In today’s security operation centers (SOCs), analysts have a large set of security solutions that they leverage to protect their organization and monitor activity. However, when setting up a SIEM it is challenging to prioritize what data to ingest and what protections each solution provides. SOCs must consider size and cost of ingestion, detections, and necessary use cases for each data source they would like to connect to their SIEM. Because of these considerations, SOCs should focus on ingesting data that is critical and has a low level of overlap to reduce the probability of double ingestion.
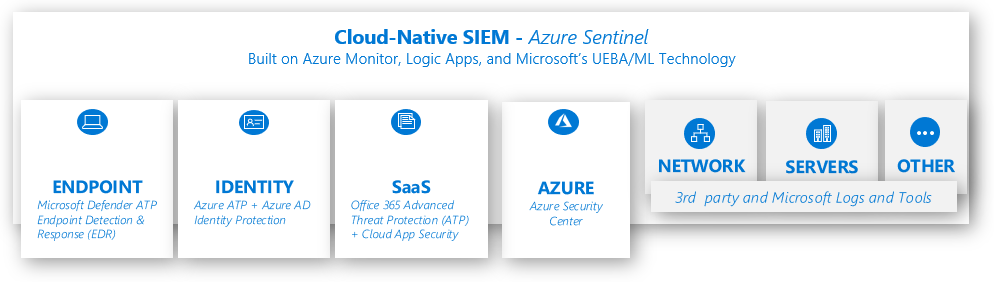
To aid SOCs as they navigate this challenge in understanding the value that each data source provides, the figure below (“Integrated Toolset”) can be used as a reference to understand how Microsoft security solutions can be grouped into categories. To expand on this, at the end of this blog the “Data Connector Table” describes several of Azure Sentinel’s built-in Microsoft data sources and maps out the respective sources to their detections (called analytics in Sentinel), use cases, and category of protection. While there are many more capabilities that Sentinel offers, this blog will focus on Data Sources and their relevant detections. The list provides a summary so that a SOC can prioritize what data they need to ingest into Sentinel as their SIEM. This blog will focus on a subset of major Microsoft data sources that can be easily leveraged in Azure Sentinel and should not be viewed as an exhaustive list. For more information on available data connectors please refer to the Azure Sentinel: Syslog, CEF, Logstash and other 3rd party connectors grand list.
Figure: Integrated Toolset
From Data Ingestion to Detection
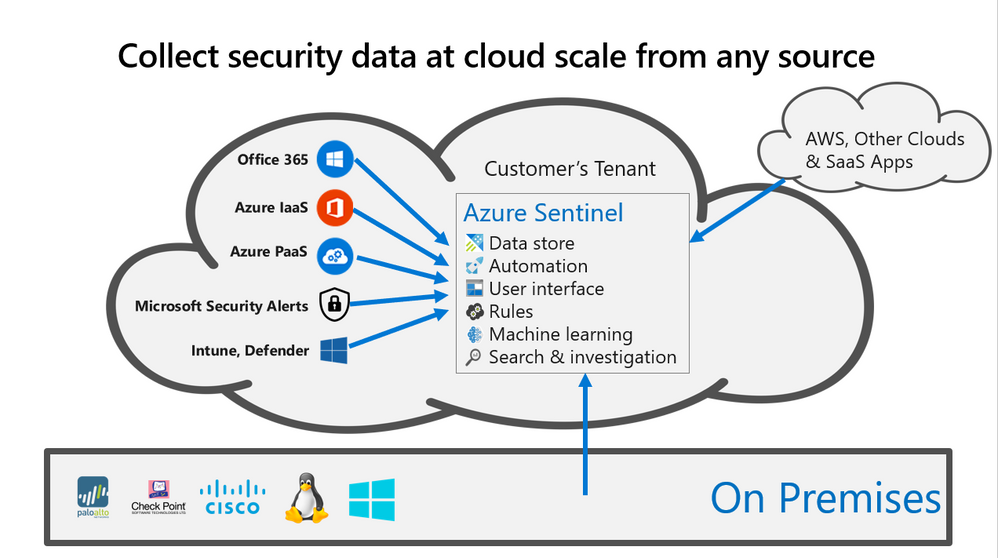
By connecting relevant security logs into Sentinel, organizations can consolidate all their relevant data into one place. Utilizing Sentinel’s built-in Machine Learning and other detections, SOCs can analyze their logs with ease and determine what truly malicious activity has taken or (more importantly) is currently taking place.
Wherever your logs are located; you can bring them into Sentinel and benefit from Sentinel’s centralized incident management view and built-in intelligence, as well as leverage Security Playbooks to implement orchestration and automation to react to emerging threats. In the figure below (“Data Collection”) one can see how Sentinel allows for the ingestion of data across Azure, other clouds, and OnPrem to fuel its ML and built-in rules.
Figure: Data Collection
There are many built-in data connectors and methods to get data into Sentinel that are not covered in this blog, but the below table can be leveraged for understanding the built-in data connectors for Microsoft technologies. Listed in the table are links to related documents that provide a deeper dive into the respective Data Connector, a list of the relevant Sentinel built-in analytics to determine observed threats, and a category of security coverage that the data source provides.
