This post has been republished via RSS; it originally appeared at: ITOps Talk Blog articles.
Hello folks,
Following my recording with Shayoni Seth (Senior Program Manager on the Azure Monitor Agent team) regarding the use and deployment of the upcoming Azure Monitor Agent (AMA) currently in preview. We established that there are 2 key parts of the new agent:
- The Data Collection Rule
- The Agent deployment.
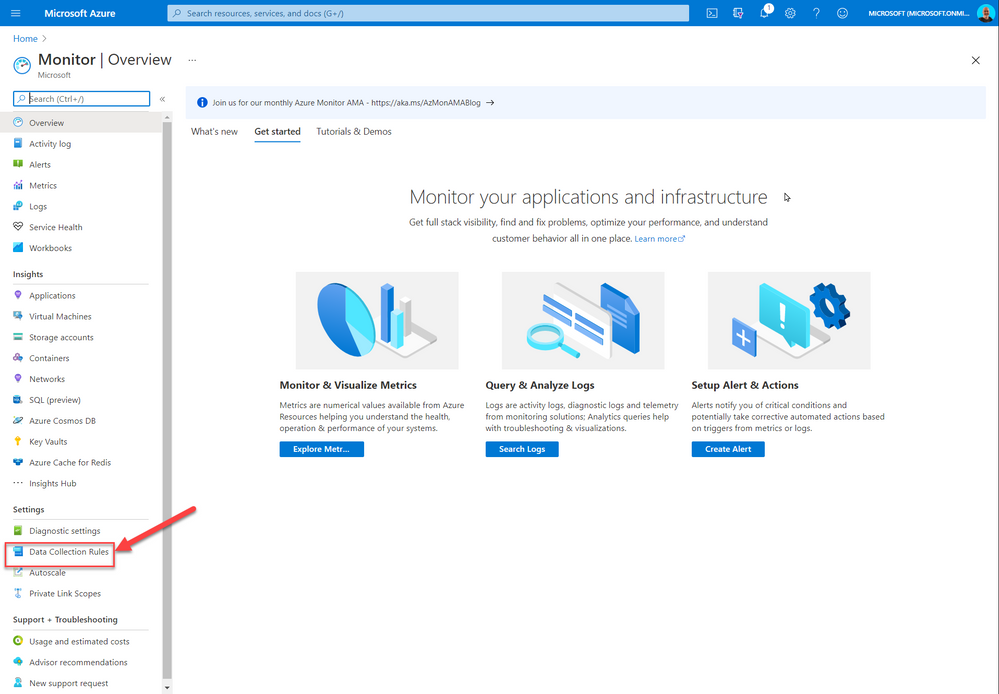
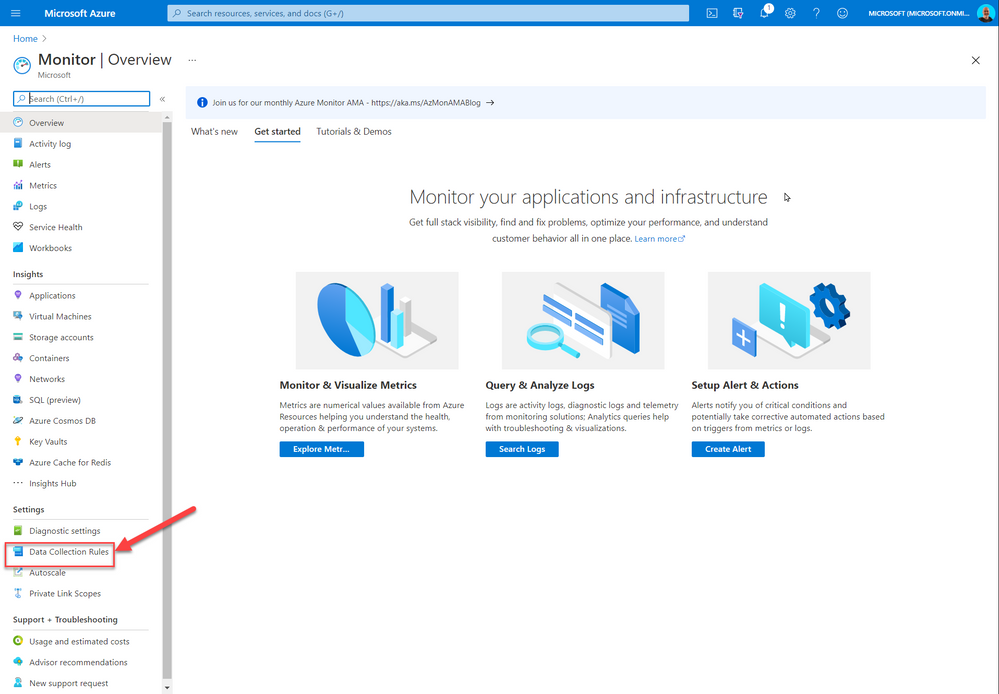
So, if you are testing this new Azure Monitor Agent and you want to avoid having to deploy the agent to each