This post has been republished via RSS; it originally appeared at: Core Infrastructure and Security Blog articles.
In my previous blog I addressed the issue of managing credentials in the code and presented two different alternatives to secure it. In this post, I will focus on Azure subscription security health and its challenge. I could summarize the subscription security health challenges as follows:
- New resources are deployed to Azure subscriptions all the time, especially if the company has many developers and DevOps working on the same subscription.
- Conducting subscription security health checks frequently for many subscriptions to make sure all the resources within the subscriptions follow the security best practices.
- For a big subscription, a manual check can be challenging.
Of course, there is an option to develop manual security checks as the scripts and run them on the subscription. However maintaining such a tool and updating it would be a nightmare, especially as the company adapts more resources type in the subscription.
Wouldn't it be nice if there was a tool that I could run against the subscription? And it could come back with a list of security issues and even give me the option to fix them automatically? Fortunately, this tool exists, and it is called a secure DevOps kit for Azure or AzSK.
What is Secure DevOps kit (AzSK)?
- Secure DevOps kit was an internal tool for Microsoft and was developed to help Microsoft internal teams to move to Azure quicker on more easily.
- It is an open-source tool and not an official product.
- Microsoft released this tool so it can share Azure cloud security best practices with the community.
- Both the code and documentation can be found on GitHub.
- It allows the option to customize these is scripts so they can match company needs
AzSK Focus Area:
- Secure the subscription: It can run global subscription health checks then it will come back with a list of improvements. Then I can go ahead and apply these improvements manually or automatically.
- Integrate Security into CICD: These security tests can be integrated into the company's continuous integration on continuous delivery pipelines.
- Enable Secure Development: It enables secure development. There is a visual extension that can be installed on the developers' machine. It adds security intelligence to the developers' IDE, so developers will be presented with the security best practices at the time of development.
- Continuous Assurance: It has the option to integrate these security tests with Azure automation, so this test can be run automatically as part of Azure automation process.
- Alerting & Monitoring: It will provide verbal’s alerting and monitoring data where users can implement it as part of Azure monitor.
- Security Telemetry in App Insights: It can write security telemetry information to an instance of Application Insights.
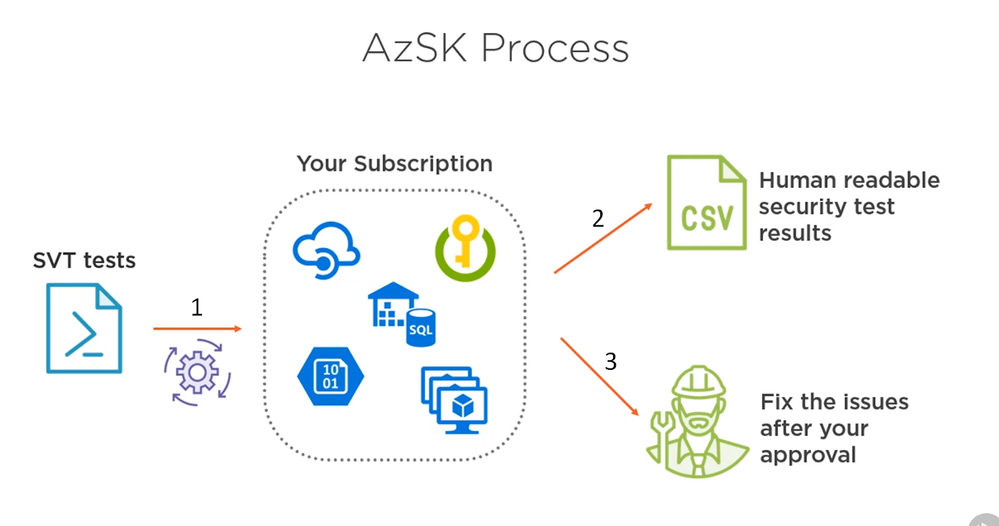
How does it work?
In the subscription, I can have different azure services like Azure SQL Server, virtual machines, storage accounts, Azure key, Walt Instances, API management instances ..etc, there are few options to user AzSK tool
- Running a few security tests against the subscription.
- Performing all these tests on come back with the test result. The test result is a CSV file.
- Automatically fix the issues for us.
NOTE: Not all the issues found can be fixed automatically. DevOps Admin will need to fix them manually.
