This post has been republished via RSS; it originally appeared at: Microsoft Security Blog.
Executive summary
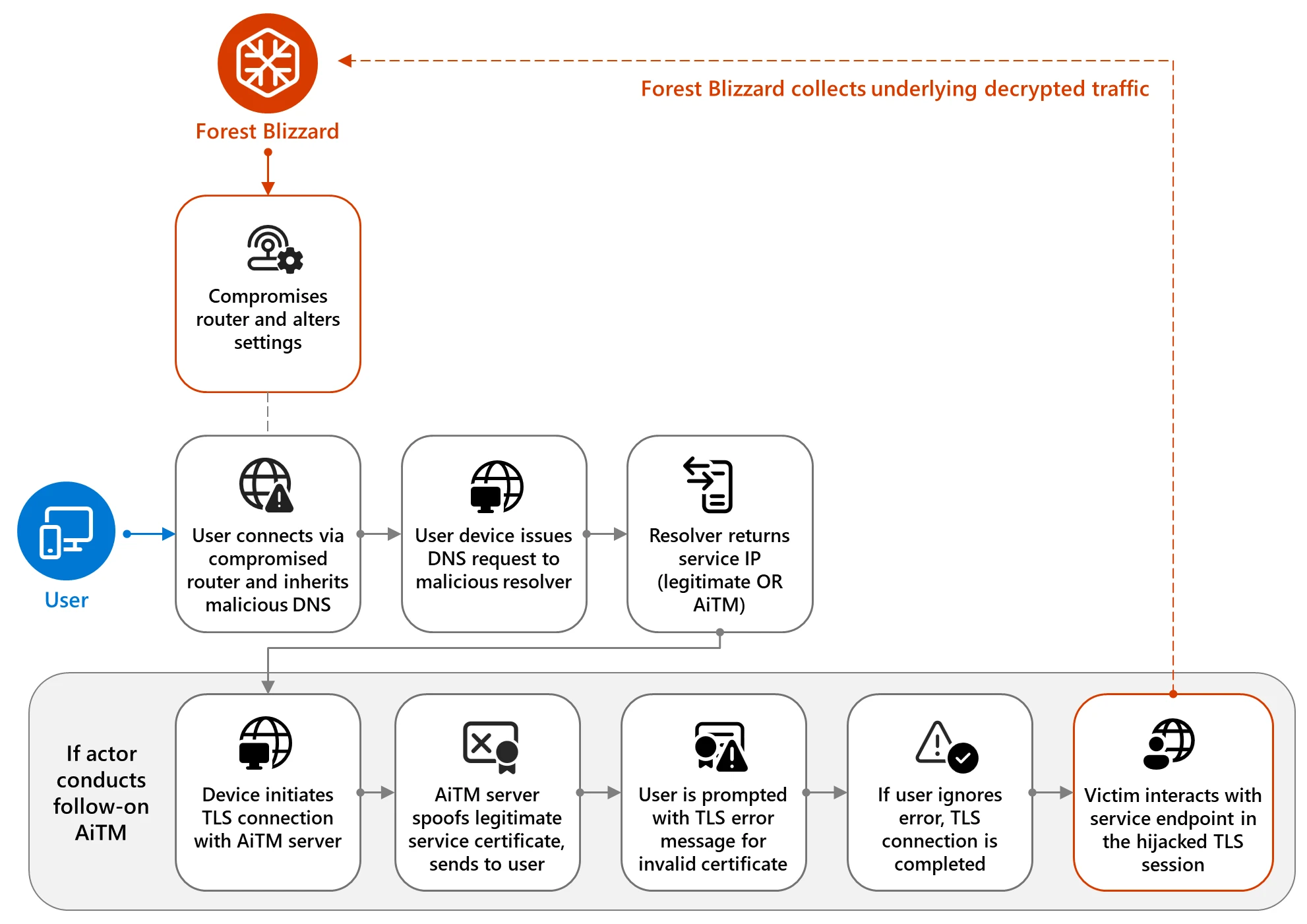
Forest Blizzard, a threat actor linked to the Russian military, has been compromising insecure home and small-office internet equipment like routers, then modifying their settings in ways that turn them into part of the actor’s malicious infrastructure. The threat actor then hides behind this legitimate but compromised infrastructure to spy on additional targets or conduct follow-on attacks. Microsoft Threat Intelligence is sharing information on this campaign to increase awareness of the risks associated with insecure home and small-office internet routing devices and give users and organizations tools to mitigate, detect, and hunt for these threats where they might be impacted.