new VM individually in the portal, by navigating to Azure Monitor and selecting the Data Collection Rules (DCR)
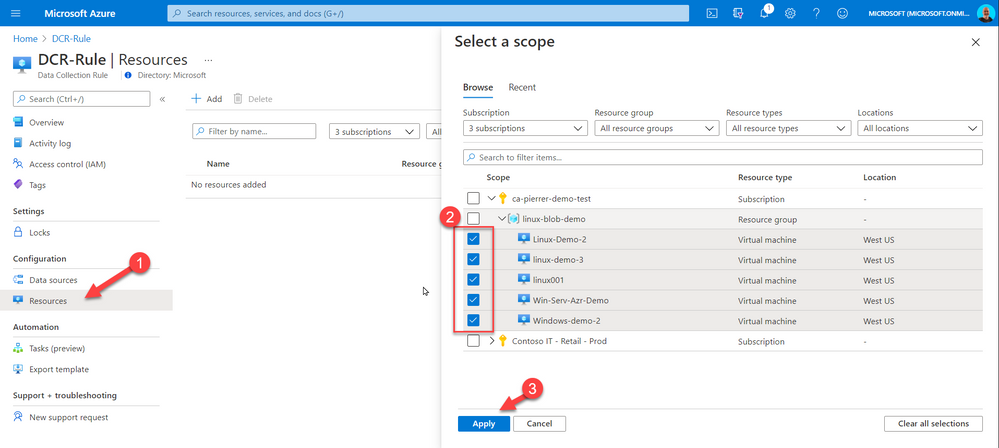
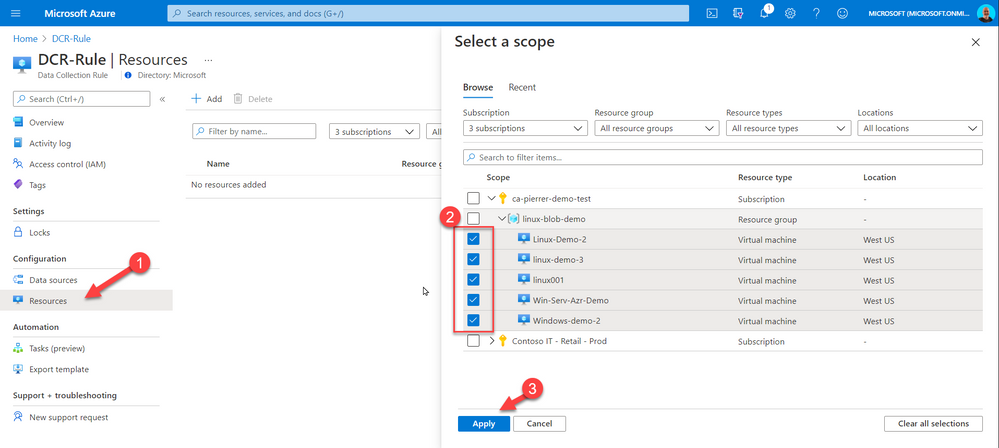
And in the DCR menu select Resources, select the resources you need the agent deployed to, and associated with the DCR rule you created.
You can create an Azure Policy that will continuously evaluate if new VMs have the agent and the association with the DCR. If the resources are not compliant with the policy, a remediation task with force the agent extension to be installed and will create the association.
