This post has been republished via RSS; it originally appeared at: Microsoft Tech Community - Latest Blogs - .
Transparent data encryption (TDE) in Azure SQL Database and Managed Instance helps protect against the threat of malicious offline activity by encrypting data at rest. Azure SQL TDE with Customer-Managed Key (CMK) enables Bring Your Own Key (BYOK) scenario for data protection at rest, and allows customer to have full control of the key lifecycle management.
The ability to use an RSA key stored in Azure Key Vault Managed HSM, for customer-managed TDE (TDE BYOK) in Azure SQL Database and Managed Instance is now generally available.
With this, along with the existing option of using Azure Key Vault (standard and premium tiers), customers now have the flexibility to use Managed HSMs for storing their encryption keys to protect their most confidential workloads in Azure SQL.
What is Managed HSM?
Managed HSM is a fully managed, highly available, single-tenant, standards-compliant cloud service that enables customers to safeguard cryptographic keys for their cloud applications, using FIPS (Federal Information Protection Standard) 140-2 Level 3 validated HSMs.
Managed HSM is built on Azure's confidential computing platform. Azure confidential computing protects the confidentiality and integrity of your data and code while it's processed in the public cloud.
Managed HSMs provide multiple benefits such as centralized key management, isolated access control (local RBAC), private endpoints, data residency, etc.
Quick steps to configure TDE BYOK on a SQL logical server using Managed HSM
- Create and activate a Managed HSM - follow instructions at create and activate a Managed HSM using Azure CLI
- Enable the system-assigned managed identity for the server (or alternatively, assign a user-assigned managed identity to the server and set it as the primary)
- Provide the server identity permissions on the Managed HSM - add the 'Managed HSM Crypto Service Encryption User' local RBAC role to the server identity on the Managed HSM. This enables the server to perform get, wrapKey, unwrapkey operations on the keys in the Managed HSM. Instructions for provisioning server access on Managed HSM
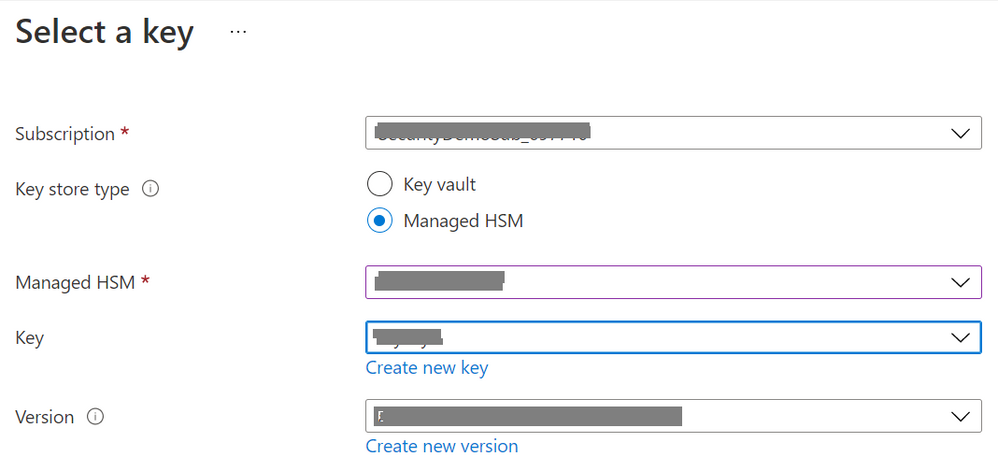
- Using Azure Portal, on the Transparent Data Encryption blade of the server, select “Managed HSM” as the Key Store Type from the customer-managed key picker and select the required key from the Managed HSM (to be used as TDE Protector on the server).
- Save the TDE settings – the server now gets configured with TDE with Customer-Managed Key using the encryption key from Managed HSM.
Learn More
- Azure Key Vault Managed HSM - https://docs.microsoft.com/en-us/azure/key-vault/managed-hsm/overview
- TDE BYOK in Azure SQL - https://docs.microsoft.com/en-us/azure/azure-sql/database/transparent-data-encryption-byok-overview
- Enable TDE with Customer-Managed Key in Azure SQL - https://docs.microsoft.com/en-us/azure/azure-sql/database/transparent-data-encryption-byok-configure?tabs=azure-powershell
With Managed HSM availability for customer-managed TDE in Azure SQL, customers can now bring their most sensitive workloads to Azure that require higher security (single-tenant, isolation, local RBAC), compliance (FIPS 140-2 Level 3 validated HSMs) and throughput for key management.