Since at least August 2025, the Russian military intelligence actor Forest Blizzard, and its sub-group tracked as Storm-2754, has conducted a large-scale exploitation of vulnerable small office/home office (SOHO) devices to hijack Domain Name System (DNS) requests and facilitate the collection of network traffic. For nation-state actors like Forest Blizzard, DNS hijacking enables persistent, passive visibility and reconnaissance at scale.
By compromising edge devices that are upstream of larger targets, threat actors can take advantage of less closely monitored or managed assets to pivot into enterprise environments. Microsoft Threat Intelligence has identified over 200 organizations and 5,000 consumer devices impacted by Forest Blizzard’s malicious DNS infrastructure; telemetry did not indicate compromise of Microsoft-owned assets or services.
Forest Blizzard, which primarily collects intelligence in support of Russian government foreign policy initiatives, has also leveraged its DNS hijacking activity to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains. This activity enables the interception of cloud-hosted content, impacting numerous sectors including government, information technology (IT), telecommunications, and energy—all usual targets for this actor.
While the number of organizations specifically targeted for TLS AiTM is only a subset of the networks with vulnerable SOHO devices, Microsoft Threat Intelligence assesses that the threat actor’s broad access could enable larger-scale AiTM attacks, which might include active traffic interception. Targeting SOHO devices is not a new tactic, technique, or procedure (TTP) for Russian military intelligence actors, but this is the first time Microsoft has observed Forest Blizzard using DNS hijacking at scale to support AiTM of TLS connections after exploiting edge devices.
In this blog, we share our analysis of the TTPs used by Forest Blizzard in this campaign to illustrate how threat actors leverage this attack surface. We’re also outlining mitigation and protection recommendations to reduce exposure from compromised SOHO devices, as well as Microsoft Defender detection and hunting guidance to help defenders identify and investigate related malicious activity. It’s important for organizations to account for unmanaged SOHO devices—particularly those used by remote and hybrid employees—since compromised home and small‑office network infrastructure can expose cloud access and sensitive data even when enterprise environments and cloud services themselves remain secure.
DNS hijacking attack chain: From compromised devices to AiTM and other follow-on activity
The following sections provide details on Forest Blizzard’s end-to-end attack chain for this campaign, from initial access on vulnerable SOHO routers to actor-controlled DNS resolution and AiTM activity.
Edge router compromise
Forest Blizzard gained access to SOHO devices then altered their default network configurations to use actor-controlled DNS resolvers. This malicious re-configuration resulted in thousands of devices sending their DNS requests to actor-controlled servers.
Typically, endpoint devices obtain network configuration settings from edge devices through Dynamic Host Configuration Protocol (DHCP). Exploiting SOHO devices requires minimal investment while providing wide visibility on compromised devices, allowing the actor to collect DNS traffic and passively observe DNS requests, which could facilitate follow-on collection activity as described in the next section.
DNS hijacking
Forest Blizzard is almost certainly using the dnsmasq utility to perform DNS resolution and provide responses while listening on port 53 for DNS queries. The dnsmasq utility is a legitimate tool that provides lightweight network services widely used in home routers or smaller networks. Among its services are DNS forwarding and caching and a DHCP server, which collectively enable upstream DNS query forwarding and IP address assignment on a local network.
Adversary-in-the-middle attacks
Microsoft Threat Intelligence has observed AiTM attacks related to the initial access campaign. Although they target different endpoints, both are Transport Layer Security (TLS) AiTM attacks, allowing the threat actor to collect data being transmitted.
In most cases, the DNS requests appear to have been transparently proxied by the actor’s infrastructure, resulting in connections to the legitimate service endpoints without interruption. However, in a limited number of compromises, the threat actor spoofed DNS responses for specifically targeted domains to force impacted endpoints to connect to infrastructure controlled by the threat actor.
