This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
We are thrilled to announce new features that are available in Azure Automanage! Automanage is a service that automates daily server management tasks allowing customers to reduce their operational overhead.
Azure Automanage machine best practices supports the following new capabilities for both Windows and Linux Azure virtual machines and Arc-enabled server:
- Custom configuration profiles [Public Preview] allows you to create your own best practices profiles to support your IT requirements.
- Support for Azure Arc-enabled server VMs including on Azure Stack HCI [Public Preview]. Apply Automanage service to both Linux and Windows Server VMs on any Arc enabled server.
Azure Automanage for Windows Server, which enables unique innovation for new Windows Server virtual machines only on Azure. The enhancements are as follows:
-
Hotpatch [Public Preview]: Quickly deploy security updates without having to frequently reboot. Hotpatch will continue to be available in public preview.
-
SMB over QUIC [General Availability]: Securely access new file servers remotely over untrusted networks and without a VPN.
-
Extended network for Azure [General Availability]: Migrate Windows Server workloads to Azure, while preserving original IP addresses.
Automanage Azure machine best practices - custom profiles
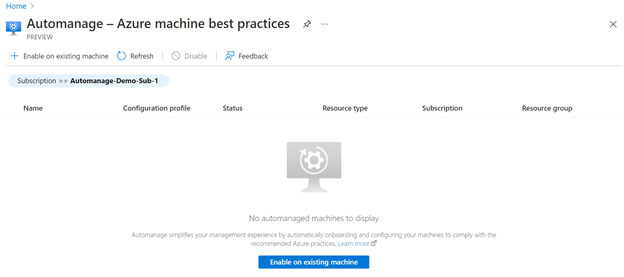
The first feature in Automanage is Azure machine best practices (Public Preview) which discovers, configures, and monitors best practices services throughout the lifetime of the Azure virtual machine or Arc-enabled server. Through Azure Automanage machine best practices, you take advantage of the default profiles that support production or dev/test machines. We have also added the support for you to create your own custom profiles by selecting the set of services and settings you want Automanage to configure and monitor for you. You can configure services like Azure Backup, Azure Security Center, Monitoring and more.
To check out Automanage custom profiles, start by browsing to the Automanage portal and click “Enable on existing machine”.
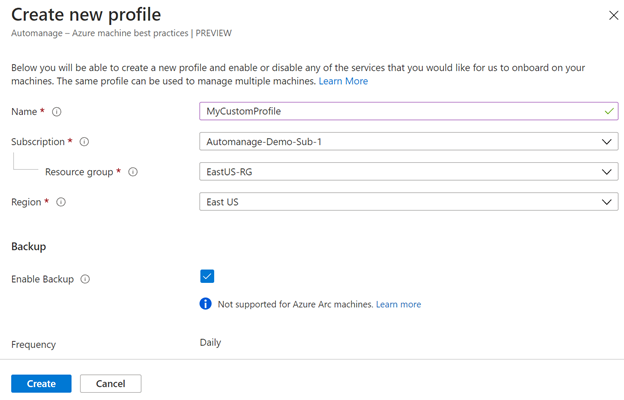
Next, choose to create a new custom profile in the Configuration profile selection option. Optionally, you could choose an existing configuration profile if you have created one previously.
Fill out the basic details of the custom profile, including Profile Name, Subscription, Resource Group, and Region. Afterwards, select the set of services and settings that you would like to use in this profile.
After you create your profile, select the Azure virtual machines and/or Arc-enabled servers that you want your custom profile applied to.
Once you have selected the machines, you can click Enable. Automanage has now configured your machines with the best practices services and settings that you selected when creating the best practices profile. You can click on the status to get the latest Automanage Status Report regarding your machines.
It is simple to onboard, and you can trust that Automanage will monitor the configuration of the machines with regards to the Azure services. For more information, check out Automanage Azure machine best practices custom profile support (Preview).
Automanage for Windows Server
As part of Azure Automanage, new scenarios and capabilities unlock with Automanage for Windows Server and its Azure IaaS virtual machines running Windows Server 2022 Datacenter: Azure Edition. The first three are Hotpatch (Preview), SMB over QUIC, and Extended Network for Azure. We update Windows Server Azure Edition machines annually with new features and we update Automanage for Windows Server continuously to make operating those features easy and reliable.
Hotpatch (preview)
Hotpatching is a new way to install security updates without requiring a reboot after installation. This means instead of rebooting at least twelve times a year for ‘Patch Tuesday’ updates, your Windows Server VM might restart as infrequently as four times a year for cumulative update re-baselining. Hotpatch-based security updates don’t just stop reboots, they’re smaller and install faster, giving CPU and memory resources back to a running VM more quickly.
