This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Challenge:
Currently there is no official Azure Red Hat OpenShift (ARO) Reference Architecture that showcases how to deploy ARO in a typical enterprise environment. This may create confusion among customers on how to deploy ARO securely, integrate with various Azure services for securing ingress/egress traffic, monitoring, identity, etc. By the way, we are in the process of publishing official ARO Landing Zone Accelerator.
Solution:
Intent of this blog is to showcase Azure Red Hat OpenShift (ARO) Reference Architecture and Reference Implementation. This will allow customers to gain confidence and deploy ARO following some of the recommended best practices.
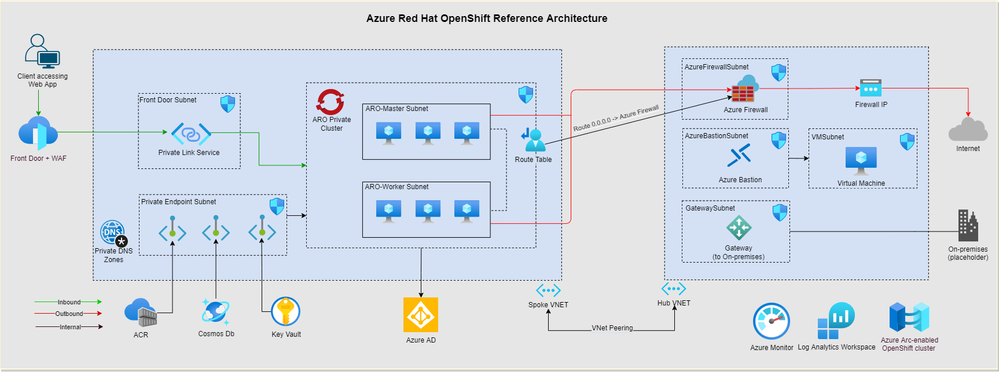
This Reference Architecture (RA) shows integrating ARO with several Azure services such as Azure Front Door + WAF for securely handling ingress traffic, Firewall for inspecting egress traffic to avoid data exfiltration, and Azure Active Directory for Role Based Access Control and so on. Also, this RA provides several recommended best practices for ARO deployment, from Networking best practices that supports multi-region growth, on-boarding the cluster on to Arc and enabling Container Insights to monitor the cluster and workload.
Reference Architecture:
Details of the Reference Architecture:
- Private ARO cluster deployed across AZs
- Integrate ARO with Azure AD for RBAC
- Azure Front Door + Web Application Firewall with Private Link Service to connect private IP address in ARO
- Azure Firewall for securing outbound traffic
- Provision Azure Bastion Host & Jumpbox VM to securely connect to ARO cluster and deploy a sample application manually
- Connect ARO cluster to Azure arc enabled kubernetes and install Container Insights extension for collecting logs through Log Analytics workspace
- [Optional] Azure Container Registry (ACR) with private endpoint for storing container images. ACR is used for sample workload deployment.
- [Optional] Azure Key Vault (AKV) with private endpoint for storing secretes/certificates in a centralized manner. AKV is used for sample workload deployment.
- [Optional] - Azure Cosmos DB with private endpoint for sample application backend. Cosmos DB is used to for sample workload deployment.
Reference Implementation:
Entire Reference Implementation on how to deploy above mentioned Reference Architecture using Azure CLI can be found under deployment folder in this GitHub repo. Bicep & Terraform modules are under work in progress.
Credit:
Credit goes to Victor Santana, Srikant Sarwa, Srini Padala & Melissa Verduci who helped immensely in putting together this Reference Architecture & Reference Implementation. Also, thanks to Sean McKenna, Kavitha Gowda, Rahul Mehta, Jim Zimmerman, Stuart Kirk & Tommy Hamilton for reviewing the same.