This post has been republished via RSS; it originally appeared at: Azure Active Directory Identity Blog articles.
Howdy folks,
Today I’ve got more exciting news to share. We’ve just turned on the public preview of Azure AD entitlement management!
Now Azure AD enables you to govern employee and business partner access to resources at enterprise scale with great compliance and auditing controls. Azure AD entitlement management removes barriers to internal and external collaboration by automating employee and partner access requests, approvals, auditing, and review for Office 365, for thousands of popular SaaS apps like ServiceNow, Workday, Google Apps, and Salesforce.com to any line of business app integrated with Azure AD.
Last year at Ignite, we outlined our vision for how to govern access to your resources with Azure Active Directory. The public preview of entitlement management, is the fourth module of Azure AD identity governance. (The other three modules, Privileged Identity Management (PIM), Terms of use, and Access reviews are already generally available.)
With the rapid adoption of SaaS apps and cloud services by business units, many central IT teams don’t have the knowledge to know which access rights which users should have. They have to delegate management of access approvals and review, such as having someone in the sales department determine what access rights someone in the sales team needs while maintaining strong compliance and security policies.
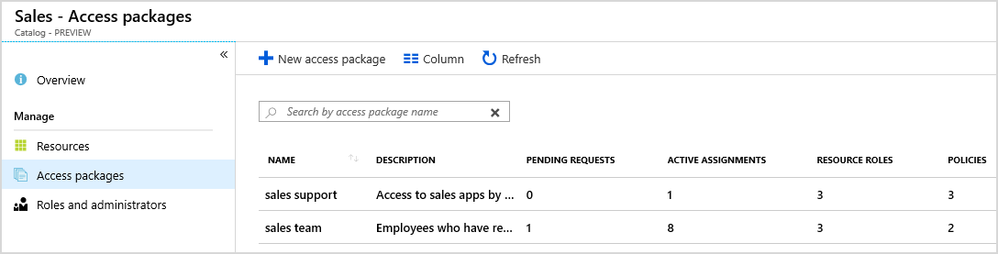
For example, if the Contoso sales division needs to enable more employees to work on sales support, they can create a “Sales Support” access package which includes the relevant memberships in Office 365 and Azure AD security groups, Microsoft Teams, role assignments in SaaS apps such as Salesforce, roles in their own apps, and access to SharePoint Online sites.
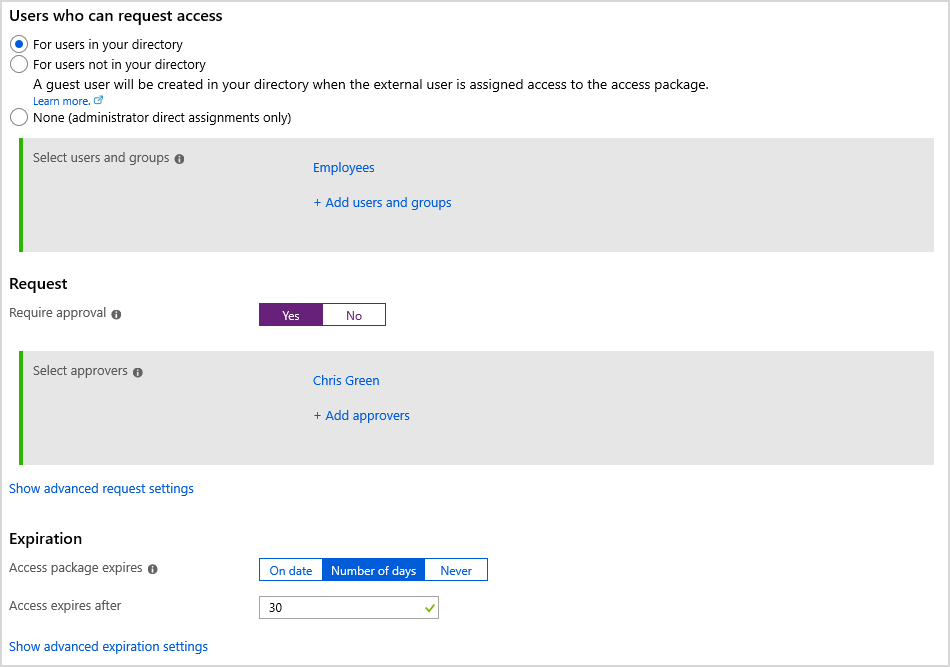
They can configure policies to include who can request this access package, who must approve, and how long the users who request will have access to these specific resources.
When an employee requests an access package, and their request is approved, the employee is automatically provisioned access to the groups, apps, and other resources in the access package.
Azure AD entitlement management works with Azure AD B2B to enable collaboration across business partners. Employees from a business partner can request access to resources using the same access packages and our policy engine, including provisioning their accounts upon approval by a business sponsor. This makes it simple to grant access to a specified set of resources for your business partners while knowing your processes are compliant and secure.
Regardless of how they got access, when a user’s access package assignment expires, their access rights are automatically removed, so you don’t need to remember to manually remove when a project is done.
With this preview, Azure AD now has:
- Access package request policies, so you can configure different approval workflows for different groups of employees or guests who might request access.
- Time-limited access for groups, apps, and sites, so users who are approved don’t retain access indefinitely—their access can be set to automatically expire.
We’ve been working with Avanade, which chose Azure AD to simplify the collaboration experience with their clients. Here’s what they had to say about entitlement management:
Learn more with the case study and video at Digital innovator Avanade chooses Azure AD Identity Governance for streamlined, highly secure collaboration.
Entitlement management along with the other Azure AD features—including Azure AD B2B, provisioning, Access reviews, Terms of use, and PIM—enable you to better protect, monitor, and, audit access to critical assets while ensuring employee and guest productivity.
To try these features in your own directory, sign in to the Azure portal as an administrator, and go to the Azure Active Directory > Identity governance section.
Note: Entitlement management is an Azure AD Premium P2 feature as part of Enterprise Mobility + Security (EMS) E5.
To learn more, look at the entitlement management overview and scenario guides, try it out, and let us know your feedback in the comments below.
Best regards,
Alex Simons (@Alex_A_Simons)
Corporate VP of Program Management
Microsoft Identity Division