This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
It is strongly recommended to use TLS v1.2 on app services by industry standards such as PCI DSS. New app services are created with TLS v1.2 enabled by default. Refer to below documents for more details.
- Secure a custom DNS with a TLS/SSL binding - Azure App Service | Microsoft Docs
- New App Service apps deployed with TLS 1.2 by default from June 30 | Azure updates | Microsoft Azure
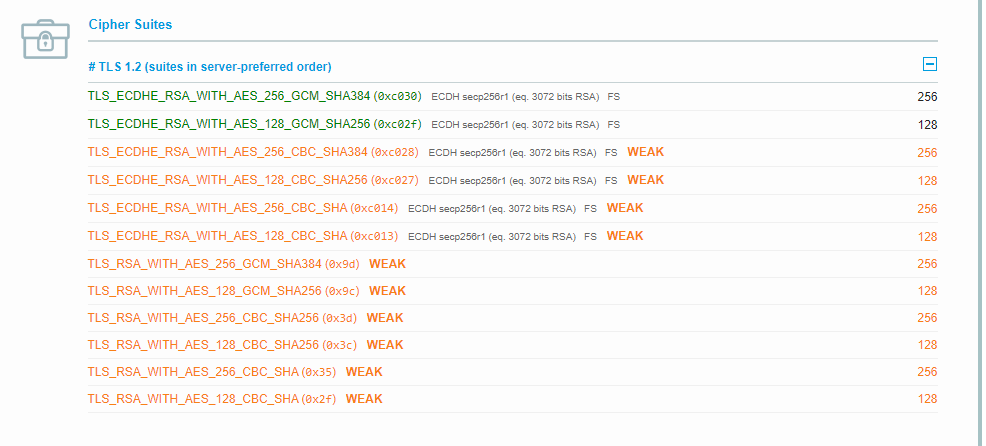
Sometimes, a user runs a security and vulnerability test on app service for their app enabled with TLS v1.2 using any of the third party tool available (for example SSL Labs) as per their organization guidance or compliance checklist. Some of these tools tag some of the cipher suites(especially CBC based cipher suites) as 'weak'. Mostly, the cipher suites are tagged 'weak' just based on the availability of the cipher suites on the app and not because of an actual vulnerabilities found. An example below:
There are reports that discusses why these CBC based cipher suites are being tagged weak. For example, you may refer to this document by SSL Labs. It mentions that "SSL Labs identifies cipher suites using CBC with orange color and with text WEAK. This change won’t have any effect on the grades, as it only means that SSL Labs discourages the use of CBC-based cipher suites further.". These are generic guidelines and these cipher suites would be advisable to disable when you are running your application on standalone server or VM/IaaS or on-premises machines.
Note that app services is a PaaS environment and its securities are constantly reviewed by the Product Group and the security team and the vulnerabilities are patched/fixed on the platform. The reason why these CBC cipher suites are being tagged 'weak' in general is because it could be vulnerable to certain attacks. However, if you test it for an app services on TLS v1.2, none of those associated vulnerabilities exists. They are already fixed on app services and none of those real security vulnerabilities exist on app services running on TLS v1.2. Also these 'weak' tagged cipher suites are lower in the order of the cipher suites presented by the app services. App service is PCI standard complaint.
You may also want to review the SSL/TLS best practices by SSL Labs. It does mention – “TLS v1.2 and v1.3 are both without known security issues.”. Also in the section Use Secure Cipher Suites it does recommend the secure cipher suites to start with:
If you are looking for disabling the cipher suites as compliance checklist(where just the existence of the cipher suites are concern), then it is recommend to add additional layer of security like WAF/application gateway or deploy to single tenant app service environment(ASE) which offers network isolation, higher scalability and security. In an ASE, you can change the default cipher suites using cluster settings. If you are running your app services on a multi-tenant app service plan(non-isolated plans) then it is not possible to modify the default cipher suites on the app services. In the multi-tenant app services, SSL is handled at the front-ends which are shared resources in a scale unit, the cipher suites are set as default and cannot be changed since there are other customers app services hosted in the same scale unit using these cipher suites.