This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Hi Team, Eric Jansen here again, this time to add on to Joel Vickery's previous post discussing how to view the DNS Analytic Logs without having to disable them. It's a great read if you haven't already seen it…. however, there's been a very unfortunate death in the family since that posting...
It was a sad day when the news posted that Microsoft Message Analyzer was no more; because it was an extremely feature rich tool that myself and a lot of others still use today, albeit of the last release - that can no longer be downloaded. In situations like this one though, we must adapt and overcome, to find new ways to accomplish the same goals. This is where I thought I might be able to help empower you guys to be able to do more, using the power of PowerShell. Reading through online forums I’ve seen numerous posts where folks say that it’s not possible to view the DNS Analytical log while it’s running. I’m here to tell you guys that you absolutely can, and not just using the methods that Joel outlined in his blog.
As you may have noticed in part one of the series, I used several cmdlets that if you tried to follow along with the posting, wouldn’t have worked for you. That’s because they’re all custom functions that I’ve personally written, since I spend a fair amount of time digging around in these logs, just to make my life a bit easier. I've written a series of functions (Seven to be exact) to help with DNS Analytic Log configuration. As we move along through the series, I’ll likely share more of them, and at some point, I’ll see if I can muster up the motivation to setup a code repository on GitHub, if the interest is there.
For today’s topic though, I thought I'd share one of my shiny new functions, I call her…… Show-DNSAnalyticLog. I decided that I’d even reveal the magic behind the curtains (OK, it's not that magical, but it does what I want it to.). In reality, there’s only one real line that does the work in the wrapper-of-a-function that I wrote, and that's the line that uses Get-WinEvent, specifically with the use of the -Oldest parameter; that's the key.
So, let's take a look at this sample code and a few notes that I’ve added in there:
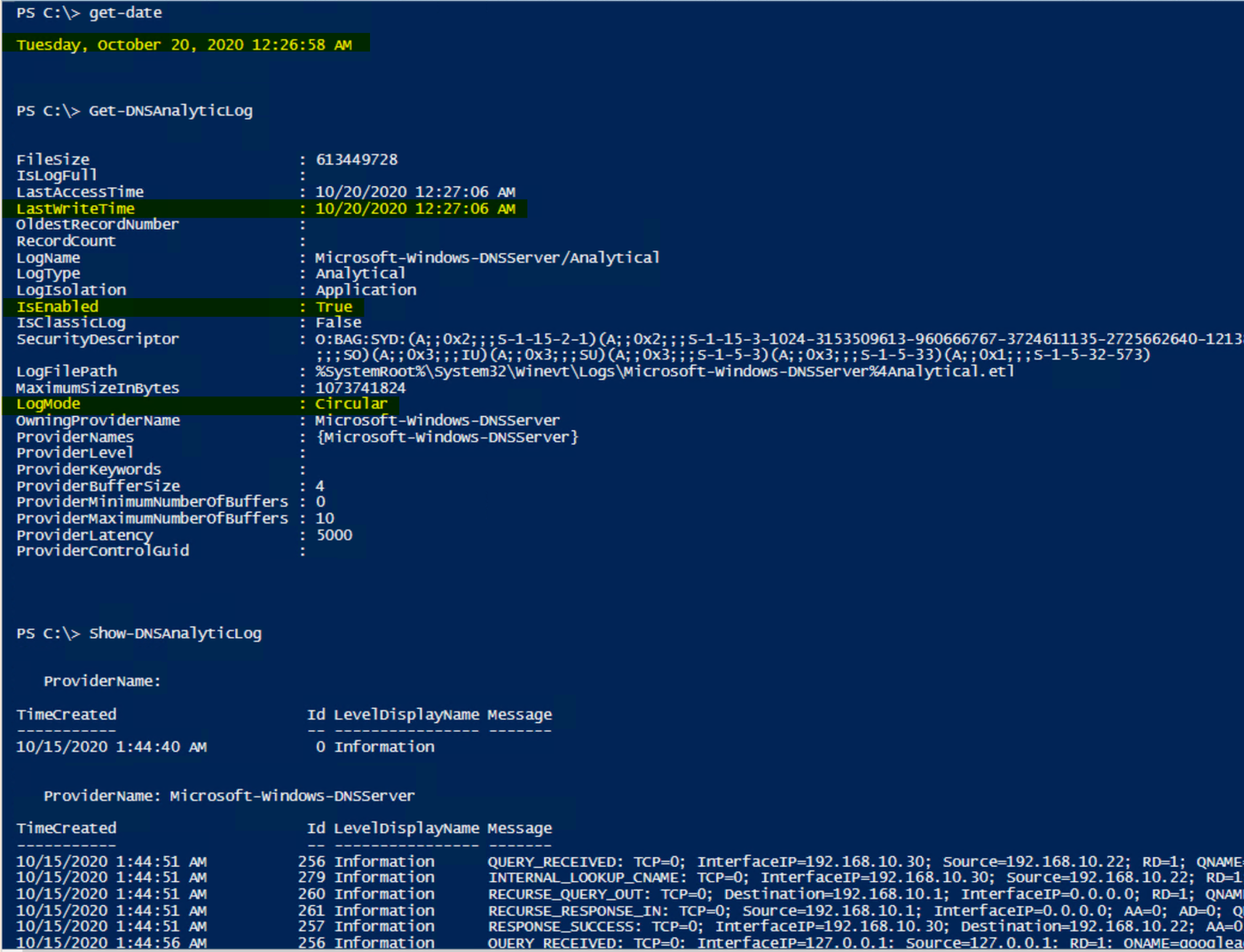
So, once you load that guy up, all you need to do is type Show-DNSAnalyticLog, and you’re off to the races. It’ll dump an unparsed / unfiltered list of events that’ll scroll down the screen until everything’s dumped out for your viewing pleasure. One thing to take into consideration though, is that when dumping ALL events (and there could be millions of them), then it could take a while before the scroll fest begins. Once it does though, it’ll look something like this…again, starting from the oldest created event, racing to catch up with the newest written event:
Note: The below just shows that the log is in fact enabled and was written to, even after I showed the current time, followed by the running of the function to show the events that are in the log.
Anyhow, nothing crazy, but if it can help someone else, then my job is done (for the time being).
But who wants unparsed / unfiltered logs when you’re on a hunt? Gross. Maybe we can talk about that in a future post. ;)
Until next time…