This list serves as a partial guide to a handful of major Microsoft data sources that can be easily and quickly ingested into Sentinel to help SOCs adopt Sentinel and see value quickly. However, it is important to note that Sentinel provides additional data source coverage, machine learning, and fusion alerts that span across multiple data sources. While this blog focuses on built-in single-source Sentinel detections and receiving detections from their respective data sources, there are more use cases to consider on cross-source detection, investigating alerts, visualizing data with workbooks, and hunting.
Data Connector Table
Note: This is an expanding list
Data Connector | Description | Relevant Links | Category | Free/Paid |
Azure Active Directory | The Azure Active Directory (Azure AD) enterprise identity service provides single sign-on and multi-factor authentication to help protect users from 99.9 percent of cybersecurity attacks. |
| Identity Devices | Paid |
Azure Active Directory Identity Protection | Detect threats to user’s identity such as compromised Azure Active Directory credentials or when someone other than the account owner is attempting to sign in using their identity | Identity | Paid | |
Azure Activity | Subscription level oversight and event tracking. This includes a record of ‘write’ changes that occur in Azure. This shows for each PUT, POST, and DELETE: who was involved, when the change happened, and what did the user change. | Identity Infrastructure | Free | |
Azure Advanced Threat Protection (Alerts) | Domain Controller based anomaly detection on User/Entity Behavior Analytics, malicious insider action, lateral movements, domain dominance, and compromised identities for OnPrem and Cloud scenarios. | Identity | Free | |
Azure Firewall | Protection for Azure Virtual Network resources. Threat intelligence-based filtering to alert and deny traffic from/to known malicious IP addresses and domains. | Network Infrastructure | Paid | |
Azure Information Protection (Alerts) | Oversight and protection in the cloud and OnPrem for advanced data related attacks and insider threats. Unusual data access attempts and custom alerts based on data. | Data Apps | Free | |
Azure Security Center (Alerts) | In addition to its Security Posture Management features; Security Center’s threat protection enables you to detect and prevent threats at the IaaS & PaaS layers (Azure Resources), as well as non-Azure servers. |
| Infrastructure Azure Resources IaaS & PaaS (see detections for full list) | Free |
Azure Security Center for IoT (alerts) | Built-in and custom detections on you IoT Hub and or IoT devices potentially malicious activity. | IoT Identity Devices Endpoints | Free | |
Azure Web Application Firewall | Protection from common web vulnerabilities such as SQL injection and cross-site scripting. Monitor your web applications using custom rules, rule groups, and Sentinel detections based on the diagnostics of Application Gateways to suit your requirements and eliminate false positives. | Infrastructure Identity | Paid | |
Domain Name Server | Oversight on malicious domain names, stale resource records, talkative DNS clients, and DNS registration failures. | Microsoft DNS | Paid | |
Microsoft Cloud App Security (Alerts and Shadow IT Report) | Raise alerts on user or file behavior anomalies in cloud apps leveraging API connectors. Detections are grouped into risk factors: risky IP address, login failures, admin activity, inactive accounts, location, impossible travel, device and user agent, and activity rate
| Apps Data Identity (see detections for full list) | Free | |
Microsoft Defender Advanced Threat Protection (Alerts) | Detection of attacker tools, techniques, and procedures, behavioral signals through the embedded endpoint behavioral sensors. Threat recognition leverages big-data, machine-learning, and Microsoft optics across Windows, other cloud products (Office 365), and online assets. | Endpoints Infrastructure Devices | Free | |
Office 365 (Office Activity: Exchange & SharePoint) | Custom and built-in detections on user, admin, system, and policy actions and events from ingestion of the OfficeActivity Log (Exchange Online and SharePoint raw audit logs). | Apps | Free | |
Windows Security Events | Streaming of windows security and AppLocker events to protect your Windows servers and workstations (physical and virtual). This can include full user audit trails, security group changes, key domain controller Kerberos operations, and more. | Identity Infrastructure | Paid |
To prioritize the onboarding of critical data connectors please view ‘Part 3: Alert and Log Ingestion’ of the Microsoft security architecture recommendations
For data sources missing from the above table, please refer to the following links:
- 3rd party sources: Syslog, CEF and other 3rd party connectors grand list
- Microsoft sources: Collecting logs from Microsoft Services and Applications
- The Log Analytics agent (a.k.a OMS Agent): Collecting telemetry from on-prem and IaaS server using the Log Analytics agent
Next Steps
Setting up a Data Connector in Sentinel can be as easy as two-clicks, but it is important to make sure that after you have setup a Data Connector that you enable the applicable built-in analytics to start detecting threats to your environment. By enabling an analytic, Sentinel will monitor the connected logs for that specific threat and will create an alert. Sentinel will then review other contextual events and potentially create an incident for investigation. Using the table above, you can navigate the Sentinel GitHub community and other relevant documents to view Sentinel’s detections per each respective data table. Additionally, you can view and enable each data sources analytics by navigating to the respective Data Connector page as seen in the graphic below.
Figure: Built-in single-source analytic rules per data source in Azure Sentinel
To reduce alert fatigue and understand how one attack spanned across multiple data sources check out Sentinel’s fusion based analytics. For additional detections that span across multiple data sources, please view the artifacts located in the Sentinel GitHub Community.
Related Blogs:
Identifying Threat Hunting opportunities in your data
Azure Sentinel correlation rules: the join KQL operator
Reviewers
Ofer Shezaf, Principal PM, Sentinel Engineering Team
Yuri Diogenes, Sr PM, Security CxE Team
Matt Lowe, PM2, Security CxE Team