs are consolidated in the CloudAppEvents table, while Log Analytics organizes this data into the AuditLogs and AzureActivity tables respectively.
Example useful Log Analytics queries:
Figure 9: Screenshot of query hunting for suspicious Azure role assignments
Diagnostic settings
Setting up and customizing diagnostic settings is essential for resources that demand heightened data plane monitoring, such as Key Vaults, Storage accounts, and others. If diagnostic settings are not configured it can limit visibility into activities such as reconnaissance, credential access, data exfiltration, and other malicious behaviours. Diagnostic logs play a crucial role in identifying actions such as identifying the entity accessing a data store or a secret, logging failed API attempts towards web services or databases, and much more. Enabling Diagnostic settings incurs a cost. It is recommended to use Azure Policy to enforce Diagnostic settings configuration on critical resources to ensure you have the proper logging enabled. You can either utilize the built-in policy definitions that Azure Policy already has for Diagnostic settings, or you can build you own custom policy.
Conclusion
In conclusion, cloud investigation in Azure subscriptions is multi-faceted and a crucial aspect of maintaining a secure and resilient cloud environment. By understanding and utilizing logs effectively and ideally bringing them into a central location, organizations can enhance their threat hunting capabilities and proactively identify potential security threats and vulnerabilities. Azure provides robust logging and monitoring tools that can be leveraged to gain insights into system activities, detect anomalies, and respond promptly to security incidents. Integrating best practices for log management, analysis, and incident response is essential for organizations to stay ahead of evolving cyber threats and safeguard their sensitive data and assets in the cloud.