In Azure Policy, create a new Definition that validates and deploys if not present the agent and the assignment.
My policy for Windows is below:
{
"properties": {
"displayName": "Deploy new Azure Monitor Agent to Windows VMs and tie to DCR",
"policyType": "Custom",
"mode": "Indexed",
"description": "Deploy new Azure Monitor Agent to Windows VMs and tie to DCR",
"metadata": {
"version": "1.0.1",
"category": "Monitoring"
},
"parameters": {
"DCRResourceID": {
"type": "String",
"metadata": {
"displayName": "DCR resource ID",
"description": "Resource ID of the DCR that the VMs in scope should point to."
}
}
},
"policyRule": {
"if": {
"allOf": [
{
"field": "type",
"equals": "Microsoft.Compute/virtualMachines"
},
{
"anyOf": [
{
"allOf": [
{
"field": "Microsoft.Compute/imagePublisher",
"equals": "MicrosoftWindowsServer"
},
{
"field": "Microsoft.Compute/imageOffer",
"equals": "WindowsServer"
},
{
"field": "Microsoft.Compute/imageSKU",
"in": [
"2008-R2-SP1",
"2008-R2-SP1-smalldisk",
"2012-Datacenter",
"2012-Datacenter-smalldisk",
"2012-R2-Datacenter",
"2012-R2-Datacenter-smalldisk",
"2016-Datacenter",
"2016-Datacenter-Server-Core",
"2016-Datacenter-Server-Core-smalldisk",
"2016-Datacenter-smalldisk",
"2016-Datacenter-with-Containers",
"2016-Datacenter-with-RDSH",
"2019-Datacenter",
"2019-Datacenter-Core",
"2019-Datacenter-Core-smalldisk",
"2019-Datacenter-Core-with-Containers",
"2019-Datacenter-Core-with-Containers-smalldisk",
"2019-Datacenter-smalldisk",
"2019-Datacenter-with-Containers",
"2019-Datacenter-with-Containers-smalldisk",
"2019-Datacenter-zhcn"
]
}
]
},
{
"allOf": [
{
"field": "Microsoft.Compute/imagePublisher",
"equals": "MicrosoftWindowsServer"
},
{
"field": "Microsoft.Compute/imageOffer",
"equals": "WindowsServerSemiAnnual"
},
{
"field": "Microsoft.Compute/imageSKU",
"in": [
"Datacenter-Core-1709-smalldisk",
"Datacenter-Core-1709-with-Containers-smalldisk",
"Datacenter-Core-1803-with-Containers-smalldisk"
]
}
]
},
{
"allOf": [
{
"field": "Microsoft.Compute/imagePublisher",
"equals": "MicrosoftWindowsServerHPCPack"
},
{
"field": "Microsoft.Compute/imageOffer",
"equals": "WindowsServerHPCPack"
}
]
},
{
"allOf": [
{
"field": "Microsoft.Compute/imagePublisher",
"equals": "MicrosoftSQLServer"
},
{
"anyOf": [
{
"field": "Microsoft.Compute/imageOffer",
"like": "*-WS2016"
},
{
"field": "Microsoft.Compute/imageOffer",
"like": "*-WS2016-BYOL"
},
{
"field": "Microsoft.Compute/imageOffer",
"like": "*-WS2012R2"
},
{
"field": "Microsoft.Compute/imageOffer",
"like": "*-WS2012R2-BYOL"
}
]
}
]
},
{
"allOf": [
{
"field": "Microsoft.Compute/imagePublisher",
"equals": "MicrosoftRServer"
},
{
"field": "Microsoft.Compute/imageOffer",
"equals": "MLServer-WS2016"
}
]
},
{
"allOf": [
{
"field": "Microsoft.Compute/imagePublisher",
"equals": "MicrosoftVisualStudio"
},
{
"field": "Microsoft.Compute/imageOffer",
"in": [
"VisualStudio",
"Windows"
]
}
]
},
{
"allOf": [
{
"field": "Microsoft.Compute/imagePublisher",
"equals": "MicrosoftDynamicsAX"
},
{
"field": "Microsoft.Compute/imageOffer",
"equals": "Dynamics"
},
{
"field": "Microsoft.Compute/imageSKU",
"equals": "Pre-Req-AX7-Onebox-U8"
}
]
},
{
"allOf": [
{
"field": "Microsoft.Compute/imagePublisher",
"equals": "microsoft-ads"
},
{
