This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Introduction
The purpose of this article is to provide specific guidelines on how to perform a proof of concept (PoC) for Azure Defender for App Service. This article is part a series of articles, called The Azure Defender PoC Series, each providing specific guidelines on how to perform a proof of concept (PoC) for a specific Azure Defender plan. For a more holistic approach where you need to validate Azure Security Center and Azure Defender, please read the How to Effectively Perform an Azure Security Center PoC article.
Planning
This section highlights important considerations and availability information that you should be aware when planning for the PoC. Let’s start with outlining how to go about planning for an Azure Defender for App Service PoC.
Important Note: At the time of writing this article, Azure Defender for App Service is available solely in Commercial clouds (and it’s not available in Sovereign cloud, such as US Gov and Azure China).
The first step begins with a clear understanding of the benefits that enabling Azure Defender for App Services brings to your organization. Azure Defender for App Service provides dedicated security analytics that help you identify a variety of threats to your App Service resources, based on monitoring of various relevant parts. Additionally, enabling Azure Defender for App Service assesses your App Service resources and provides security recommendations with detailed best practice guidance on how to harden those resources. To learn more about Azure Defender for App Service, watch this video.
Now that we’ve touched briefly on the benefits that Azure Defender for App Services brings, let’s move on to the next step. The second step is identifying which use cases the PoC should cover. A common use case might be detecting attempts to run high privilege commands on a Windows App Service, or maybe detecting when known malicious IP addresses connect to your Azure App Service FTP interface. Azure Defender for App Service monitors for many threats and its alerts cover almost the complete MITRE ATT&CK tactics from pre-attack to command and control. It can even detect DNS dangling – any DNS entries remaining in your DNS registrar when an App Service website is decommissioned. To learn more about threats can Azure Defender for App Service detect, read this article.
Keep in mind that you have 30 days free trial of Azure Defender for App Service, which means that you should plan to execute your PoC prior to this expiration and based on the results keep it enabled or not. Please note that once enabling the Azure Defender for App Services plan (as well as any other Azure Defender plan), it will stay enabled until you disable it.
Preparation and Implementation
This section highlights the requirements that you should be aware before starting the PoC.
There are two main steps when preparing to enable Azure Defender for App Service.
- Determining if the App Service plan is supported
At the time of writing this article, all App Service plans are supported, except Azure Functions on the consumption plan.
Important Note: Please visit this article, for the latest information about availability and list of supported App Service plans.
- Enabling Azure Defender for App Service on your subscription
Security Center natively integrates with App Service, meaning the integration is done in the backend and you don’t need to deploy (and/or onboard) any agents or additional software package (see Figure 1). To learn how to enable Azure Defender, read this article.
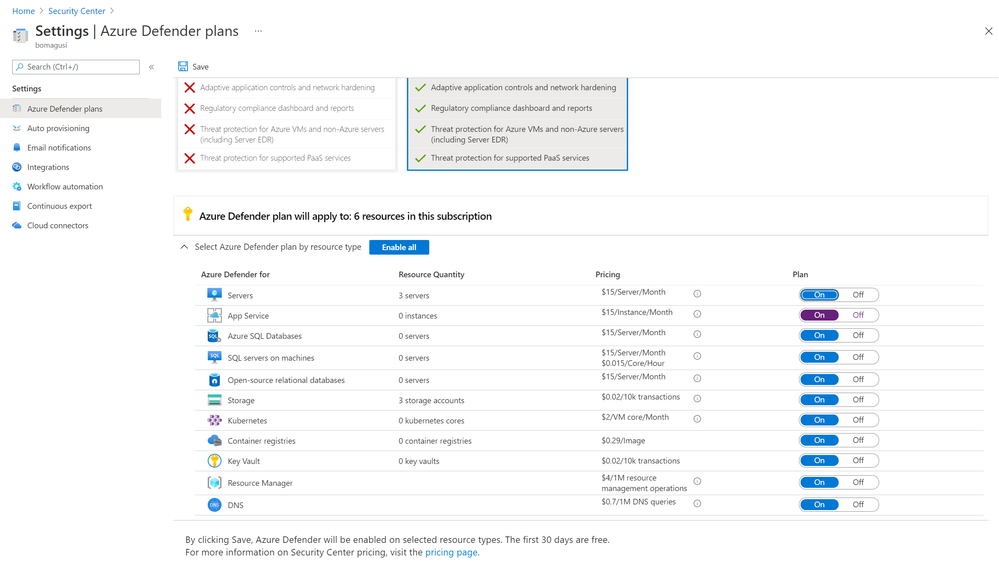
For the purpose of this PoC, it is important that you enable Azure Defender for App Service on the subscription(s) that you’ve identified for the PoC. Note: For the purposes of this PoC, it’s not mandatory to enable any other Azure Defender plans.