Setting up AzSK
All the requirement and step by step instruction can be found here
I will need the following Pre-requisites:
- PowerShell 5.0 or higher.
- Windows OS
To Install the Secure DevOps Kit for Azure (AzSK) PS module:
Demo: Running Security Validation Tests (SVT) with AzSK
I am going to use the tool to scan on Azure subscription for Security Health. I will also use the tool to scan a resource group for security health. The resource group will have the following
- Storage Account
- Azure SQL Database.
- Virtual Machine
- Azure Key Vault
- Azure Cosmos DB
The following the azSK command will run security scans against the subscription.
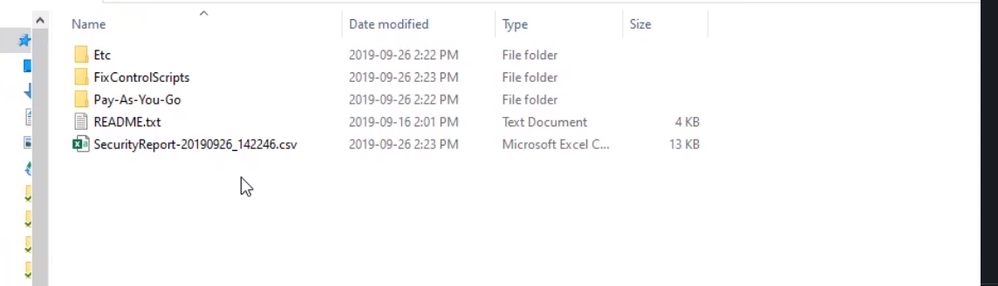
Once the command is finished it will open an explorer window and show the result.
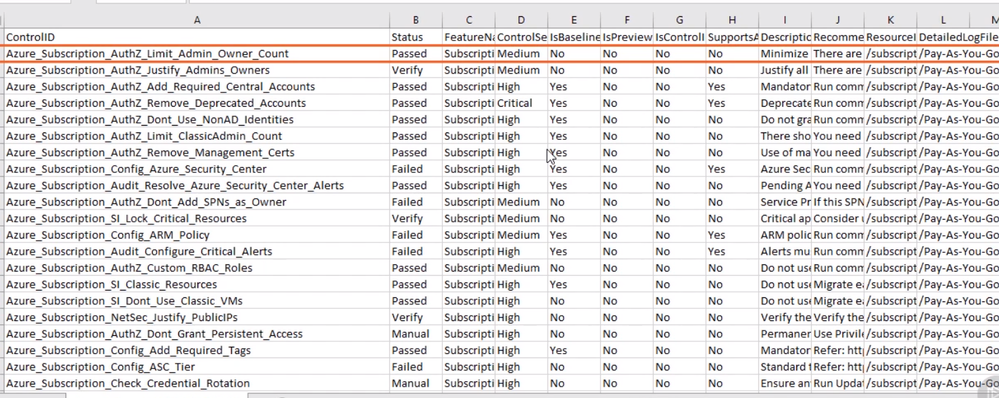
The SecurityReport file will show a list of the subscription level test, which were executed, and its result. For example, there is a test to make sure the admin owners off.
