This post has been republished via RSS; it originally appeared at: Microsoft Tech Community - Latest Blogs - .
We're changing the behavior of Office applications to enforce policies that block active content (macros, ActiveX, DDE, etc.) on Trusted Documents. Previously, active content was allowed to run in Trusted Documents even when an IT administrator had set a policy to block it. As part of ongoing Office security hardening, the IT administrator’s choice to block active content will now always take precedence over end-user set trusted documents. This change is released to Insiders in build 2110 and is planned to roll out to Current Channel in early February 2022. It is not planned to be backported to down-level versions.
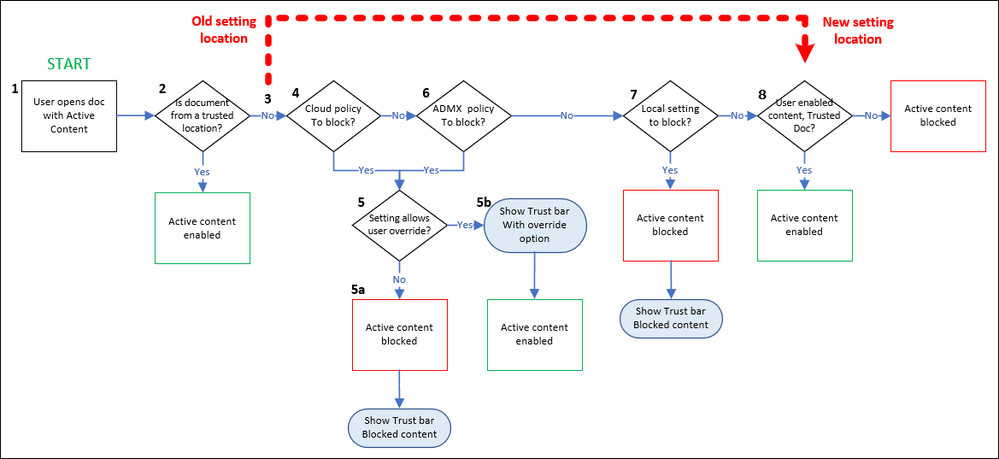
As you can see from the chart, the change in the evaluation flow allows admin-configured policies to always take precedence over user settings, which can help reduce the impact of attacks that use active content. This is important in the current threat landscape as active content attacks become more common.
End user experience
The expected impact is when a user opens a previously trusted document with active content that’s enabled. If there’s a policy set by their IT administrator or a Trust Center setting blocking the active content, the content will remain blocked. When this happens, we will display a business bar:
The Trusted document settings have changed KB article explaining the change in behavior, and links to Commercial guidance for IT Administrators: Manage active content in Office documents.
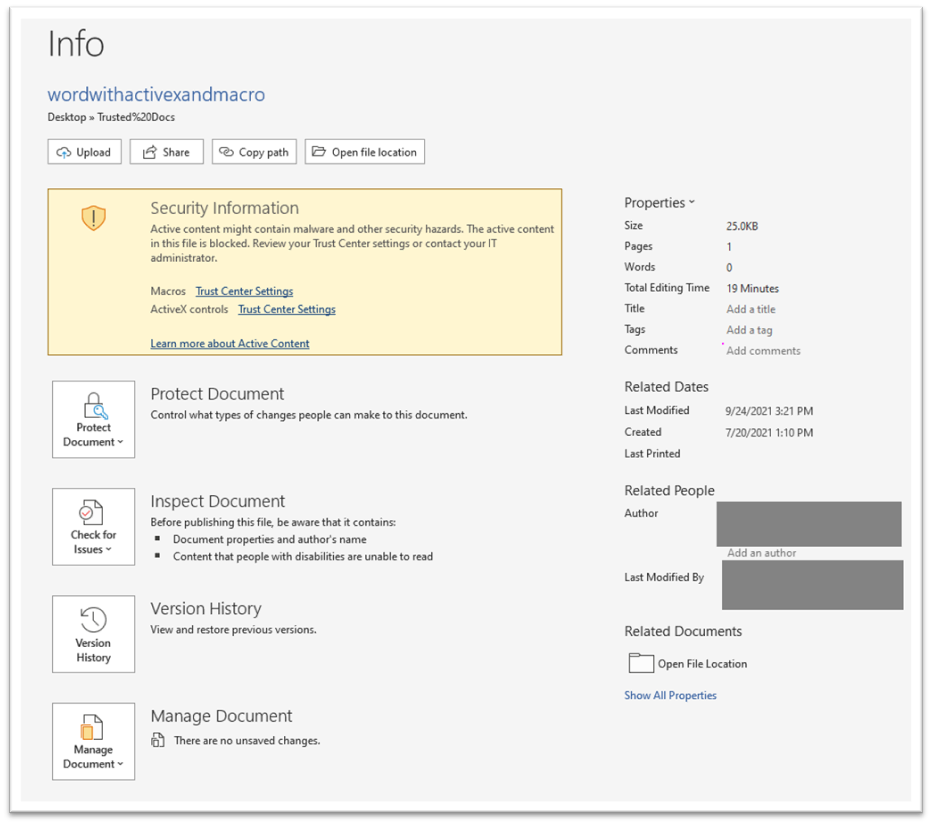
In addition, we’ve added a backstage slab for all documents containing active content displaying the trust scenario of the document:
This backstage notification particularly helps when the IT administrator has blocked all Trust bar notifications with the policy:
- Disable all Trust Bar notifications for security issues
For these impacted users with no business bar notification, they can select File/Info and see the backstage Security Information describing the trust scenario for the file.
IT administrator options:
It’s important for IT administrators and users to have tools to manage Office applications to balance security and productivity needs. Options available for this new trust workflow include:
- The Microsoft 365 Apps for enterprise Security Baselines are our recommendations for policy settings. Use these to guide your evaluation of active content settings.
- If your users don't need specific types of active content, your most secure option is to use policies to turn off user access to that active content, and allow exceptions as needed.
- Determine the appropriate trust behaviors for your end users, the following policies are available:
- Turn off Trusted Locations: Exceptions for security groups available.
- Turn off Trusted Documents: Exceptions for security groups available.
- Some policies controlling active content have settings that allow for user override. If you trust your users to make security decisions on their own, you can select these options, learn more.
Thank you,
Office Product Group – Security