This post has been republished via RSS; it originally appeared at: Core Infrastructure and Security Blog articles.
Hello dear readers! My name is Daniel Ribeiro and I am a Customer Engineer working with Microsoft Mission Critical Team (SfMC).
The Problem
A customer of mine recently reported that when deploying a container using the Azure Web App, the Azure Container Registry (ACR) credentials were exposed in the environment variables of the web app.
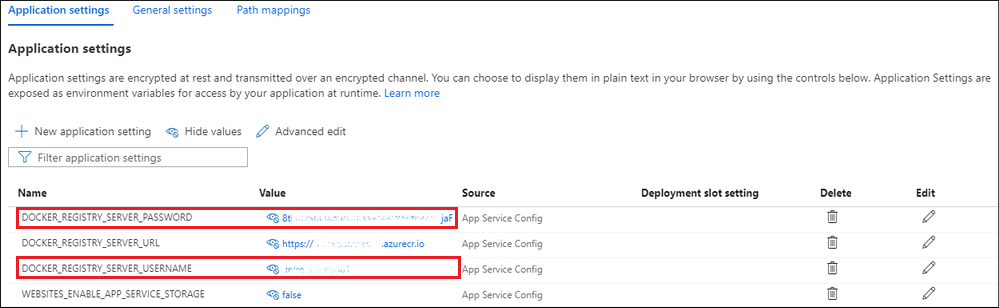
Take a look at the image below! As we can see, the ACR user and password are stored as environment variables.
But then you can think: just enable managed identity for the web app, grant permissions on the ACR and remove the credentials from the variables!
It makes perfect sense, however, currently, Azure Web App for Containers can't use their managed identity to authenticate with Azure Container Registry when pulling a container image to deploy the container resource itself.
The Solution
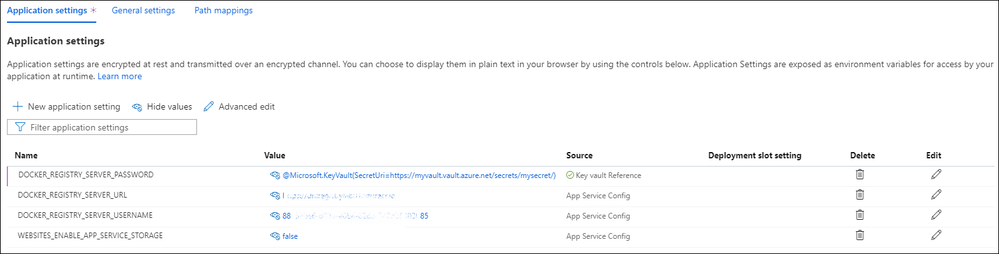
To solve this issue and prevent ACR credentials from being exposed in Web App variables, we created a Service Principal (SP), assigned SP to ACR and stored SP credentials in Azure Key Vault.
How to set up Web App to use SP during authentication in ACR?
- Create a Service Principal:
az ad sp create-for-rbac --name AppServicePullACR NOTE: The command above returns a Client ID and Secret, save both of them.
- Give Web App identity (Service Principal) access to pull from ACR:
az role assignment create --assignee $ServicePrincipalClientID --scope /subscriptions/$YourSubID/resourceGroups/$RegistryResourceGroup/providers/Microsoft.ContainerRegistry /registries/$RegistryName --role "AcrPull" - Save SP credentials on Azure Key Vault:
- Create a key vault by following the Key Vault quickstart.
-
Create a system-assigned managed identity for your web app.
- Create an access policy in Key Vault for the application identity you created earlier.
- Enable the "Get" secret permission on this policy.
- Save Service Principal password (secret) in the Key Vault as a Secret.
- Change the variable "DOCKER_REGISTRY_SERVER_PASSWORD" on the Web App and point to the Key Vault using the following syntax:
KeyVault(SecretUri=https://myvault.vault.azure.net/secrets/mysecret/) Also change the variable "DOCKER_REGISTRY_SERVER_USERNAME" and point to the Service Principal Client ID. - Disable the Admin account on Azure Container Registry:
az acr update -n <acrName> --admin-enabled false
Conclusion
As we saw in this article, managed identity to pull images from ACR is not yet available for Azure App Services, so using Service Principal can help increase the security of the environment and avoid exposing credentials in the web app variables.
Thank you for reading! I hope this can be useful.
Disclaimer The sample scripts are not supported under any Microsoft standard support program or service. The sample scripts are provided AS IS without warranty of any kind. Microsoft further disclaims all implied warranties including, without limitation, any implied warranties of merchantability or of fitness for a particular purpose. The entire risk arising out of the use or performance of the sample scripts and documentation remains with you. In no event shall Microsoft, its authors, or anyone else involved in the creation, production, or delivery of the scripts be liable for any damages whatsoever (including, without limitation, damages for loss of business profits, business interruption, loss of business information, or other pecuniary loss) arising out of the use of or inability to use the sample scripts or documentation, even if Microsoft has been advised of the possibility of such damages.