Also, since I used “GenerateFixScript” flag, there is a folder calls “FixControlScript” and if I opened this folder I can see Powershell fix script
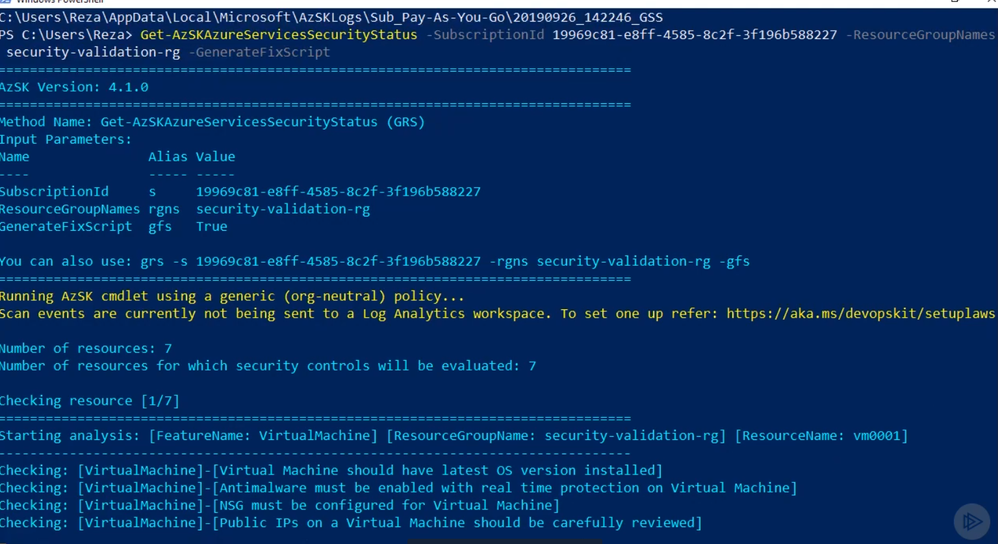
In this second test, I will run the AzSK command against a resource group
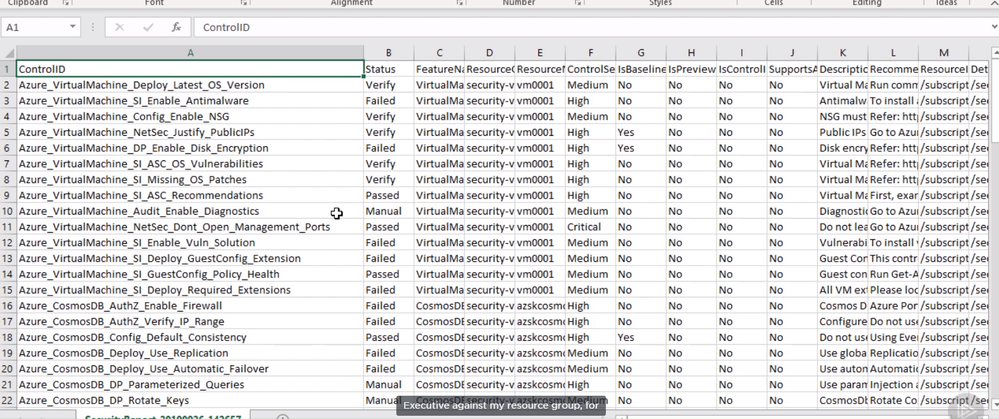
Like the last test, AzSK command will open the result folder where I can find the security scan result report
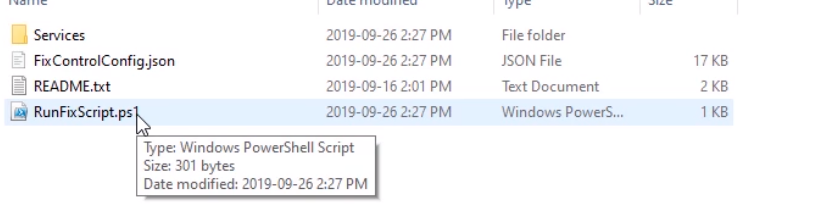
Also, there will be a “FixControlScript” folder where I will find the “RunFixScript” file
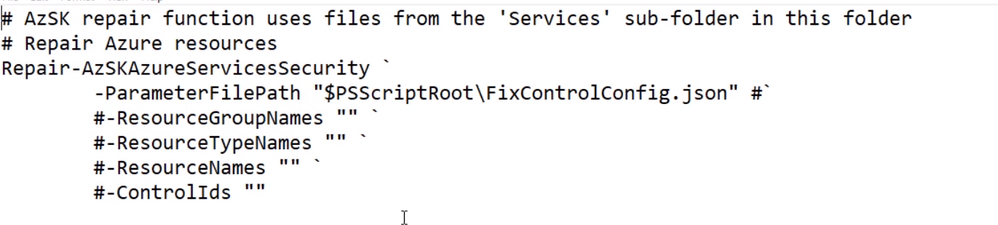
If I edit the file I could see the script and how it will attempt to fix the problem
Also if I checked the result folder again I could see a “security-validation-rg” folder that contains logs for each azure service that exists under the resource group. The log will contain information about the test and results that executed against the resource.
Summary
AzSK enables us to run security health checks against our subscriptions or resource groups. The tool will give a report and also an option to automatically fix issues that are found. In our next blog, I will discuss Azure sentinel.