The actor-controlled malicious infrastructure would then present an invalid TLS certificate to the victim, spoofing the legitimate Microsoft service. If the compromised user ignored warnings about the invalid TLS certificate, the threat actor could then actively intercept the underlying plaintext traffic—potentially including emails and other customer content— within the TLS connection. Since Forest Blizzard does not always conduct AiTM activity after achieving initial access through DNS hijacking, the actor is likely using it selectively against targets of intelligence priority post-compromise:
- AiTM attack against Microsoft 365 domains: Microsoft observed Forest Blizzard conducting follow-on AiTM operations against a subset of domains associated with Microsoft Outlook on the web.
- AiTM attack against specific government servers: Microsoft identified separate AiTM activity targeting non-Microsoft hosted servers in at least three government organizations in Africa, during which Forest Blizzard intercepted DNS requests and conducted follow-on collection.
Possible post-compromise activities
Forest Blizzard’s DNS hijacking and AiTM activity allows the actor to conduct DNS collection on sensitive organizations worldwide and is consistent with the actor’s longstanding remit to collect espionage against priority intelligence targets. Although we have only observed Forest Blizzard utilizing their DNS hijacking campaign for information collection, an attacker could use an AiTM position for additional outcomes, such as malware deployment or denial of service.
Mitigation and protection guidance
Microsoft recommends the following mitigation steps to protect against this Forest Blizzard activity:
Protection against DNS hijacking
- Enforce domain-name-based network access controls using Zero Trust DNS (ZTDNS) on Windows endpoints to ensure that devices only resolve DNS through trusted servers.
- Block known or malicious domains to prevent DNS-based attacks, and maintain detailed DNS logs to monitor, investigate, and gain insight into anomalous DNS traffic.
- Follow best practices for enhancing network security for cloud computing environments.
- Enable network protection and web protection in Microsoft Defender for Endpoint to safeguard against malicious sites and internet-based threats.
- Avoid using home router solutions in corporate environments.
Protection against AiTM and credential theft
- Centralize your organization’s identity management into a single platform. If your organization is a hybrid environment, integrate your on-premises directories with your cloud directories. If your organization is using a third-party for identity management, ensure this data is being logged in a SIEM or connected to Microsoft Entra to fully monitor for malicious identity access from a centralized location.
- The added benefits to centralizing all identity data is to facilitate implementation of Single Sign On (SSO) and provide users with a more seamless authentication process, as well as configure Microsoft Entra’s machine learning models to operate on all identity data, thus learning the difference between legitimate access and malicious access quicker and easier.
- It is recommended to synchronize all user accounts except administrative and high privileged ones when doing this to maintain a boundary between the on-premises environment and the cloud environment, in case of a breach.
- Strictly enforce multifactor authentication (MFA) and apply Conditional Access policies, particularly for privileged and high‑risk accounts, to reduce the impact of credential compromise. Use passwordless solutions like passkeys in addition to implementing MFA.
- Use the Microsoft Authenticator app for passkeys and MFA, and complement MFA with Conditional Access policies, where sign-in requests are evaluated using additional identity-driven signals.
- Conditional Access policies can also be scoped to strengthen privileged accounts with phishing resistant MFA.
- Your passkey and MFA policy can be further secured by only allowing MFA and passkey registrations from trusted locations and devices.
- Implement continuous access evaluation and implement a sign-in risk policy to automate response to risky sign-ins. A sign-in risk represents the probability that a given authentication request isn’t authorized by the identity owner. A sign-in risk-based policy can be implemented by adding a sign-in risk condition to Conditional Access policies that evaluates the risk level of a specific user or group. Based on the risk level (high/medium/low), a policy can be configured to block access or force multi-factor authentication. We recommend requiring multi-factor authentication on Medium or above risky sign-ins.
- Follow best practices for recovering from systemic identity compromises outlined by Microsoft Incident Response.
Microsoft Defender detection and hunting guidance
Microsoft Defender customers can refer to the following list of applicable detections. Microsoft Defender coordinates detection, prevention, investigation, and response across endpoints, identities, email, apps to provide integrated protection against attacks like the threat discussed in this blog.
Microsoft Defender for Endpoint
The following alerts might indicate threat activity associated with this threat. These alerts, however, can be triggered by unrelated threat activity and are not monitored in the status cards provided with this report. Microsoft tracks the specific component of Forest Blizzard associated with this activity as Storm-2754.