Once you opt in to Automanage machine best practices and the hotpatch preview, and enable these during VM creation, Windows Server 2022: Datacenter Azure Edition configured as Server Core will automatically receive those patches and stop rebooting for updates except when rebaselined.
For more information on Automanage and Hotpatch, visit Hotpatch for new virtual machines (Preview).
SMB over QUIC
SMB over QUIC offers an "SMB VPN" for telecommuters, mobile device users, and branch offices, providing secure, reliable connectivity to edge file servers over untrusted networks like the Internet. QUIC is an IETF-standardized protocol used in HTTP/3, designed for maximum data protection with TLS 1.3 and requires encryption that no one can disable. SMB behaves normally within the QUIC tunnel, meaning the user experience doesn't change. SMB features like multichannel, signing, compression, continuous availability, and directory leasing work normally. SMB over QUIC is GA and available for VMs running Azure Edition, currently in Azure IaaS.
It doesn't stop there though: Automanage machine best practices for Windows Server also includes SMB over QUIC management. QUIC uses certificates to provide its encryption and organizations often struggle to maintain complex public key infrastructures. Automanage Azure machine best practices Automanage best practices ensure that certificates do not expire without warning and that SMB over QUIC stays enabled for maximum continuity of service.
Simply enable Automanage machine best practices for your VM either when creating your VM or afterwards from the Automanage menu. Automanage machine best practices will continuously monitor your VM, ensure the SMB over QUIC certificates are healthy and valid, and that SMB over QUIC stays available for your organization’s users and applications.
For more information, review SMB over QUIC and SMB over QUIC management with machine best practices.
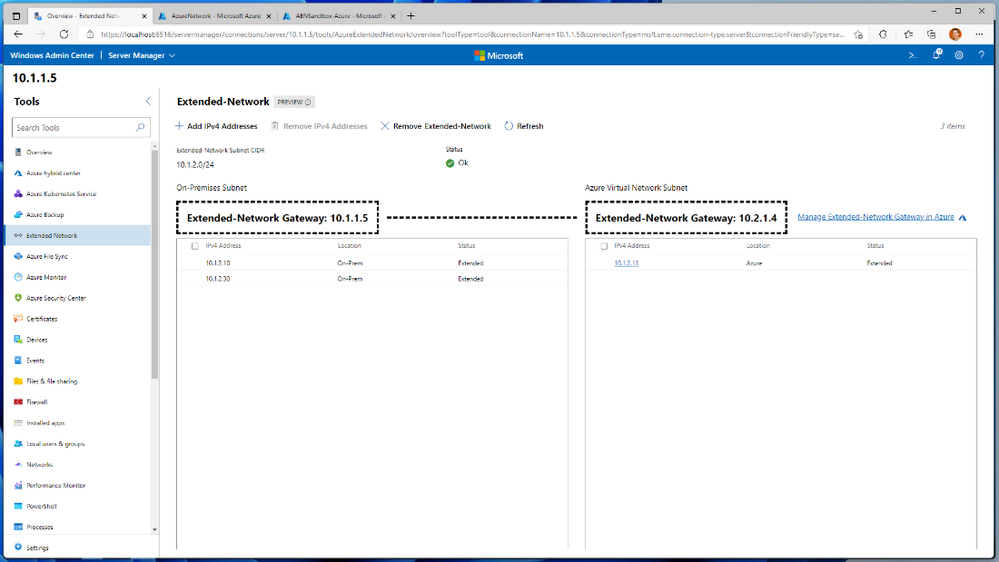
Extended Network
Extended Network for Azure enables stretching your organization’s on-premises networks into Azure so that migrated VMs can keep their IP addresses. Applications with hardcoded IP addresses – or where IT staff don’t know if someone has previously configured them using IP addresses – often block VM migrations to Azure. Extended Network uses an Azure Edition IaaS server and Datacenter edition server on-prem as virtual appliances to form a bidirectional VXLAN overlay over an Azure gateway connection (VPN or Express Route). With this you can be confident that any applications with hardcoded IP addresses instead of DNS names will still work when their VM migrates to Azure.
For more information, review Extended Network for Azure.
Conclusion
To keep learning, Azure Automanage has some exciting new capabilities:
- Get more detailed content on this topic with a custom Microsoft Learn collection
- Get started with Automanage best practices.
- Learn more about Azure Automanage for Windows Server.
To follow along at Ignite, watch our sessions on Azure Automanage and Windows Admin Center:
- Microsoft Into Focus: Infrastructure.
- Simplify IT server management through Azure Automanage.
- What’s new in Windows Admin Center.