This post has been republished via RSS; it originally appeared at: Microsoft Tech Community - Latest Blogs - .
The Microsoft Windows 365 provides all the benefits of Windows, without any of the traditional hardware limitations. It is the most optimized Microsoft 365 powered compute experience delivered from Azure and managed by Microsoft Endpoint Manager interfaces – portal and associated Graph APIs. It is Microsoft’s best expression of Windows and M365 and is always secure and up to date. The Windows 365 is SaaS virtual desktops/apps which is provisioned instantly for licensed users. It can be accessed anywhere from any device and can scale with a user’s changing compute needs. AD Joined Hybrid Windows 365 machines have connectivity to customer’s on-premises network. In order to align with this feature, Windows 365 service needs of sight into the customer’s virtual network in Azure subscription that must have the connectivity to customer on-premises network. Hybrid AD joined windows 365 solution will be replaced by Azure AD joined zero trust architecture in future market soon.
Prerequisites
To manage AD-joined Hybrid Windows 365 in Intune, be sure the following criteria are met:
- Azure subscription has been created for Windows 365 on-premises network connection.
- The Windows 365 service needs line of sight into the customer’s virtual network (Vnet on the Azure subscription) that has connectivity to the customer’s on-prem domain.
- Service account in on-premises domain should be created and synchronized to Azure AD.
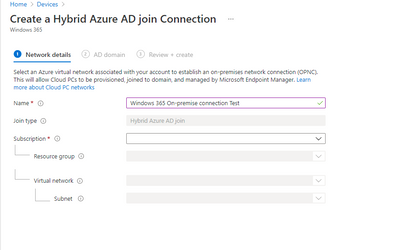
Create on-premises network connection
Navigate to Microsoft Endpoint Manager Admin Center, go to “Devices\Windows 365” blade, choose “On Premises network connections”, Click “Create connection”, Input the connection name, choose Azure subscription in prerequisites, create or choose an existing valid resource group, choose Virtual network in prerequisites, input AD domain full name and service account, after “review and create”, the connection will be created successfully.
If the connection is created successfully, it will be showing “Status” as “Checks successful”.
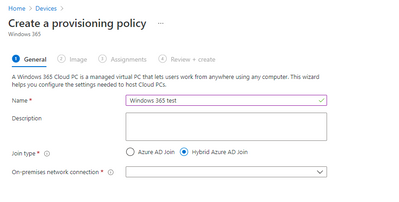
Create Provisioning policies
Provisioning policy defines which on-premises network connections and what version Windows OS the Windows 365 provisioning process will pick up. Navigate to “Devices\Windows 365” blade, go to “Provisioning policies” tab, click “Create policy”, input policy name, choose the correct On-premises network connection which was created in pervious steps.
After click “next”, choose image type as below:
The final step is to target this provisioning policy to a security group as assignments, the security group will be added with Windows 365 licensed user alias as members.
After the provisioning policy is created successfully, under “Provisioning policies” table, the provisioning policy should be listed.
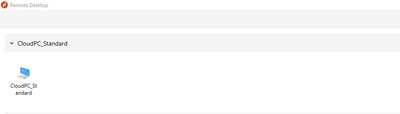
Now it is ready to provisiong Windows 365. If licensed user alias is added to above provisioning policy assignments security group in AAD, the provisioning process is kicked off right away without delaying. If there is no Azure deployments congestion, normally a Windows 365 can be provisioned successfully from 20-40 minutes. If the user alias is removed from the security group, the provisioned device will be in “Grace” period for 7 days and will be fully decommissioned after that. After the Windows 365 is provisioned successfully, the User will see the Windows 365 connection in remote desktop app as below:
The successfully provisioned Windows 365s show up in Windows 365 blade. These devices can be managed same as other physical devices in Intune.
Deploy apps and policies to Windows 365 from Intune
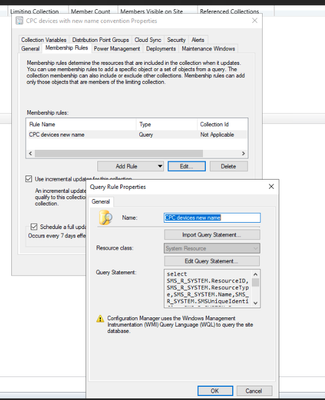
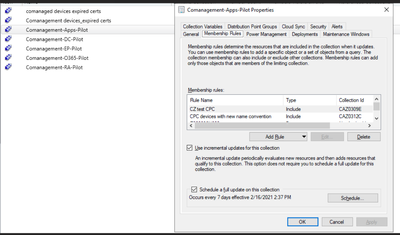
Since Windows 365s are all AD-joined Hybrid devices, Apps and policies deployment in Intune needs the deployment workload to be shifted from SCCM to Intune. Windows 365 doesn’t have identifier in AD domain attributes or properties, so we only can use device name convention to create configuration manager collection filter rule, then nest Windows 365 collections to co-management collections to shift policy and apps deployment to Intune:
Name convention query:
select SMS_R_SYSTEM.ResourceID,SMS_R_SYSTEM.ResourceType,SMS_R_SYSTEM.Name,SMS_R_SYSTEM.SMSUniqueIdentifier,SMS_R_SYSTEM.ResourceDomainORWorkgroup,SMS_R_SYSTEM.Client from SMS_R_System inner join SMS_Client_ComanagementState on SMS_Client_ComanagementState.ResourceId = SMS_R_System.ResourceId where SMS_Client_ComanagementState.Name like "CPC-%-%"