- Forest Blizzard Actor activity detected
- Storm-2754 activity
Entra ID Protection
The following Microsoft Entra ID Protection risk detection informs Entra ID user risk events and can indicate associated threat activity, including unusual user activity consistent with known Forest Blizzard attack patterns identified by Microsoft Threat Intelligence research:
- Microsoft Entra threat intelligence (sign-in) (RiskEventType: investigationsThreatIntelligence)
Hunting
Because initial compromise and DNS modification occur at the router-level, the following hunting recommendations focus on detecting post-compromise behavior.
Modifications to DNS settings
In identified activity, Forest Blizzard’s compromise of an infected SOHO device resulted in the update of the default DNS setting on connected Windows machines.
- Identifying unusual modifications to DNS settings can be an identifier for malicious DNS hijacking activity.
- Resetting the DNS settings and addressing vulnerable SOHO devices can resolve this activity, though these actions will not remediate an attacker who has managed to steal user credentials in follow-on AiTM activity.
Post-compromise activity
Forest Blizzard’s post-compromise AiTM activity could enable the actor to operate in the environment as a valid user. Establishing a baseline of normal user activity is important to be able to identify and investigate potentially anomalous actions. For Entra environments, Microsoft Entra ID Protection provides two important reports for daily activity monitoring:
- Risky sign-in reports surfaces attempted and successful user access activities where the legitimate owner might not have performed the sign-in.
- Risky user reports surfaces user accounts that might have been compromised, such as a leaked credential that was detected or the user signing in from an unexpected location in the absence of planned travel.
Defenders can surface highly suspicious or successful risky sign-ins using the following advanced hunting query in the Microsoft Defender XDR portal:
AADSignInEventsBeta
| where RiskLevelAggregated == 100 and (ErrorCode == 0 or ErrorCode == 50140)
| project Timestamp, Application, LogonType, AccountDisplayName, UserAgent, IPAddress
After stealing credentials, Forest Blizzard could potentially carry out a range of activity against targets as a legitimate user. For Microsoft 365 environments, the ActionType “Search” or “MailItemsAccessed” in the CloudAppEvents table in the Defender XDR portal can provide some information on user search activities, including the Microsoft Defender for Cloud Apps connector that surfaces activity unusual for that user.
CloudAppEvents
| where AccountObjectId == " " // limit results to specific suspicious user accounts by adding the user here
| where ActionType has_any ("Search", "MailItemsAccessed")
Threat intelligence reports
Microsoft Defender XDR customers can use the following threat analytics reports in the Defender portal (requires license for at least one Defender XDR product) to get the most up-to-date information about the threat actor, malicious activity, and techniques discussed in this blog. These reports provide the intelligence, protection information, and recommended actions to prevent, mitigate, or respond to associated threats found in customer environments:
Microsoft Security Copilot
Microsoft Security Copilot is embedded in Microsoft Defender and provides security teams with AI-powered capabilities to summarize incidents, analyze files and scripts, summarize identities, use guided responses, and generate device summaries, hunting queries, and incident reports.
Customers can also deploy AI agents, including the following Microsoft Security Copilot agents, to perform security tasks efficiently:
- Threat Intelligence Briefing agent
- Phishing Triage agent
- Threat Hunting agent
- Dynamic Threat Detection agent
Security Copilot is also available as a standalone experience where customers can perform specific security-related tasks, such as incident investigation, user analysis, and vulnerability impact assessment. In addition, Security Copilot offers developer scenarios that allow customers to build, test, publish, and integrate AI agents and plugins to meet unique security needs.
Learn more
For the latest security research from the Microsoft Threat Intelligence community, check out the Microsoft Threat Intelligence Blog.
To get notified about new publications and to join discussions on social media, follow us on LinkedIn, X (formerly Twitter), and Bluesky.
To hear stories and insights from the Microsoft Threat Intelligence community about the ever-evolving threat landscape, listen to the Microsoft Threat Intelligence podcast.
The post SOHO router compromise leads to DNS hijacking and adversary-in-the-middle attacks appeared first on Microsoft Security Blog.