"field": "Microsoft.Compute/imageOffer",
"equals": "windows-data-science-vm"
}
]
},
{
"allOf": [
{
"field": "Microsoft.Compute/imagePublisher",
"equals": "MicrosoftWindowsDesktop"
},
{
"field": "Microsoft.Compute/imageOffer",
"equals": "Windows-10"
}
]
}
]
}
]
},
"then": {
"effect": "deployIfNotExists",
"details": {
"type": "Microsoft.Insights/dataCollectionRuleAssociations",
"name": "association1",
"roleDefinitionIds": [
"/providers/microsoft.authorization/roleDefinitions/92aaf0da-9dab-42b6-94a3-d43ce8d16293"
],
"type": "Microsoft.Compute/virtualMachines/extensions",
"existenceCondition": {
"allOf": [
{
"field": "Microsoft.Compute/virtualMachines/extensions/type",
"equals": "AzureMonitorWindowsAgent"
},
{
"field": "Microsoft.Compute/virtualMachines/extensions/publisher",
"equals": "Microsoft.Azure.Monitor"
},
{
"field": "Microsoft.Compute/virtualMachines/extensions/provisioningState",
"equals": "Succeeded"
}
]
},
"deployment": {
"properties": {
"mode": "incremental",
"template": {
"$schema": "http://schema.management.azure.com/schemas/2015-01-01/deploymentTemplate.json#",
"contentVersion": "1.0.0.0",
"parameters": {
"resourceName": {
"type": "string"
},
"vmName": {
"type": "string"
},
"location": {
"type": "string"
},
"DCRResourceID": {
"type": "string"
}
},
"variables": {
"vmExtensionName": "AzureMonitorWindowsAgent",
"vmExtensionPublisher": "Microsoft.Azure.Monitor",
"vmExtensionType": "AzureMonitorWindowsAgent",
"vmExtensionTypeHandlerVersion": "1.0"
},
"resources": [
{
"name": "[concat(parameters('vmName'), '/', variables('vmExtensionName'))]",
"type": "Microsoft.Compute/virtualMachines/extensions",
"location": "[parameters('location')]",
"apiVersion": "2018-06-01",
"properties": {
"publisher": "[variables('vmExtensionPublisher')]",
"type": "[variables('vmExtensionType')]",
"typeHandlerVersion": "[variables('vmExtensionTypeHandlerVersion')]",
"autoUpgradeMinorVersion": true
}
},
{
"name": "[concat(parameters('resourceName'), '/', 'Microsoft.Insights/', 'association1')]",
"type": "Microsoft.Compute/virtualMachines/providers/dataCollectionRuleAssociations",
"location": "[parameters('location')]",
"apiVersion": "2019-11-01-preview",
"properties": {
"dataCollectionRuleId": "[parameters('DCRResourceID')]"
}
}
],
"outputs": {
"policy": {
"type": "string",
"value": "[concat('Enabled for VM', ': ', parameters('resourceName'))]"
}
}
},
"parameters": {
"resourceName": {
"value": "[field('name')]"
},
"location": {
"value": "[field('location')]"
},
"vmName": {
"value": "[field('name')]"
},
"DCRResourceID": {
"value": "[parameters('DCRResourceID')]"
}
}
}
}
}
}
}
}
}
And once you have the definition created you will need to assign it to your environment. When assigning it you will require the DCR resource ID. This can be found in the JSON section of the DCR Overview.


The rest of the policy assignment is the same as any other policy. Just don’t forget to check the box to create the remediation task.
That’s it. From now on, any new VMs deployed in scope of the policy will get the Agent and will be associated with the DCR rule you selected. Of course, you can have multiple DCR and corresponding policies for different VM types or workload definitions.
I hope this helps!
Cheers!