Validation
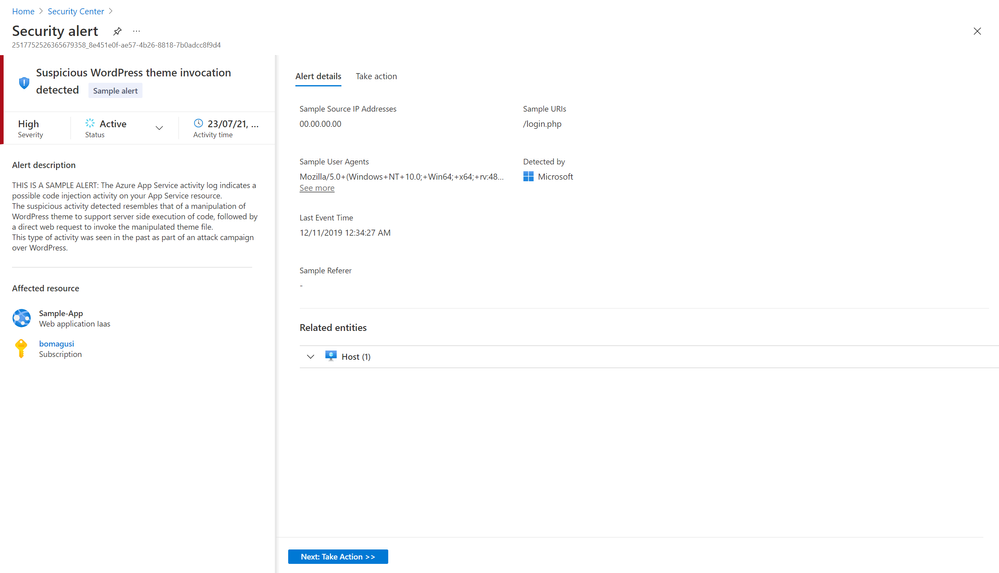
Once you’ve enabled Azure Defender for App Service on target subscription(s), you can validate it by simulating alerts relevant to the use cases that your PoC covers. You can also use the feature to validate Azure Defender for App Service alerts (as show in Figure 2.).
When validating the alerts, be sure to consult the full list of App Service alerts.
- You can also export Azure Defender security alerts to a SIEM (i.e. Azure Sentinel or 3rd party SIEM).
- Learn more about how to stream alerts to a SIEM, SOAR or ITSM.
- Learn more about how to investigate Azure Security Center alerts using Azure Sentinel.
Validating Azure Defender Alerts for App Service.
This article is all about providing specific guidelines on how to perform a proof of concept (PoC) for Azure Defender for App Service. For a more holistic approach where you need to validate Azure Security Center and Azure Defender, please read the How to Effectively Perform an Azure Security Center PoC article. As mentioned, Azure Defender for App Service provides dedicated security analytics to help you identify potential threats to your App Service resources. By the end of this PoC, you should be able to determine the value of Azure Defender for AppService and the importance to have this level of threat detection to your workloads. I hope you got real value out of this article and make sure to check out more articles from our Azure Defender for PoC series, which can be found on our official ASC Tech Community.
Reviewers:
@Yuri Diogenes, Principal PM
@Tomer Spivak, Senior PM
